*Lloo is a variant of Stop/DJVU. Source of claim SH can remove it.
Lloo
Ransomware cyber threats such as Lloo are a widely-known category of malware programs. Lloo is developed with the sole purpose of allowing its creators to blackmail the malware’s victims.
Usually, ransomware is programmed to either block the screen of the infiltrated device or to encrypt the personal user data files stored inside the computer’s HDD. This divides the ransomware malware category into two main subclasses: screen-locker ransomware and ransomware cryptoviruses. The first one, the screen-lockers are considered to be the least advanced and less problematic sub-class of ransomware. These viruses usually generate a big banner or pop-up that is superimposed over the screen and thus prevents the user from interacting with anything on their device.
The hackers offer their victims to remove the banner but only if a certain amount of money is paid as ransom. However, it’s actually oftentimes possible (and, in many cases, not that difficult) to deal with such an issue manually without having to pay anything. The situation with the ransomware cryptoviruses like Lloo or Eijy is different. These threats are widely regarded as some of the worst kinds of malware you can get your machine infected with. They are highly advanced and successfully dealing with them and their effects on your PC and data it very difficult. As we already mentioned, cryptoviruses target the personal files of the user seeking to encrypt them.
The Lloo virus
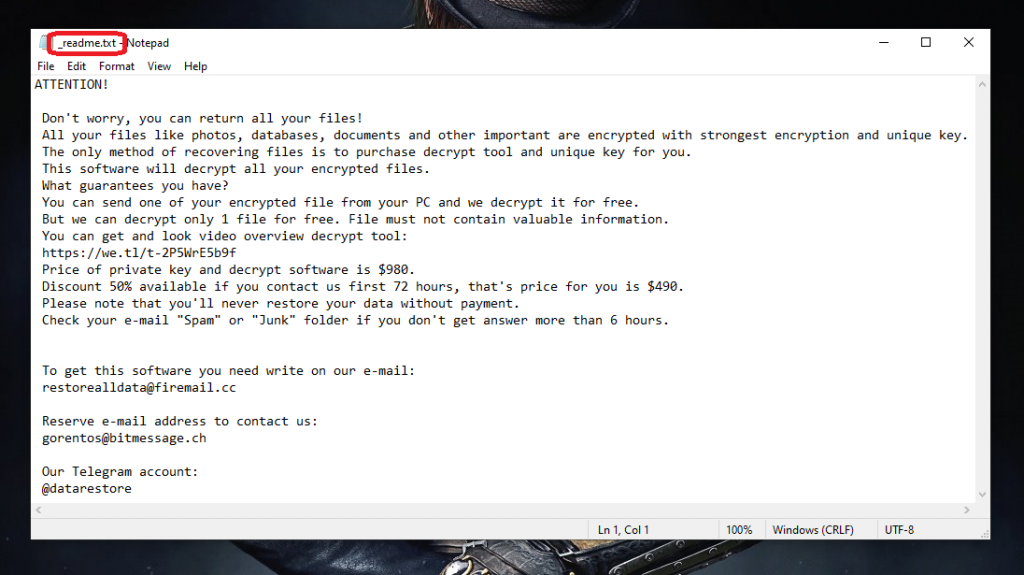
The Lloo virus is a good example of a ransomware cryptovirus. Similarly to other viruses of its class, the encryption used by the Lloo virus renders all targeted data inaccessible to the computer’s user and the only reliable way of regaining access to the files is through a special key that the ransomware generates.
However, the said key is possessed only by the hacker who’s responsible for the virus attack and it is this key that you are promised to receive provided that you carry out the demanded ransom payment. However, here is the moment where you should ask yourself whether or not it’s actually a good idea to trust some shady and anonymous cyber criminal with your money in hopes that they’d keep their promise and send you the needed decryption key. You need to understand that there are a lot of users who have been tricked into paying the requested money without getting the details needed for the decryption of their files.
If Lloo currently has your files locked, you might want to fist take a loot at all available potential alternatives and try them out before you actually consider transferring the money. For your convenience, we have put together a guide for removing Lloo and we have added to it some file recovery instructions which might help you get back some of your data. We have also included a professional anti-malware tool in the guide which you might find useful when trying to eliminate the cryptovirus. Sadly, however, we can’t guarantee that you will get your files back regardless of what course of action you decide on. Still, remember that the ransom option should only be seen as a last resort.
The Lloo file
Once in the infected computer, the Lloo file will normally show no symptoms and is also oftentimes able to bypass the security programs on most PCs. Sometimes, if the antivirus has a specialized ransomware detection feature, the Lloo file might be stopped immediately but this is oftentimes not the case.

Also, CPU and RAM spikes are two possible red flags that might give a cryptovirus infection away but, again, it’s all situational. Therefore, it’s simply better to ensure that your PC never gets attacked by such a malware piece. Normally, Lloo and other similar threats get distributed via spam social network messages and spam e-mails, shady and hazardous web ads, pirated software downloads, illegal or questionable sites and many other similar sources. The key is to avoid anything sketchy and obscure you might come across online and only go to reliable web locations. Also, never forget to back-up any important files that you might fear losing – a backup is the ultimate tool against a ransomware attack so always keep that in mind.
SUMMARY:
| Name | Lloo |
| Type | Ransomware |
| Detection Tool |
*Lloo is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Lloo Ransomware

The elimination of Lloo may require your undivided attention, much as the elimination of other ransomware versions. Additionally, the procedure of removing ransomware may require that the computer be restarted many times. That’s why, if you want to follow the instructions in this article from the very beginning to the very end, it is a good idea to bookmark this page in your browser, so you can easily find it later.
Performing a restart in Safe Mode is another stage in the preparation process. This step enables you to keep just the most essential programs and processes running, which makes it easier to identify malicious software that is wreaking havoc on your computer. If you need assistance with rebooting the system, follow these Safe Mode instructions and, once you are done, come back to this page.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Lloo is a variant of Stop/DJVU. Source of claim SH can remove it.
After you have restarted the computer in Safe Mode, go to the Processes tab in the Task Manager (launch it by pressing CTRL+SHIFT+ESC), and check for any processes that appear suspicious. Pay close attention to any processes that are utilizing a significant amount of your computer’s processing power or memory for no apparent reason. If you think a certain process could be hazardous to your computer, right-click on it, and then select Open File Location from the options that appear.

Once the File Location folder associated with the selected process opens, just drag and drop the files that are saved there to the free online virus scanner that is provided below in order to check them for malicious code:

If malware was discovered in any of the files that were scanned, you should immediately terminate the processes by right-clicking on it and choosing the option End Process. After that, clean the computer of the files and folders that were identified as potentially harmful by the scanner.
![]()
The Hosts file on the computer is often subjected to changes by malicious actors. Because of this, at this stage you will need to open the Hosts file and search for any malicious IP addresses that are listed under Localhost in the text. To do this, simultaneously hit the Windows key and the R key on your keyboard, and then copy and paste the following text into the Run command box:
notepad %windir%/system32/Drivers/etc/hosts
After that, you should click the OK button.
In the following image, we provide an example of strange virus creator IPs that you should look for in your file in the event that it has been hacked.

If you do not find anything troubling in your Hosts file, you may just close the window and go to the next step. If you do find anything troubling in your Hosts file, please let us know about it in the comments below.
If ransomware such as Lloo has attacked your computer, you can discover that specific settings in the System Configuration window have been altered, most notably the Startup tab. As an example, potentially dangerous startup items might be added to the list of items that the computer starts on boot up. To determine whether this is the situation with your computer, launch System Configuration by entering msconfig into the Windows search bar and click on the result that appears:

If there is anything in the list of startup items that raises a red flag, such as an entry with an odd name or a manufacturer that is unfamiliar to you, make sure its checkbox is not selected. After that, be sure to save your modifications and check that the list consists of just authentic items that have been checked with a checkmark.
![]()
*Lloo is a variant of Stop/DJVU. Source of claim SH can remove it.
When advanced malware infects a computer, it will often add malicious entries to the registry in order to increase its chances of staying longer in the system and making it more difficult for inexperienced users to remove it. That’s why, being a new threat, Lloo is not an exception, and it’s possible that it might have installed potentially harmful items in the registry of your computer without your knowledge. For this reason you will need to start the Registry Editor (to do so, type Regedit in the Windows search bar and hit Enter) and look for files that are associated with the infection in it. If you are not a trained expert and are unsure where to search for possibly harmful files, you may start a Find window by simultaneously hitting the CTRL and F keys, and then type the name of the ransomware into the box that appears on the screen. After that, all you need to do is hit the button labeled Find Next.
If any entries are discovered, they need to be removed very carefully. This is because, if you delete files that don’t have anything to do with the ransomware, your operating system can get affected. On the other hand, if you don’t remove all the registry entries that are connected to Lloo, there’s a chance that the virus may come back and infect your system again. That’s why it is advised that you use an anti-malware program that is able to check your computer and eliminate any potentially malicious files that may have been disguised or are still present on your computer. This application can do this by scanning the entire system.
Additionally, a manual search for entries connected to ransomware should be performed in the five locations listed below. To access any of them, just copy the following into the Windows search bar and hit the Enter key:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
If you find anything out of the ordinary in the locations that are listed above, it is advisable to scan them for malicious code and then remove the files and folders that are flagged as dangerous.
The temporary files associated with Lloo may be removed by entering the Temp folder, selecting everything included inside it, and then removing the selected items.
![]()
How to Decrypt Lloo files
After ransomware has been removed from a computer, the most pressing problem for those whose data have been encrypted is how to decrypt their files. Having said that, this is a problem that calls for extreme caution to be addressed.
It is highly recommended that you make use of a professional anti-virus program such as the one that is provided on this page in order to remove Lloo and other forms of malware. If you are absolutely convinced that Lloo has been entirely erased from your computer, then you should follow the method described below to retrieve your files.
The process of decrypting data that has been encrypted might be different depending on the variant of ransomware that has infected your computer. That’s why checking the file extensions of encrypted files is the first thing to do to determine the variant of the ransomware are you dealing with.
New Djvu Ransomware
STOP Djvu is the name of the most recent variant of the Djvu ransomware. Files encrypted by this variant typically end with the .Lloo suffix attached which makes it simple for victims to recognize that they have been infected with this particular threat. If this is your situation, then using this decryptor may help you to retrieve your lost data.
The STOPDjvu.exe file may be downloaded from the link above to by clicking the blue Download button that is located in the upper right corner of the website.
Once you’ve saved the file on the computer, select “Run as Administrator” before you press the Yes button to start the software on the computer. After you have finished reading the agreement and the short instructions and have clicked the Decrypt button, the process of decryption will begin. Remember that this decryptor cannot decode data that was encrypted using unknown offline or online keys.
Please let us know if the methods provided here are helpful to you, or if you have any difficulties while following our Lloo removal guide. It is important to keep in mind that you may eliminate the ransomware more quickly and save yourself some time if you use the anti-virus software that is included in this removal guide. Also, you can use the free online virus scanner that can be accessed via the provided link if you have any files that appear suspicious, and you want to check them for viruses.

Leave a Comment