Khonsari
Khonsari is a highly-advanced PC infection that has the purpose of encrypting sensitive data on your computer to keep it inaccessible to you. After Khonsari completes the encryption procedure, it places a ransom-demanding message on your desktop.
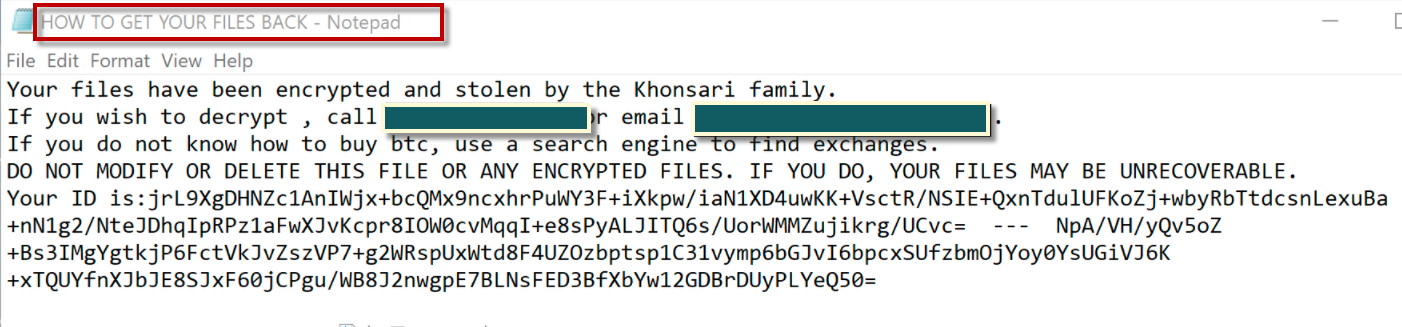
The Khonsari ransomware HOW TO GET YOUR FILES BACK.TXT ransom note
If Khonsari has taken the data inside your computer “hostage” and you can no longer open any of your personal data files because an encryption has been applied to them, then you should definitely read the information available to you inside the present article as this really is a very problematic malware threat and you should know all your options at this moment so that you can decide what to do next.
The main problem with malware threats like Khonsari is that the data encryption used by them is oftentimes way too advanced for anyone to be able to decrypt it. Typically, the only way to get the access to the encrypted files restored is through a unique key that is specifically generated for the specific encryption code. Of course, the only people in possession of this key in case Khonsari has attacked you would be the hackers that are behind this whole scheme. Their goal is, of course, financial profit through illegal means. In this case, they would try to blackmail you – they’d tell you that you must send some of your money to them in order to “purchase” the access key that would supposedly bring your files back to their accessible state. Because of all this, the category of viruses similar to Khonsari and Shgv are mostly known as Ransomware. There are other forms of Ransomware that do not target the files and instead focus on some other component of the system but the ones that are the most problematic are indeed the file-encrypting viruses.
The Khonsari virus
The Khonsari virus is a threat from the Ransomware file-encrypting family and its goal is to deny you access to your most valuable files by encrypting them. The Khonsari virus is used for money-extortion purposes as it asks for a ransom to release the files.
In the end, it is up to the user who’s victim of such an infection to make a decision about what to do in case of a Ransomware infection. It is important to remember, though, that paying may not always have the expected result. The hackers do not typically care about what happens with your files after the money they’ve requested has been received. After the payment is made, you’d be at their mercy and if they decide not to send you anything, there would be nothing you could do to change that. Because of this , it is generally not the best idea to go for the money transfer to the blackmailers as it may turn out to be nothing but an utter waste of money from your side.
The Khonsari file
The Khonsari file is any file that this virus program has managed to put under its encryption. A typical characteristic of the Khonsari file is that it will have a unique file extension that no program can recognize, which makes the file unopenable.
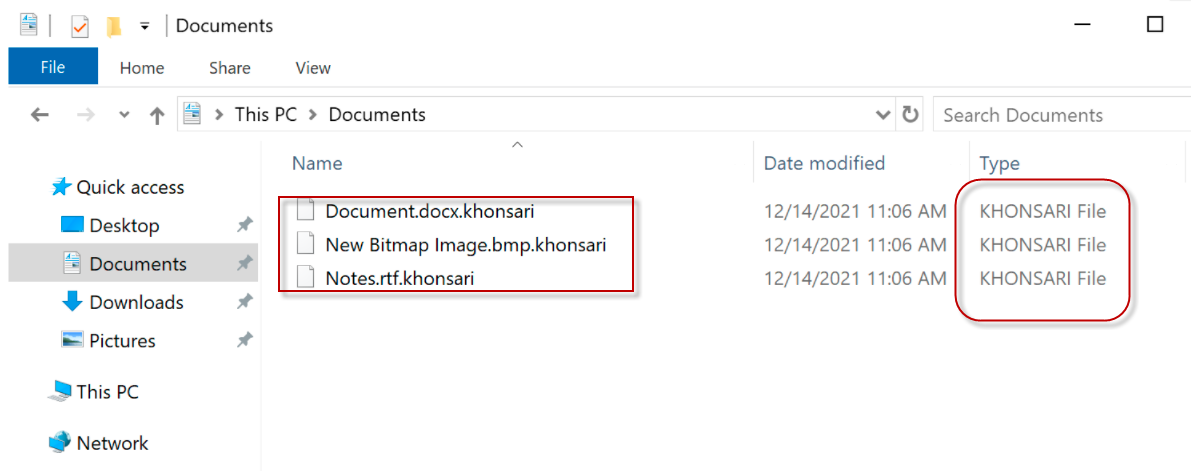
The Khonsari file ransomware
On the flip side, there could be some other things you may try that may or may not yield satisfying results. Know, however, that it really depends on each specific case how effective the alternative methods of dealing wit threats like Khonsari would be. Some of the luckier users may manage to get their data back but others may not be that fortunate. However, if you try the completing the guide we’ve provided below, you should at least be able to make the computer you are using safe again and ensure that you no more files would get encrypted on your computer.
SUMMARY:
| Name | Khonsari |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | In most cases, the users don’t notice anything before the ransom-demanding note pops-up on their screen. |
| Distribution Method | Fake and misleading clickbait ads ad pirated downloads are the usual tools used to spread Ransomware. |
| Data Recovery Tool | Not Available |
| Detection Tool |
Khonsari Ransomware Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Khonsari files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment