I Sent You An Email From Your Account
Where cybersecurity is concerned, a Trojan horse like “I Sent You An Email From Your Account” is synonymous for disaster. “I Sent You An Email From Your Account” belongs to the type of malware that’s the most widespread and most versatile type of dangerous and harmful programs.
Therefore, it is not a surprise why the web users tend to fret just by the thought that their computer might have been infected with a representative of the Trojan horse category. Cyber criminals, however, don’t miss a chance to benefit from users’ fear and come up with different scams and sketchy schemes that can earn them some quick money. One viral scam which has been spreading around the web lately is a new email Bitcoin scam that may be related to a Trojan called “I Sent You An Email From Your Account”.
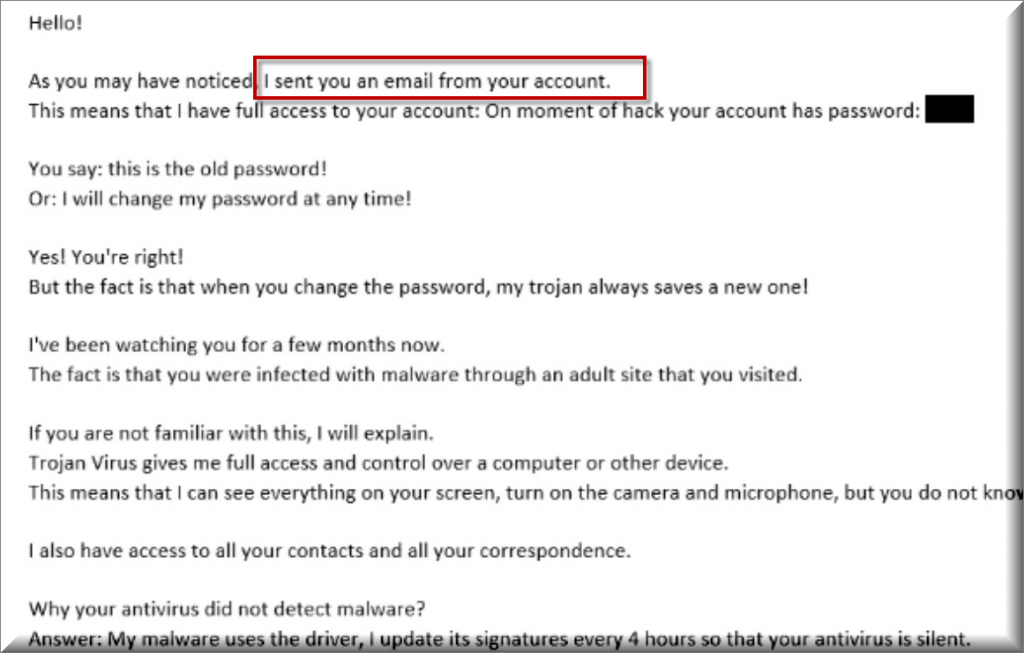
Many of our users reported to us about an ongoing email spam with the following message:
Subject: You password must be need changed
Hello!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account: On moment of hack your account has password: [removed] You say: this is the old password!
Or: I will change my password at any time!Yes! You’re right!
But the fact is that when you change the password, my trojan always saves a new one!I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks. I can also post access to all your e-mail correspondence and messengers that you use.If you want to prevent this, transfer the amount of $780 to my bitcoin address (if you do not know how to do this, write to Google: Buy Bitcoin).
My bitcoin addresses (BTC Wallets) are:
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.If I find that you have shared this message with someone else, the video will be immediately distributed.
Best wishes!
The victims of this new criminal extortion scheme have been reporting their email inbox getting spammed with some strange blackmail messages which state that their computers have been infected with hidden malware. It seems that the premise of these scam messages is similar – a self-proclaimed hacker warns the victims that they have gained control over their computer with the help of a hidden Trojan horse and that they intend to activate its malicious code if the user does not send certain amount of money to a given Bitcoin wallet. The blackmailer typically threatens that they will damage the PC and the data stored in it and/or make some sensitive personal information available to the public by uploading it online if the victim refuses to fulfill the ransom demands.
This simple blackmailing scheme seems to have tricked some web users so far and has made them send money to the anonymous criminals behind the scary message. Leading security professionals, however, warn that there is no reason to panic over such messages and give your money to the hackers. Even if there are some suspicious symptoms in your machine that may suggest a malware infection, paying the ransom is still not the answer to solving this issue.
That’s why, instead of rushing with the payment, we would suggest running a full scan of your system with reliable antivirus software. In many cases, such scam messages turn out to be just a bluff that aims to scare users. That’s why, if the scan does not show any actual infection, you don’t have a real reason to worry. If your security program detects some real malware, however, you should take immediate action towards dealing with it.
Most commonly, spam messages like the ones that we described above can be linked to the distribution of Trojan-based viruses such as “I Sent You An Email From Your Account” Bitcoin Email. That’s why you can accidentally get contaminated with such a malware program if you happen to interact with this type of shady email scams.
The good news is that there is a removal guide below, which can help you remove “I Sent You An Email From Your Account” in case that the scan detects it on your PC. And the sooner you eliminate the infection, the better, because if not removed on time, this Trojan can mess up your computer in a really bad way. Not only can it provide its criminal creators with full remote access to your machine but it may also insert other viruses and malware into your computer, including ransomware and spyware, without your knowledge.
SUMMARY:
| Name | “I Sent You An Email From Your Account” |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | In most of the cases, there aren’t any particular symptoms which can give the Trojan horse away. |
| Distribution Method | Spam, malicious emails, fake messages, misleading links, sketchy pop-ups, infected websites. |
| Detection Tool |
Remove “I Sent You An Email From Your Account” Bitcoin Email
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment