lAeSUZDqb File
The lAeSUZDqb file is classified as a ransomware virus of the file-encrypting subtype. This means that lAeSUZDqb encrypts the files on its victims’ machines as part of an extortion scheme. The idea behind it is that once the said files have been encrypted, they become unusable to anyone. No software will be able to read them and therefore no one can access the data. So, the hackers who have created the virus offer the victims the opportunity to get their files back in exchange for a certain amount of money, usually a rather significant one. The money is in a sense requested as ransom for the encoded data, hence where this malware category gets its name from.
Ransomware like lAeSUZDqb, Jaqw or Jasa is considered to be extremely dangerous, if not the most dangerous kind of malicious programs that you can find on the internet. And for this reason it’s important to duly assess the potential consequences of dealing with such infections.
Namely, we should point out that there’s a very real risk that you may never be able to regain access to your files. And if you think that paying the hackers whatever money they’ve demanded will guarantee you success in this, you’d best think again. There are many things that could go wrong and you might never receive the decryption key which is necessary to undo the encryption. Likewise, relying on alternative file recovery methods may not necessarily yield the desired results either. But at least these options won’t take a toll on your wallet. We have described then in the second part of our removal guide below, after the steps you need to take to remove lAeSUZDqb.
The lAeSUZDqb virus
The lAeSUZDqb virus uses a strong encryption algorithm to lock the files on your computer and make them completely inaccessible to you. This practice makes ransomware like the lAeSUZDqb virus among the most disastrous malware types out there.
On the one hand, yes, the encryption is very difficult to breach or reverse. And this makes recovering the encrypted data very difficult, with the potential of it remaining encrypted forever. But on top of that, this very instance of encryption also enableы ransomware like lAeSUZDqb to slide under the radar of most security software on the market. This is due to the simple fact that encryption is not in itself a harmful act. Much on the contrary, it’s actually a very helpful one. And it is so widespread and commonly used on a daily basis by the vast majority of internet users, that if it were to trigger antivirus programs, we wouldn’t be able to do a whole lot of things online.
Hence, we stress a lot on the importance of preventing ransomware attacks rather than relying on your antivirus to fend them off. In addition, frequently backing up your most important files and storing the copies on a separate drive will essentially render any ransomware virus harmless.
The lAeSUZDqb Ransomware
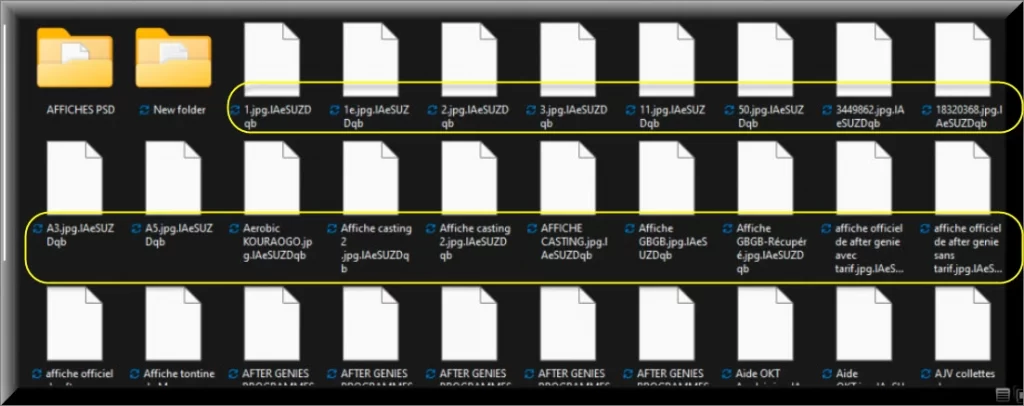
The lAeSUZDqb ransomware is the suffix that you see at the end of each of the encrypted files. The lAeSUZDqb ransomware prevents any software form recognizing the file format and therefore reading the data.
SUMMARY:
| Name | lAeSUZDqb |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Detection Tool |
Remove lAeSUZDqb File Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt lAeSUZDqb files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Hello.
I wanted to ask you through this message for help if you can.
I, who am writing to you, am a blind person/can’t see.
2 month ago, I formatted my PC with Windows 10.
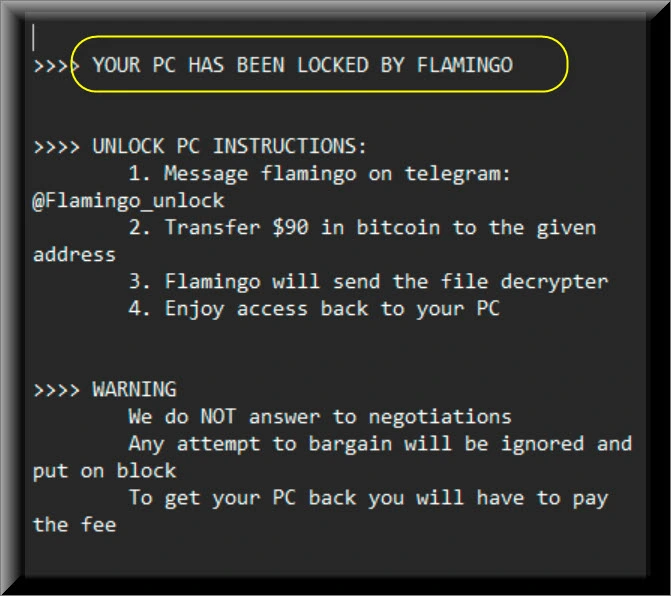
when I was trying to install a crack in a software, a ransomware called flamingo entered my PC and encrypted most of my necessary files, too
created a txt file in each folder.
in this txt file, when I open it, it instructs me to pay money to return the PC as before.
Do you know any solution to restore the documents by removing the second suffix with a decryptor?
the second suffix placed on the file is: .lAeSUZDqb
I also reformatted it to remove the ransomware, but I saved the encrypted ones on another external ssd.
Hi alban
Sorry to hear that, as far as i know there is no official decrypting tool for this ransomware, but you can check these here.