Look-this.site
Look-this.site is a rogue Windows application that looks like a browser extension but is closer to a browser hijacker. Look-this.site installs in Firefox, Chrome, Edge, and other popular browsers, replaces their default search engines, and starts spamming them with aggressive advertisements and page-redirects.
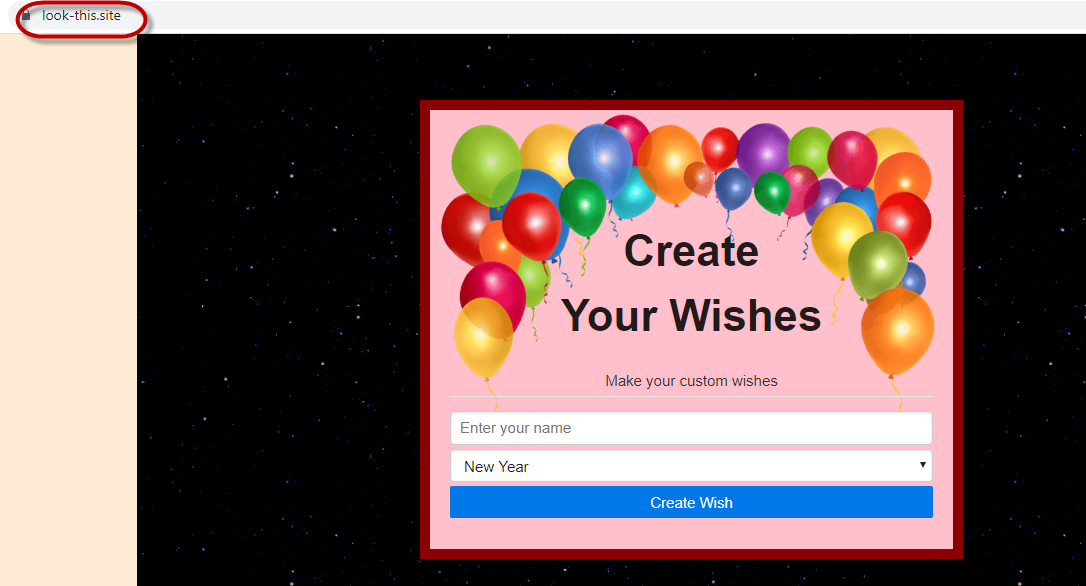
The Look-this.site virus display message like this
If you have been visited by this app and it is currently tampering with your browser’s settings, you will most likely need our help in order to deal with it and bring back the regular settings of your browser. Hijackers like Look-this.site can be particularly irritating to have in your browser as they can shower your screen with aggressive banners, pop-ups, misleading links, and promotional messages as well as change the homepage address of the infected browser and alter its toolbar. However, as unpleasant as they are, most hijacker apps are not actually intended to harm your system or do anything bad to your files. Though some users and researchers may refer to them as viruses, a hijacker is nowhere near as dangerous as a virus program of the Ransomware, the Trojan Horse, the Spyware, or of some other category of highly-malicious programs. Even though Look-this.site isn’t the safest app you can have on your PC, any potential danger that may be related to it is indirect and is more of a by-product of its activities rather than an actual programmed purpose of the app.
Look This Site
As we said, Look This Site isn’t intended to cause any sort of harm in the system, but it can certainly make some unwanted changes in the browser and even in the system Registry. Those changes are introduced in order to make the system’s main browser predisposed to ad-generation and automatic page-redirection.
However, those changes may also serve as vulnerabilities that more dangerous threats like Ransomware or Trojans may exploit in order to infect your system. Also, even though most hijacker ads should be harmless, there’s simply no way of knowing if there aren’t any unreliable or misleading adverts among the stream of safe ads. Usually, there isn’t much control over the sources of the displayed ads, meaning that some of them may indeed be linked to hazardous or illegal sites. What’s even worse is the fact that there are many phishing pages out there that very closely resemble legitimate and popular sites and landing on one such page may get you tricked into providing some very important and sensitive personal information that can later be misused by online scammers. Therefore, if you don’t want to risk getting tricked by some phishing page or if you don’t want to potentially get your PC exposed to Spyware, Ransomware, Worms or other similar threats, it is best to make the uninstallation of Look-this.site the first thing you do once you finish reading this article. The guide that we will now present you with includes all the necessary steps you must follow to uninstall Look-this.site and fully remove all data related to it from your computer.
SUMMARY:
| Name | Look-this.site |
| Type | Browser Hijacker |
Remove Look-this.site WhatsApp Virus
We are sending you to another page with a removal guide that is regularly updated to counter the latest tricks malware creators use. It will show you how to:
1. Locate and clean up your phone’s apps if they are infected.
- Find browser extensions related to the threat and how to remove them.
- Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment