Lezp
Lezp is a ransomware representative aimed at encrypting user files and keeping them hostage for a ransom. The creators of Lezp are criminals who use blackmail tactics to extort money from their victims.
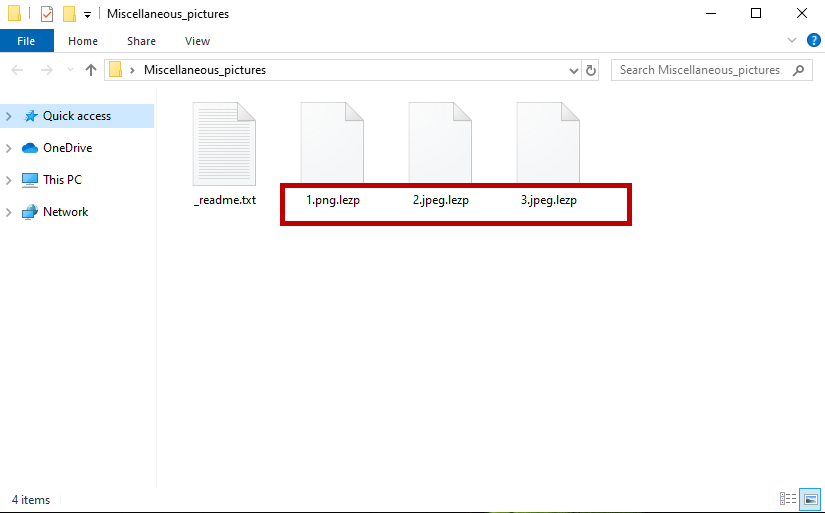
The Lezp virus will encrypt your files and leave a message in a _readme.txt file.
Immediately after Lezp applies its encryption code to the files that are stored on your computer, the hackers behind it place a notification on your screen and ask you to pay a ransom (typically in Bitcoins). The notification may come in the form of a .txt file, a pop-up or an on-screen banner and contains instructions on how to transfer the money. A deadline is also given, after which, the crooks threaten to leave the encrypted files inaccessible forever. Those who fulfill the ransom demands, however, are promised to receive a decryption key which can reverse the applied file encryption. Sadly, if such a key exists, there is no guarantee that it will really work, let alone that the hackers will give it to you. That’s why if you don’t want to send money to anonymous cybercriminals in vain but still want to remove Lezp and try to save some of your data, we suggest you to take a look at the information in the next paragraphs and the alternatives that we have described in the removal guide below.
The Lezp virus
The Lezp virus is a malicious piece of software that hackers use to extort money from online users by restricting access to their personal files and demanding a ransom. The Lezp virus sneaks in the computer through security vulnerabilities and applies encryption to the files stored there.
Usually ransomware versions like Lezp operate with absolute secrecy and you can barely notice them during the time they apply their file encryption. This is because, the encryption process, in general, is not a malicious process that destroys data or corrupts the system. Quite the opposite – this is a process that converts digital files into bits of data that cannot be accessed without a decryption key. The general use of the file encryption is for data protection, not for blackmail. Therefore, even if this process runs in the background of the system, most antivirus programs won’t consider it as malicious and won’t do anything to stop it or to notify the users about it.
The Lezp file encryption
The Lezp file encryption is a repetitive and sometimes very time-consuming process that runs in the background of the system. In some instances, the Lezp file encryption process may trigger symptoms such as significant system slowdown and higher CPU and RAM usage.
Sadly, once the file encryption process is over and the targeted files are encrypted, there is little that can be done to reverse the code that has been applied. Paying a ransom for a decryption key cannot guarantee that you will really recover your files. Trying other alternatives may also not be 100% effective because there is still no universal solution to ransomware threats like Lezp and their sophisticated encryption algorithms. What you can do, however, is to remove the infection and have a clean computer. Recovering files from system or personal backups is another possible solution. That’s why we encourage you to explore these alternatives and check out the instructions in the removal guide below.
SUMMARY:
| Name | Lezp |
| Type | Ransomware |
| Detection Tool |
Remove Lezp Virus File Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

I could not remove the virus Can you help restore a Word file I sent you on Please help me
Hi,Ola!Firstly, we advise you to complete the guide from the current page in order to remove the malware and clean your PC. Then, you can visit our How to Decrypt Ransomware article on this site and use the methods suggested in it to hopefully restore some of your data.The best thing to do is back those files up onto another drive for safe keeping until a decrypter becomes available.
i had used malwarebytes hitmanpro, and now spyhunter is remaining. many malware adware were removed by software now. main problem is how to decypt the impt files that i have on my pc like image , microsoft data excel word file, other database pdf how to decryot this file. i tried renaming file by removing lezp extension fromm file name but taht works only for audio and video file . while rest type of data are still in encrypt mode.
Hi nrj, our advice and the best thing to do is back those files up onto another drive for safe keeping until a decrypter becomes available.