Lockbit
Lockbit is a malicious computer infection that targets Windows systems with the goal to lock the most important files of their users. IT security researchers report that Lockbit is one of the latest additions to the infamous Ransomware virus category.
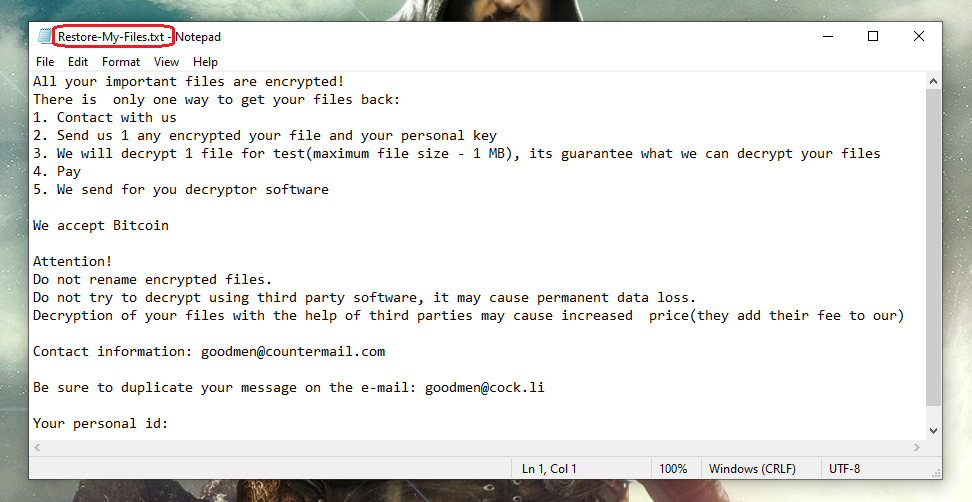
The Lockbit Ransomware will display this message in a .txt file.
This harmful computer threat is definitely something you should keep away from your computer, especially if you have some sensitive files stored on the machine. The problem with Ransomware is that you never realize it’s there until its job has been completed and now you are left with a bunch of inaccessible files and a ransom note on your desktop. Of course, if there are no important files on the attacked machine, the effects of the Ransomware will be nullified. However, one thing that must be mentioned here is that oftentimes threats like this one do not come alone. In many cases, the thing that brings the Ransomware into your system is a Trojan horse infection that has been disguised as something else in order to get you to download it. Once the Trojan gets in your computer, it “invites” the Ransomware in. In some instances, this is the only job of the Trojan, but there is no guarantee that there won’t be something else that it will do in your system once it delivers the Ransomware to it. Therefore, if you have been attacked by Ransomware, know that there may be another hidden threat in the system you don’t even know about.
The Lockbit Ransomware
The Lockbit virus is the latest addition to the file-locking category of malware known as Ransomware cryptoviruses. The Lockbit virus is tasked with taking its victims’ files hostage with the goal of asking for a ransom payment to release the files from its grasp.
The majority of experts in the field recommend not paying the ransom or to at least put it off until after you have tried all other possible solutions. We wish we could tell you there is a universal recovery method for your files that doesn’t involve paying the ransom, but there isn’t – depending on the situation, a given file-restoration solution may or may not work. This, however, is not to say that paying the ransom guarantees anything – quite the contrary. If you pay the money to the hackers, there is a significant chance that you may waste your money and fail to recover anything. The criminals behind the Ransomware cannot be trusted to send you the decryption key, which is why we advise you to not go for this option unless you truly have no other choice.
The Lockbit Decryptor
If you don’t have the Lockbit decryption key, it will be hard for you to deal with the Ransomware extension problem. There are some available Lockbit decryptor tools available mentioned in the removal guide below.
The Lockbit file extension is a short string of letters that get appended to the end of your files’ names. The Lockbit file extension doesn’t signify any regular data format and, therefore, can’t be recognized by your programs, but there may be other ways to circumvent this predicament and we will introduce you to some of them in our guide. Just remember to first complete the removal steps and only then try the ones related to file recovery.
SUMMARY:
| Name | Lockbit |
| Type | Ransomware |
| Detection Tool |
Lockbit Ransomware Removal
![]()
You may be required to quit your browser in some of the instructions below, that’s why before you continue, we advise you to Bookmark this page in order to quickly get back to it and complete the removal guide. Also, we advise you to enter your computer in Safe Mode in order to improve your chances for ransomware detection and deletion.
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
With the computer booted in Safe Mode, go to the desktop and press CTRL + SHIFT + ESC keys from the keyboard simultaneously. A new window called Windows Task Manager will open up. Go to the Processes Tab. There, you will see a list of processes that are running. Carefully search the list for processes that seem to be operated by Lockbit or look dangerous and unsual.

