This page aims to help you remove IDP.ALEXA.51 Virus. These IDP.ALEXA.51 Virus removal instructions work for every version of Windows.
What is idp.alexa.51 ?
If the question “what is IDP.ALEXA.51?” brought you to this page, then you have come to the right place.
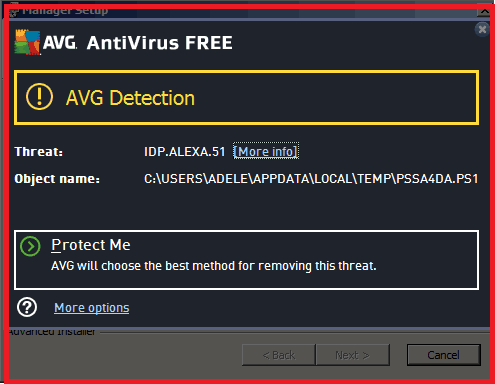
IDP.ALEXA.51 is a detection most often tied to Avast and triggered by online games like “Plants vs. Zombies” and “SeaMonkey”. The detection is often originating from .exe and .tmp files located in Windows folders like WindowsPowershell, %appdata% and %temp%.
What is idp.alexa.51?
The removal guide below is made with the sole aim to help you successfully clean your system from this nasty threat. We say nasty because this is one of the most threatening viruses available online that comes in the form of a Trojan horse. As you probably know, Trojans are famous for their especially cunning and harmful nature and dealing with such threats would require your full attention. Therefore we have prepared a very detailed guide with exact steps and instructions on how to safely delete the malicious files and recover your PC. Another useful thing you will find here is a handful of tips and tricks on how to protect your system and prevent infections in the future. We would also point out some specifics about Trojan horses, which will help you better understand the problem you are facing and effectively get rid of it. It is really worth the read.
The IDP.ALEXA.51 Virus
The IDP.Alexa.51 Virus is a virus detection for a trojan malware infection mostly used by avast antivirus.
You probably wonder how you got IDP.ALEXA.51 Virus on your PC in the first place. Well, we would start by saying that such infections happen very sneakily and they are really hard to detect. In fact, Trojan horses are named like that not by chance. These bad guys are really tricky and they infect unsuspecting users in ways and locations where no one even notices them. Trojans like IDP.ALEXA.51 Virus rely on delusive tactics and mask themselves like seemingly harmless files, this way tricking users into clicking on them. This is known more as social engineering tactics that mislead the unsuspecting victims into interacting with the infected payload. Very often Trojans provoke user’s curiosity by camouflaging themselves like some interesting content – files, images, links, ads, offers, email attachments, applications and many more. Once the victim interacts with the content, the harmful script gets immediately activated and introduces the malware right into the system, usually without any symptoms. If you have been infected with a Trojan, you have every right to be concerned about your system’s security and privacy, because such viruses are developed to do literally everything malicious you could think of: from spying on you, to stealing data and credentials, to destroying the system or even introducing Ransomware to your PC. That’s why it is highly recommended to remove this infection as soon as possible and in the next lines we will show you exactly how to do that.
IDP.ALEXA.51 Avast
IDP.ALEXA.51 is an Avast triggered detection for numerous trojan threats mostly related to online video games.
As we already said above, the Trojan’s malicious capabilities are many. Malware like IDP.ALEXA.51 Virus is usually developed with a “mission” to create serious vulnerabilities in your machine and this way help other malware easily find its way to your PC. With its help, people with malicious intentions can gain access to your computer and use it for various criminal deeds and online fraud. Trojans are the hackers’ favorite way to establish remote control over a computer and turn it into a zombie or involve it into a Botnet that loads targeted malware attacks.
Usually, this type of malware tries its best to stay unnoticed and there are hardly any symptoms that can help you detect the infection without good antivirus software. However, there are a few things that victims of IDP.ALEXA.51 Virus may notice during the malware activity. For example, some unusual movements with the cursor of the mouse over the screen may indicate unauthorized access to your machine. Some programs may shut down or open on their own without your interaction or you may notice that your hard drive is loaded with data, though you have not placed anything there. All these may be signs of exploited system vulnerabilities and once you detect any such behavior it is a good idea to fully scan your machine for malware.
Tips and tricks on how to protect your system from IDP.ALEXA.51 Avast Virus
Despite the rise of Ransomware, Trojan horses are still one of the biggest threats among the known malware found online. Therefore, prevention still remains the best option to keep such threats away. Your system’s safety could be improved if you install a reputable antivirus and antimalware software that is daily updated and runs regular scans on your machine. In case you need suggestions, you can check our recommendations in the links below. Another way to minimize the risk of interacting with infected content is to avoid suspicious files and online locations in the first place. E-mail spam campaigns are the favorite method of hackers to distribute malware; therefore you should resist the temptation to click on every file or link you receive. Scan your inbox for harmful e-mails and never install anything that you are not sure when it comes from.
How to remove IDP.ALEXA.51 Virus infection?
Detecting and removing Trojan horses could require a bit more attention and system knowledge. To successfully delete this nasty infection from your machine, please follow closely the instructions in the guide below. Do notice tough, that during the manual removal you will be interacting with some major system files, which if corrupted may crack the system. Therefore, if you are unsure how you can handle the manual process, the IDP.ALEXA.51 Virus removal tool is there to detect and delete the infection for you.
SUMMARY:
| Name | IDP.ALEXA.51 Virus |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware and can introduce many other malware to your PC) |
| Symptoms | System crashes, unusual system behaviour, high CPU usage. |
| Distribution Method | Trojans usually camouflage as seemingly harmless files and are distributed through spam emails, attachments,files, images, torrents, applications and many more. |
| Detection Tool |
Remove IDP.ALEXA.51 Avast Virus
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:

![]()
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
![]()
Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment