Idp.alexa.53
Idp.alexa.53 is a malware detection message that certain antivirus programs show to warn the user about the potential presence of a virus in the computer. Idp.alexa.53 could be a false positive, but it could also mean that your computer is infected.
What is idp.alexa.53?
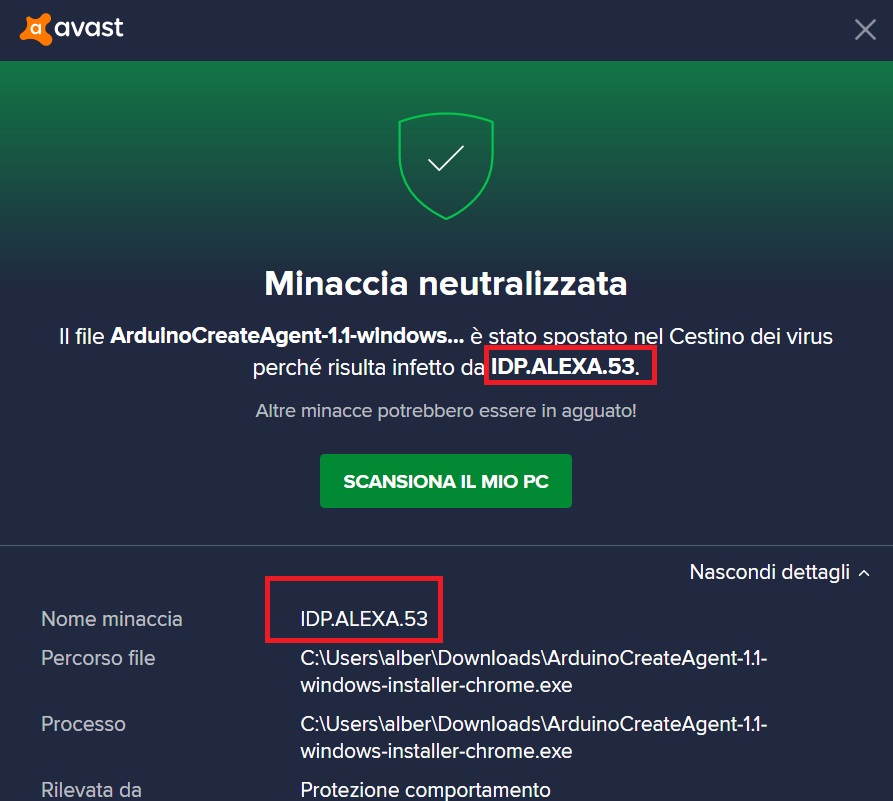
Idp.alexa.53 is a warning message that Avast, AVG, and other antiviruses sometimes show when they detect something suspicious in the system. If you see the Idp.alexa.53 detection warning, this could mean that your machine has been attacked by a malicious virus.
If you see this warning message from your antivirus, this could mean one of two things. The first possibility is that the antivirus detected a suspicious but non-harmful file in your system and it categorized it as the Idp.alexa.53 threat. In such cases, if you are certain that the detected file is harmless, you can whitelist it in the antivirus so that you won’t be getting the same warning message again. However, it is also possible that the detected file is indeed threatening and is from a real Trojan Horse virus, in which case you must perform the action suggested by your antivirus in order to secure your computer. If the threat is real, we also advise you to complete the malware-removal guide we’ve posted on this page.
Idp.alexa.53 – is it a virus?
Idp.alexa.53 is virus detection from your antivirus – its appearance could mean you have a virus in the computer, but it could also be a false positive. If the Idp.alexa.53 is triggered by a virus, you find and eliminate said virus ASAP.
Obviously, one of the main problems here is that it may be difficult to tell whether the warning is a false positive or not. Many users who have encountered it report that it was triggered by a file (or files) related to legitimate computer games such as Plants vs. Zombies and SeaMonkey. If you are convinced that the file(s) triggering the malware detection is from a reliable and safe program (such as either of those two games), then it would probably be safe to whitelist that file(s) so that the warnings stop. However, it must be noted that oftentimes malware threats such as Trojan Horses are added to seemingly safe and desirable programs and they infect the computer once those programs are installed and started. Therefore, remember to consider the source from where you downloaded the program the files of which are causing the Idp.alexa.53 detection. Was it a reputable source or was it some sketchy and potentially unreliable site? If it was the latter, it may be better to quarantine the flagged files and then complete the guide we offer on the current page.
Idp.alexa.53 – what does it do?
Idp.alexa.53 could be a malicious Trojan Horse virus that your antivirus warns you about. If the Idp.alexa.53 detection is truly due to a virus attack, the Trojan Horse causing it could damage your files and software, spy on you, and more.
If it turns out that the Idp.alexa.53 detection is caused by a real threat, this means that your whole system and the data stored in it are in danger and immediate actions need to be taken to secure the computer. Some Trojan Horses (especially newer ones) could have very advanced abilities and could be used in all sorts of harmful ways. They could steal the user’s data, spy on what you do on your PC, use the resources of the machine for cryptocurrency mining, send out spam messages with malware from your system to other users, and more. It is critical that you find and eliminate any such threats from your computer if you have the slightest suspicion that the machine may be infected.
Is Idp.alexa.53 specific to Avast?
The Idp.alexa.53 malware detection isn’t specific to Avast but Avast users seem to be the ones who see it the most often. That said, other antivirus programs such as AVG may also detect Idp.alexa.53 and show you this security warning.
It seems that this malware detection is typically seen in the Avast antivirus but some users report also seeing it in other antivirus suites (AVG being one example). It is likely that other antiviruses would simply show a different warning message when they detect the same threat. It is important to note, though, that this detection doesn’t mean there’s anything wrong with your antivirus. Even if the detection is a false positive, there must have been something in the flagged file that triggered the warning. For instance, vulnerable software could also sometimes cause such malware detections. Because of that, it may also be a good idea to update the software on your PC just in case there are any unpatched vulnerabilities that Trojans and other threats may exploit.
SUMMARY:
| Name | Idp.alexa.53 |
| Type | Trojan |
| Detection Tool |
Remove idp.alexa.53 from Windows 10
To remove idp.alexa.53 from Windows 10, you must uninstall any unwanted programs, quit any suspicious processes from the Task Manager and clean your Startup Items, Hosts file, Registry.
- Go to Control Panel > Uninstall a Program and there uninstall any items that could be linked to the idp.alexa.53 detection.
- Check the Task Manager for questionable processes and quit what you find.
- Open the Hosts file and the Startup section of System Configuration and check them for unwanted modifications/items.
- Open the Registry Editor, search for items related to idp.alexa.53 and delete any such items you may find.
Those steps provide a quick summary of the actions you must perform in order to take care of idp.alexa.53. However, if you need us to further elaborate upon these steps and provide more detailed instructions, refer to the following paragraphs where we offer a more in-depth explanation of what exactly must be done in order to delete the software that is causing the idp.alexa.53 detection.
Detailed Guidelines
Step 1: Uninstall rogue programs
If you think there may be a program that causes the idp.alexa.53 warning to be triggered, you must go find that program and uninstall it.
First, open the Starting Menu, type Programs and Features in it, and hit the Enter key from your keyboard.
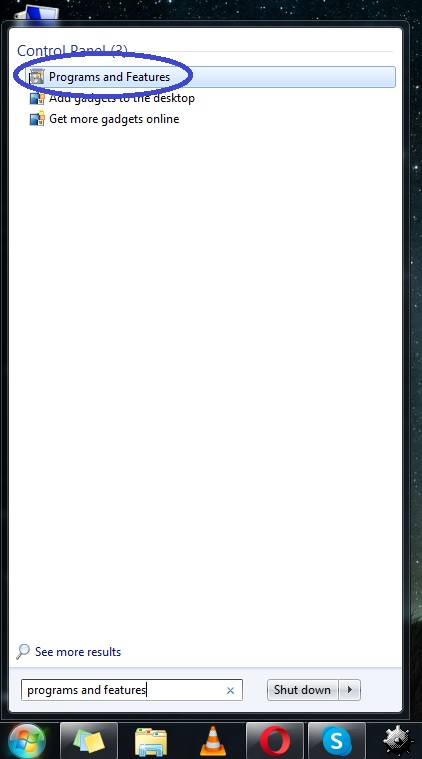
The list that appears on your screen contains all programs that are installed on your PC at the current moment. Look through the listed items trying to find the program that may be behind idp.alexa.53. It could help if you look for entries added close to the time when the detection warning first started appearing.
If you find the suspicious program, click on it and then click the Uninstall option from the top of the window. Follow whatever steps show up in the uninstallation wizard but make sure that you don’t allow anything related to the program to stay in the system (including any personalized settings for it).

Once the uninstallation completes, restart the computer and proceed with the next steps.
Step 2: Check for rogue processes
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press the following keys from your keyboard: Ctrl + Shift + Esc. In the window that opens (Task Manager), click the Processes tab. In that tab, you must find a process that could be related to idp.alexa.53. This could be a tricky task because you are not expected to know all the regular processes that are normally running in the computer in order to be able to single out the ones that are rogue and shouldn’t be there. One thing that could help spot any rogue processes is to first focus on the processes that are consuming the largest amounts of RAM and CPU. If among them, you see anything with a weird and unusual name or a name that could be associated with the program (or programs) you uninstalled during the previous step, look up that process name on the Internet and see what you can find.
In most cases, if a given process is malicious/unwanted, searching for its name will quickly lead you to reports from other users or from researchers posted on security forums that confirm the process is rogue. If you find such information about any suspicious process that’s currently running in your system, return to the Task Manager, right-click the process in question, and select the option that opens its File Location.

Next, scan all the files in the location folder with the free online anti-malware scanner that we offer below:

If any of the scanned files turns out to be malware, go to the related process, quit it, and then make sure to delete the entire location folder. If this can’t be done at the moment, delete the files in the folder (the ones that you are allowed to delete) and proceed with the guide. Later, once you’ve made sure to complete all other steps, try once more to delete the location folder if you weren’t able to delete it earlier.

Note: If you’ve learned from a reliable source that a given process in your PC is unwanted, there’s may be no need to scan its files – you can directly quit it and delete its file location.
Step 3: Go into Safe Mode
When you are in Safe Mode, most unwanted/malicious processes shouldn’t be allowed to run so even if you didn’t find and quit all of them during the previous step, while you are in Safe Mode they shouldn’t be a problem or an obstacle. Click the provided link if you need instructions on how to get your machine into Safe Mode.
Step 4: Clean the Hosts file and the Startup items
Press the Winkey and R keys from the keyboard and when the Run search bar appears, copy the following line of text, paste it in it, and click OK:
- notepad %windir%/system32/Drivers/etc/hosts
Look at the bottom of the text in the notepad file that opens (Hosts) and see if there are any IPs listed there. If there’s any IP addresses below the Localhost line, copy them and post them in the comments. Once we look at them, we will be able to determine if they have been placed there by any type of rogue software, and we will tell you if you have to delete them from the file.

The next thing you ought to do is type msconfig in the Run search box, click OK, open the Startup tab, and look for entries that are unfamiliar and/or suspicious. Anything that looks like it shouldn’t be there needs to be unchecked. Once you uncheck all questionable entries, select Apple and then OK.

Step 5: Clean the Registry
This final step will require you to delete any unwanted/rogue items from the Registry of your computer. Since there are lots of sensitive settings stored there, you ought to be very careful when deleting anything. If you can’t be sure a certain item should be deleted, we strongly suggest consulting us through the comments section before you proceed with the deletion!
Firstly, open Run again, type regedit, and hit Enter. Then click on Yes to allow the Registry Editor to make system changes and when the Editor opens, press Ctrl and F to evoke its search bar. In the Registry Editor search, type idp.alexa.53, search for related items, and if anything gets found, delete it. Make sure to keep repeating the search and deleting what gets found until no more related items remain.

Next, do another search with the name of the program you uninstalled in Step 1 (if you uninstalled any program in that step) and delete all Registry items related to it as well.
Lastly, open the following locations from the left panel of the Registry Editor:
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
When you get to these locations, check them for items with suspicious names – names that seem unusually long and/or contain randomized letters/numbers. If you there are any such items in either of those locations, you should delete them. Of course, if you aren’t sure about a certain item (items), you should first ask about it in the comments.
Step 6: Use professional removal software
We really hope the steps thus far have allowed you to deal with whatever may be causing the idp.alexa.53 detection warning. However, it is possible that even after completing everything, the problem persists. In such cases, it is strongly recommended that you try using a reliable specialized program to clean your system because there may indeed be a hidden malware in the computer that has managed to evade your troubleshooting attempts. In such cases, it is best to use professional software to scan and clean your computer. One such malware-deletion tool that we highly recommend can be found linked on the current page – with its help, you should be able to quickly take care of anything unwanted that may be in your system causing the detection warning to appear.

Leave a Comment