This page aims to help you remove .karl for free. Our instructions also cover how any .karl file can be recovered.
.karl
.Karl is a ransomware that encrypts users’ computer, making them unreadable. All relevant personal files are encrypted with a custom extension and users are left with a message asking for a ransom payment to return the files.
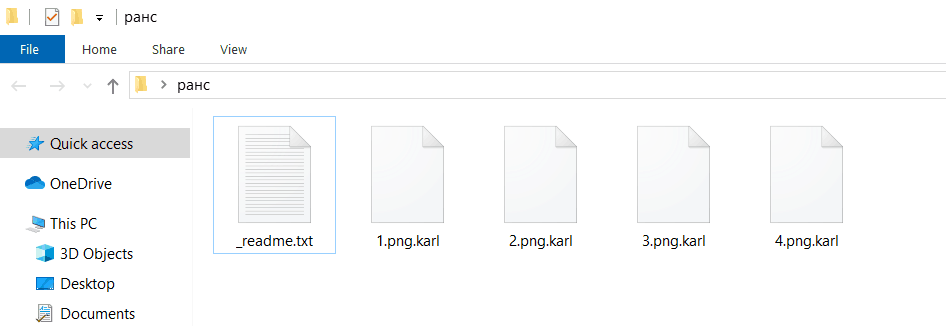
An example of .karl’s encryption.
In case that a cryptovirus called .karl has secretly encrypted your files, and has asked you to pay a ransom for their decryption, you must be wondering about what to do. There may be an option, though, and the following removal guide may assist you with avoiding the ransom payment, and removing the infection from your system.
Unfortunately, what you have been infected with is a very hazardous cryptovirus from the Ransomware family that makes it impossible to open your files by applying a powerful encryption to them. This is why we’ve prepared a special removal guide below, to assist with the removal of .karl in the best possible way. In the next lines, you will find a set of instructions on how to detect and remove the infection, as well as some file-recovery suggestions, that do not involve paying a ransom to the hackers behind the Ransomware. Keep in mind, though, that threats of this category are very challenging to deal with, and you may need more than just a removal guide to effectively minimize the consequences of their attack. So, please spend a couple of minutes reading the information that follows, in order to gain a better understanding of the risks and the possible solutions.
The .karl virus
The .karl virus is a ransomware that hijacks users by placing a trojan in their system. The trojan slowly starts encrypting files with the eponymous .karl extension, making them inaccessible without the encryption key.
In contrast to other malware types, which try to remain hidden for as long as possible in the system, .karl uncovers itself immediately after it has completed the encryption process. It typically does that by displaying a ransom note on the screen, right after all the files have been secured with a powerful and secret algorithm. The ransom note informs the victims that without a special decryption key, they cannot access their files, and asks them to pay a certain amount of money for that key. Unfortunately, this special decryption key is in the hands of the hackers, and they typically ask for a lot of money in order to send it to the victims. What is really bad about the whole situation is that there is no other way to unlock your files and reverse the encryption. An error message will appear every time you attempt to open them, and no software will be able to recognize them. And this is the reason why the cyber criminals may get quite harsh when they start blackmailing you to pay them to decrypt your files. They may give you a short deadline to transfer the money, or threaten to double the ransom amount, or even destroy the decryption key if you don’t fulfill their demands. The idea is to manipulate you, and make you act impulsively, without giving yourself time to research your alternatives.
The .karl files
Any .karl files signify an encryption algorithm places by a ransomware on the user’s files. They are easily recognizable because they have a double extension, e.g. example.jpeg.karl.
Many users get panicked from the fact that they can’t access their files, and let the hackers’ ransom demands intimidate them. However, paying the ransom hides a lot of risks, and often leaves them with empty pockets and files that are still inaccessible. In fact, many Ransomware victims never get the “promised” decryption key form the hackers, despite having paid all the ransom money the blackmailers had demanded. That’s because the crooks either disappear with the money or simply “forget” to send anything back. Of course, there are cases where the hackers do send a decryption key to the victims, but there are also many instances where that key proves utterly ineffective, and fails to decrypt the files. At the same time, once the hackers have compromised the computer, and the Ransomware is active in it, nothing can prevent them from causing even more harm. This is why cleaning up the infection is the first move to be taken, rather than making the criminals richer. You can find out exactly how to do this in the removal guide below, and safely remove .karl from your device.
The .karl ransomware
.karl is the latest ransomware of the djvu ransomware strain and exhibits the same symptoms as the rest of its family. What is notable is that the .karl ransomware’s trojan still remains in the user’s system, leaving the files to fall back again to the ransomware.
SUMMARY:
| Name | .karl |
| Type | Ransomware |
| Detection Tool |
Remove .karl
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment