Jope
Jope is a ransomware variant of the file-encrypting type. This means that Jope encrypts specific file types on the computers of its victims and then blackmails them for ransom.
The Jope Virus File Encryption
By encrypting the files, this ransomware basically denies users access to these files. Hence, no program or software will be able to make sense of the data and therefore won’t be able to open it. In turn, the hackers offer to provide with a solution for this problem in the form a decryption key. But, of course, there’s a catch. And the catch is that you will first be required to pay a hefty sum of money as ‘ransom’, which is how this malicious software type gets its name.
Unfortunately, ransomware viruses like Jope are among the most dangerous pieces of malicious code out there and are very difficult to deal with. But that doesn’t mean that paying the hackers is the only option you have. First and foremost, you need to remove Jope from your system so as to ensure that it doesn’t encrypt any files that you manage to recover. We have described this process in step-by-step format in the free removal guide below.
But in the second part of the guide, we have also listed several alternative file-recovery methods that you can try before you decide to send your hard earned cash to some cyber criminals.
The Jope virus
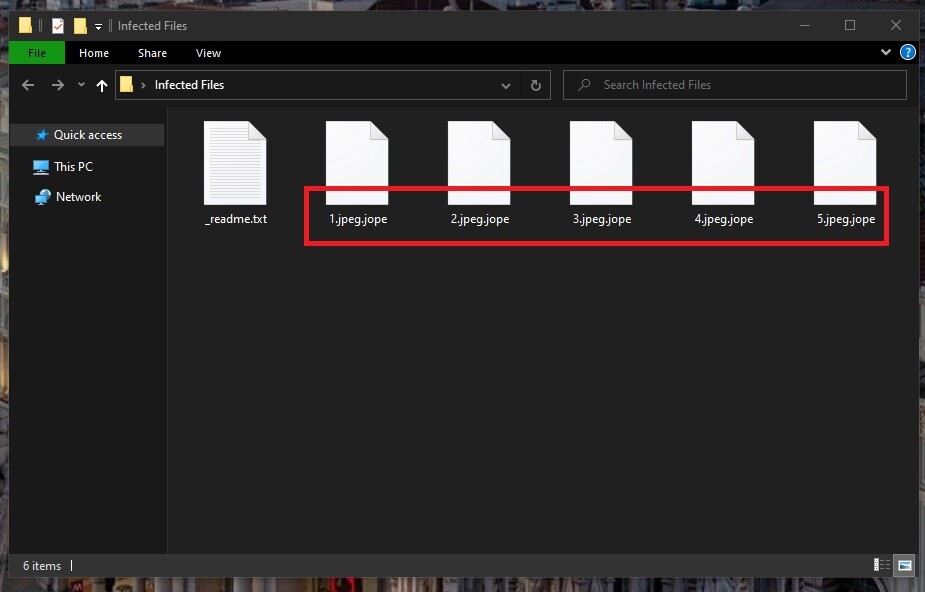
The Jope virus can target most commonly used file types including images, videos, audios, documents, etc. The Jope virus then creates encrypted copies of the files whilst deleting the originals.
The above can at times be a rather tedious process and take up to several hours to complete, depending on the computer’s processing power and the amount of data stored on it. And this can, in turn, sometimes offer the victim user an opportunity to stop the virus in its tracks before it manages to encrypt all of the files on the PC. But in order for this to happen, the user would have to be prompted to check the Task Manager where the ransomware would be the process using the most system resources. Most probably this ‘prompt’ would be a slowdown in the system’s overall performance, as ransomware doesn’t otherwise have any symptoms.
Furthermore, relying on your antivirus to stop Jope is a mistake, too. In most cases, antivirus software will not be triggered by ransomware, and some advanced versions of this malware class can even disable the antivirus on your computer.
The Jope file encryption
The Jope file encryption is typically very complex and the only way to reverse it is with the help of a special decryption key. In some instances, users may be able to find a solution for the Jope file encryption in decryptor tools online.
Other possible solutions include restoring your files from system backups, for example. We have mentioned a few others in the guide below. But the best and absolute surefire way to disarm any ransomware infection is by keeping copies of your most important files on a separate drive.
SUMMARY:
| Name | Jope |
| Type | Ransomware |
| Detection Tool |
Remove Jope Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

the information is useful but not enough how to recrypt the infected files please all my files ecrypted by this virus how to get it again pleas reply quickly
Hi Hadeer,
on the bottom of the guide you will find a link, that will lead you to a decryption page. There are number of methods you can try there, but .Jope virus is a new variant and there is no decryption to it yet.
Today I face the JOPE ransomware, can I resolve by cleaning windows and reinstall it
Hello Suhas, if you only reinstall the OS and completely wipe the hard drive your problem will be resolved because the ransomware will also be deleted in the process, but if you only uninstall the operating system there is a good chance your PC will remain infected.
In step 4, how can I determine which file is newly added and which is not? And are the newly introduced files viruses? How can I discern that? Are they written ambigiously?
And also if I only deleted %temp% do I still need to do it in safe mode?
Hi Asad, going through your windows registries to look for the right files to delete can sometime prove to be very difficult, that is why we recommend you to download Spy Hunter as it does all that for you and it will not cause problems on your operating system.
what happen after 48 hour…?
can the app clean my jope…?
Hello Teguh Chun, after the 48 hour waiting period you can use Spy Hunter to delete the virus that has infected your system.
Respected Sir and bro
My system infected by .jope virus and renamed all files and I reinstalled OS on 5th april 2020. But today I saw that my brother’s son videos are changed to .jope extension. There is no other videos of his. If it not recovered,
we don’t have his childhood videos.
Please I beg to all of you please help me.
Hi Nagaraju,
Jope Virus is still new and there is no decryption to it yet.
hola, tengo mi hdd portatil le entro el virus jope, mi pc estubo infectado pero lo formatie y se libero pero lo q daño fue mi hdd portatil tengo archivos y documentos de suma importancia como puedo solucionarlo, estare ala espera de su respuesta, gracias
Hola, Dennis,Lo mejor que puede hacer es hacer una copia de seguridad de esos archivos en otra unidad para mantenerlos seguros hasta que esté disponible un desencriptador.