Lonkem
Lonkem is an application that can disturb the users’ normal web browsing activity by constantly spamming their browser’s screen with pop-up ads and page redirects. By default, Lonkem can change the main browser’s homepage and install a new search engine.
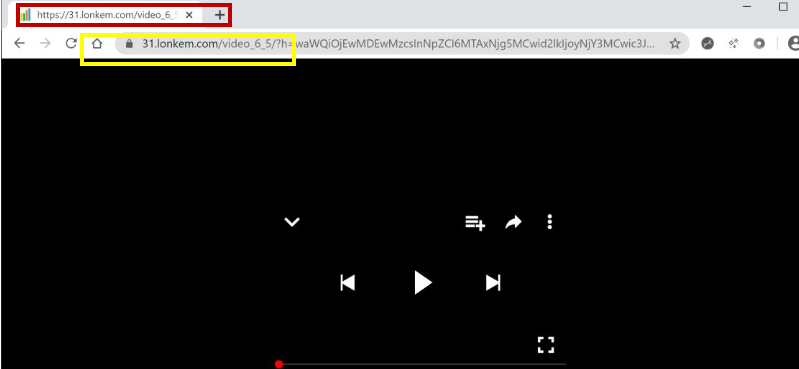
If you have recently noticed a significant change in the way that your Chrome, Firefox, Edge or Safari browser operates, then most probably, a potentially unwanted program called Lonkem could be behind the change. This program is known to modify the settings of any given browser and to install some new components such as search engines, new toolbars, redirect buttons, etc. Lonkem can also fill the screen with various sponsored advertisements, pop-up notifications, and page redirects.
Fortunately, the program you are faced with is not a malicious virus, Ransomware or a Trojan horse. That’s why you don’t need to panic. Lonkem is just a browser hijacker. However, you may still be interested in uninstalling it and regaining control of your web browser. That’s why we have prepared a removal guide below which will show you the steps that you need to take to safely remove the annoying program.
Lonkem.com
Lonkem.com is very invasive program, which can lead to very annoying modifications in your browser. The most upsetting thing is that Lonkem.com do not ask users for their agreement to these changes, which is the key reason why many people are so annoyed and want to remove such pieces of software as soon as possible from their systems.
Fortunately, programs such as Lonkem will not harm your system. They are not created for theft or malicious purposes but are rather used as instruments for online advertising. They simply advertise certain products, services or websites on your screen but use a very aggressive approach to do that. As you might expect, the explanation for this aggressiveness is money. Typically, browser hijackers display pay-per-click ads that generate income for their developers every time that users click on them. That’s why they are often so intrusive.
There may, however, be some unwanted effects of browser hijackers that can give you good reasons to uninstall them. For instance, while your system won’t get destroyed by a browser hijacker, it could slow it down considerably. Lonkem could use a lot of CPU and RAM resources in order to load its dozens of pop-up messages and promotional pages, thereby affecting your machine’s performance. The hijacked web browser can also stop responding to your searches and redirect you to dozens of new websites. This can often lead you to an unknown web location where questionable adverts and deceptive links can easily infect you with malware or a virus such as Ransomware or a Trojan horse.
So, if this possibility is something that worries you and you think it’s just not worth the risk of bumping into a computer threat due to an invasive promotional program like Lonkem, please follow the removal guide below or use the professional software to uninstall this hijacker once and for all.
SUMMARY:
Remove Lonkem
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Reply