When you detect an unusual or a dangerous process, right-click on it and then choose the Open File Location option from the menu that pops up. Then use the free online virus scanner that is available here to scan the files in that location for malware:

When the scan completes and you see the results, end the processes whose files are infected by going back to the Processes tab, then go to the file location and delete the folders that contain the infected files.
![]()
Once you are sure that there are no more malicious processes running in the Task Manager, it is very important to check the Hosts file on your computer for signs of possible hacking. For that, press the Start and R keys from the keyboard. Then, copy the line below in the Run box that pops up:
notepad %windir%/system32/Drivers/etc/hosts
Click on the OK button and you will open the Hosts file on the screen. Scroll the text till you reach to Localhost. Then, check for strange IP addresses below Localhost. Normally, there shouldn’t be any unusual and unfamiliar IPs, but if there are, this may indicate that the computer is hacked.
The image here explains what you should be looking for:

Important! Please, write to us in the comments below this post if you find some suspicious-looking IPs below “Localhost” in your Hosts file.
Next, go to the Windows search field and type msconfig in it. Hit enter and this will open the System Configuration window on your screen:

The thing that you need to do there is to go to the Startup tab and remove the checkmark of the entries that seem to have a relation to Lockbit or look suspicious and have “Unknown” as Manufacturer. Be very careful here, though, and carefully check all the entries. Make sure that you leave the checkmark only for the ones that are legitimate.
![]()
Ransomware threats like Lockbit are known to make unwanted changes to the Registry. That’s why a very important step in the removal process is to open the Registry Editor (type Regedit in the windows search field and press Enter) and carefully search for entries that have the same name as the infection. The quickest way to search for them is to use the Find function of the Registry Editor (press CTRL and F together to open a Find box) and simply type the exact name of the virus. Then, click on the Find Next button and delete the results that are found with that name.
Attention! You may need to repeat the search action as many times as needed until no more results are found. Be very careful what entries you delete, though, as any deletions unrelated to the ransomware may be fatal for the health of your operating system.
Then, go manually to each of the following directories by typing them in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Check the directories for any recently-added entries that look suspicious. When you get to the Temp folder, remove all the entries that are found there.
If you happen to run into trouble or have any questions regarding any of the steps in the guide, we invite you to leave us a comment below this post so we can do our best to help you.
![]()
How to Decrypt Lockbit files
After you complete the steps above, and you are sure that you have removed Lockbit successfully, you may want to try some alternative file-recovery solutions that do not involve paying a ransom to some anonymous online crooks. Our separate file-decryption guide is specially created for that and can be found here.
Keep in mind, though, that to have success with the recovery of your encrypted data, it is important that the ransomware has been fully removed from the infected computer. If the steps above aren’t helpful, please use the recommended removal tool and scan your system with it.

When i click the start button before doing safe boot only ms paint is there can my be decrypted please reply
Hi Pruthviraj nagwade,
did you go through the whole guide step by step?
Hello my company system was attacked by ramsomware lockbit and all de company files are encrypted. Any help?
Thanks
Hi Carlos Lamas,
i would suggest to you to try the methods here