Industrate
Industrate is a software application that integrates itself in the main browser on Apple iOS devices. After this, Industrate converts the Chrome or Safari browser into a platform for online advertising.
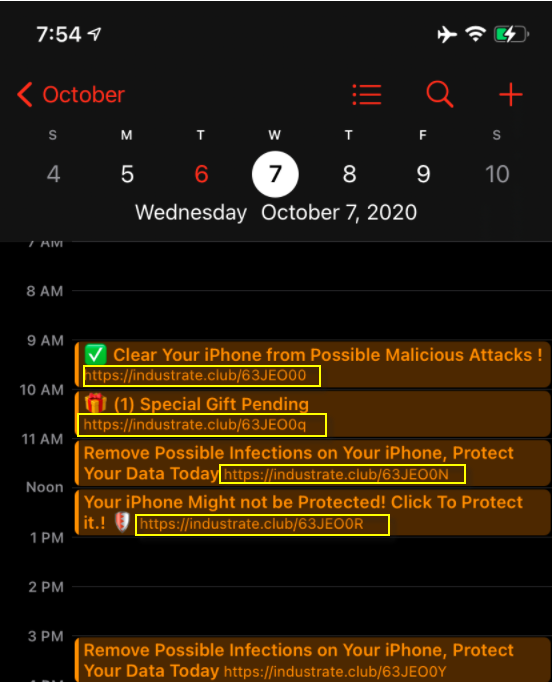
Industrate.club will fill you calendar with unwanted fake events.
This is a common type of application more commonly referred to as a browser hijacker. And it gets its name due to the highly intrusive practices it is involved in. For example, browser hijackers like Industrate, will very often alter the settings of the infected browsing application, thus changing the default search engine and/or browser homepage. In addition, by installing ad-generating components on the device, your browser will very soon start flooding your screen with screen-wide banners and spontaneously appearing popups that result in page redirects to various sponsored sites.
The only way you can restore your old browser configurations and stop seeing all the annoying online ads is if you thoroughly remove Industrate from your iPod, iPad or iPhone. And to do this, you may require the help of a removal guide such as the one we have published below. It contains but a handful of steps and you should be able to rid yourself of the pesky software in no time.
As far as your device’s security is concerned, Industrate does not pose a direct threat to it, as it is not a virus or malware. However, you should be aware of the fact that as a result of its intensive advertising practices, Industrate may potentially expose you to actual viruses such as Trojans, ransomware and others.
SUMMARY:
| Name | Industrate |
| Type | Browser Hijacker |
Industrate iPhone Removal
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and clean up your phone’s calendar events if they are infected.
2. Find browser extensions related to the threat and how to remove them.
3. Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment