*Source of claim SH can remove it.
Ingenering Group Inc Product
Ingenering Group Inc Product is a dangerous computer virus recognized as a Trojan Horse capable of mimicking system processes to avoid detection from your antivirus. Threats like Ingenering Group Inc Product are very difficult to detect on time and can damage your computer in many different ways.
As their name suggests, these malicious programs typically employ some form of disguise that allows them to infiltrate any system without triggering any security warnings. In some cases, if there is a reliable and up-to-date antivirus in the computer, the threat may get detected but it is important to remember that antivirus programs are most effective against known infections that are already in their databases. However, against a new and relatively unknown threat such as Ingenering Group Inc Product, the effectiveness of most antiviruses wouldn’t be as high. The problem with recently released Trojans like Ingenering Group Inc Product is that security researchers are yet to gather enough information about the virus and add it to the database of their antivirus. There are certain tools that some of the more advanced antivirus solutions have that may manage to stop a unknown Zero-Day Trojan virus but those tools’ effectiveness varies and you shouldn’t solely rely on them. In the end, the importance of being vigilant and prepared to act quickly cannot be overstated and that is why we must warn you about some of the potential symptoms that could be related to an attack from Ingenering Group Inc Product.
Potential infection signs
It is well-known that the Trojans are very stealthy and difficult to spot threats that oftentimes carry out their malicious tasks with minimal symptoms, making their timely detection quite unlikely. That said, in some instances, a virus of this type could end up causing some rather obvious infection red flags. For instance, if the Trojan manipulates the system processes too much, sudden errors, freezes, and even BSOD crashes may start to occur. If you have been noticing any such symptoms on your computer in recent days, it is critical that you investigate the cause of the problem because it could be a Trojan Horse attack. Other possible infection signs could be corruption of personal data, unauthorized changes in the settings of different programs, severe slow-down of the machine caused by unknown processes or by processes that don’t normally consume high amounts of CPU or RAM, etc. In general, any type of system instability that cannot be contributed to any normal process or program should be seen as a potential sign of a malware infection. Of course, there could be other reasons for most of the aforementioned symptoms but we suggest you don’t take any chances and immediately go to the guide we have prepared for our readers and complete it in order to eliminate anything that may be related to the malicious Ingenering Group Inc Product.
After you get rid of the malware, it is also important to remember to keep your computer clean and safe in the future by staying away from sketchy sites and download sources that distribute pirated or low-quality software. In the end, the factor that contributes the most to the increasing number of malware infections is the users’ own negligence and carelessness so be sure to not give Trojans like Ingenering Group Inc Product the opportunity to enter your system from now on.
SUMMARY:
| Name | Ingenering Group Inc Product |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
How to Uninstall Ingenering Group Inc Product
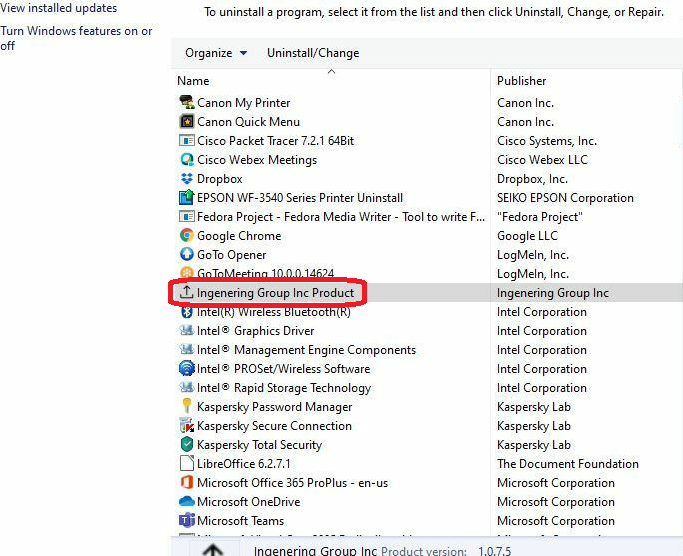
The first thing you could do to try to remove Ingenering Group Inc Product is search for a program that may have brought this threat to your computer. Most Trojans get distributed disguised as programs that initially appear normal and so users download them without suspecting the threat that’s hidden in them. You can see all the programs installed on your computer by typing Uninstall a Program in the search field of the Start Menu and opening the first result. The list shown on your screen contains all apps and programs on your PC and there you may be able to find the one responsible for the Trojan Horse infection.
There may or may not be an item with the Ingenering Group Inc Product name on it so look carefully through the list and if you don’t find Ingenering Group Inc Product, then look for other programs that seem unfamiliar, suspicious, or that seem to have been installed without your informed approval. Additionally, you can sort the list by date and look at the most recent items – anything installed around/just before the Trojan symptoms started appearing should be regarded as the potential cause of the infection and therefore removed (unless, of course, you know for a fact that a given program is safe and not related to Ingenering Group Inc Product).
When you think you have singled out the program responsible for bringing Ingenering Group Inc Product into your computer, click on its name and then select the Uninstall button at the top.

Follow whatever uninstallation prompts get shown on your screen to remove the program, making sure that you uninstall everything, including any personalized settings or bonus components that the program in question may have brought into your PC.
In case you get shown a dialogue window like the one from the next image, be sure to select NO.

After you are done with everything here, restart the PC and try to determine if there are still any symptoms of the Trojan Horse’s presence. If you still think the malware is in the system, proceed to the following steps and complete the rest of this guide. If the problem seems to have been resolved, you can stop here rather than completing all of the steps.

Start the Task Manager of your computer either by pressing the Ctrl + Alt + Delete buttons and selecting Task Manager or by pressing Ctrl + Shift + Esc. In the window of the Task Manager, you must select Processes from the top and try to find the process/processes launched by Ingenering Group Inc Product. Those could have the name of the virus but may also be named in an entirely different way so be watchful and if you don’t find anything named Ingenering Group Inc Product, then look for other items with odd names that seem out of place. You can sort the processes by the amount of RAM or CPU consumed by to see which are the most resource-intensive ones since the process(s) of the Trojan is likely to be requiring lots of resources from your system.
If you suspect a certain process of being linked to the virus, open your browser and look up the name of that process to see what information you can find. It is not excluded that the process you suspect is actually a legitimate one from your OS, in which case you should look for another one (unless your research suggests that the suspected the malware may be using the name of the otherwise legitimate process to disguise itself).

Once you have confirmed that the process you think is coming from Ingenering Group Inc Product isn’t from your OS, right-click on it in the Task Manager, select the Open File Location option and scan all the files there using the following free online scanner:

You can also use your own security program if you have such a program. Combining the two methods would obviously increase the chances of detecting any malware that may be hiding in the scanned files.
If any of the items that you are scanning is detected as malware, quickly go back to the Task Manager and quit the suspicious process by selecting it and then clicking on the End Process button at the bottom of the Task Manager window.
Next, delete the whole folder that is the file location of the process. If you cannot do that because one or more of the files from that folder can’t be deleted, open the folder and delete all other files that are in it. By the end of this guide, you should be able to return to this folder and delete it together with any files that may have been left inside it so make sure to not forget to do that.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
You must now enter Safe Mode to keep any Ingenering Group Inc Product processes that you may have missed from running on the computer and interrupting the troubleshooting process. For users who may need help with entering Safe Mode, you can follow the steps from this page where it is explained how you can do it.

*Source of claim SH can remove it.

Next, you must clear any unneeded and/or related to Ingenering Group Inc Product startup items so that your PC doesn’t automatically launch them on startup. You can do this by typing System Configuration under the Start Menu, opening the System Configuration icon, and checking the Startup tab. There, you will see what apps and programs are set to start automatically on startup – look through the list, and uncheck the ones you think may have anything to do with the virus. Also, it may be a good idea to uncheck startup items that are listed with an Unknown manufacturer.
Finally, save the changes and close the System Configuration window by clicking on OK and proceed with the remainder of this guide.


Place the following line in the Start Menu and hit Enter: notepad %windir%/system32/Drivers/etc/hosts. A notepad file titled Hosts must appear on your screen – this is a file that gets commonly targeted by different forms of malware and undesirable software, so you must check it for any unwanted modifications that Ingenering Group Inc Product may have made to it. If there is anything written below the Localhost line in the Hosts file, this means that a third-party program has modified the file, and it is likely that the third-party program is the Ingenering Group Inc Product virus. However, we will need to look at the lines written below Localhost before we can tell you if that is indeed the case, so we suggest that you copy them and place them down in the comments. We will reply to your comment and tell you if the lines are from the virus and if they are, you will have to erase them from the Hosts file and save the changes to the latter.

Important!: The current step will require you to delete items added to your computer’s Registry by the Ingenering Group Inc Product virus. The Registry stores many essential system settings, so you must be very careful to not delete something you are not supposed to. If have any doubts about the nature of a given item from the Registry and are not sure if said item must be deleted, it is recommended that you first consult us via the comments section below before proceeding with the deletion.
To access the Registry Editor, go to your Start Menu, type regedit in it and click on the icon from the search results titled regedit.exe. Windows will want you to confirm that you want to open the Registry Editor and allow it to introduce changes to the computer so click on Yes to open the Editor.
Once you have the Registry Editor in front of you, go to the Edit Menu and click on Find. In the Find window, type the virus name in the search field, click on Find next and if an item is found, select it and delete it either by pressing the Del key from your keyboard or by right-clicking on the item in question and then on the Delete option from the context menu. Keep repeating the search and deleting any items that get found until there are no more results for the name of the Trojan.
Finally, manually navigate to the Registry directories/folders listed below. In them, you must look for items/folders with names that seem out of place. Usually, those names would consist of long strings of randomized characters that don’t seem to make any sense. If anything like that catches your attention, delete the folder(s) in question. Again, if you are uncertain and can’t decide whether a particular item is to be deleted, you can always ask us about it down in the comments. Now, here are the Registry directories we told you about:
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
Once you’ve completed this final step, remember to go back to the file location folder of the Trojan Horse process from Step 1 and delete it if you didn’t manage to do that earlier.

Leave a Comment