Lightversionhotel.com
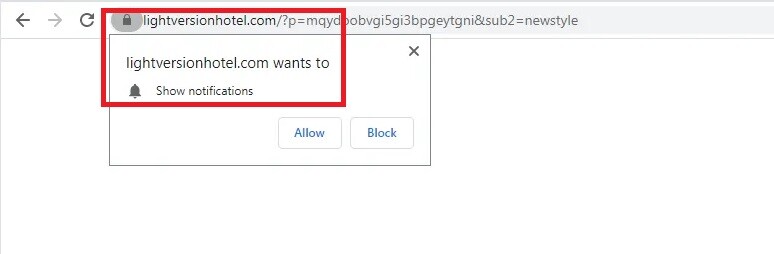
Lightversionhotel.com is a program that can initiate page redirects to sites that users may not have the intention to visit. In addition to that, Lightversionhotel.com may cover the main web browser’s screen with aggressive pop-up ads and banners that prompt users to click on various links.
The Lightversionhotel.com Virus will display pop up ads and messages
If some unusual and unwelcome changes have been taking place inside your default web browser lately, then you should check your system for the presence of one of the newest browser hijackers named Lightversionhotel.com. This program is a page-redirecting tool that is mainly used for online promotion. Aside from initiating redirects to some pre-defined sites, this program can also make modifications in the homepage URL or the main search engine of your web browser. It also can generate hundreds of annoying advertisements on your screen, open new tabs, display different supported alerts and promotional messages on the websites you visit.
You have come to the right place if you are looking for an optimal way of uninstalling those changes because, in this article, we have published a detailed removal guide that will help you remove all the strange modifications and ads from your browser.
How does a browser hijacker affect your PC?
A browser hijacker is a piece of software that isn’t a bad thing for you. It’s not a virus and even if its name sounds frightening, such software does not intend to harm the computer the way that a real virus or malware like a Trojan horse or a Ransomware infection will most probably do.
Browser hackers are normally designed to display a large number of promotional messages, ads, banners, and pop-up notifications on the users’ screen. But, the way they do that is a bit aggressive – essentially, they hijack the main browser by replacing the main homepage or the search engine with a different one which automatically redirects all the user searches to some sites and their promotional messages. This is part of a highly lucrative business model called Pay-Per-Click, which allows various online companies and developers to make a profit by collecting user clicks on paid ads. Apps like Lightversionhotel.com are just the software that supports such Pay-Per-Click models.
However, the browser hijackers often cause tremendous navigation problems and web browsing frustration to the users who have them in their system. The developers are of course after the money, and they are more than interested to show you as many paid ads every time you open your browser. That’s why they will typically set apps like Lightversionhotel.com to fill your screen with them. This is not illegal, but it may not be helpful to you either. You won’t get money out of the ads, as the clicks go into the developers’ pockets.
What you will get, however, will be an unstoppable stream of advertisements in the form of pop-ups, promotional banners, and nagging redirect prompts. To some people, this could be enough reason to become irritated to the extent where they want to uninstall Lightversionhotel.com. But that’s not all. Users should also take into account the use of malicious page redirect tactics and fake advertisements when deciding what to do with the browser hijacker because some of its ads may accidentally redirect to web locations full of dangerous viruses, Trojans, Ransomware and other nasty threats.
SUMMARY:
| Name | Lightversionhotel.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Lightversionhotel.com Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment