*Source of claim SH can remove it.
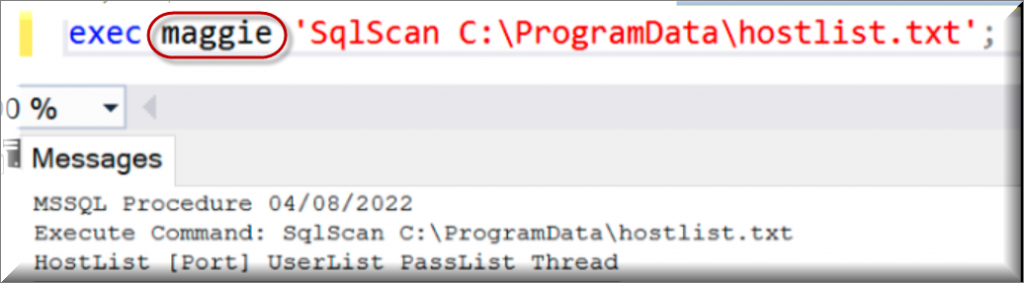
Maggie Malware
Maggie Malware is malicious piece of software that falls in the category of Trojan Horses. If you suspect that Maggie Malware has infected your computer, please read the following information carefully.
This article’s goal is to provide you and other victims of Maggie Malware with knowledge that will be useful in eliminating the danger. We’ll also cover several ways you can protect yourself from getting the same virus again. If you’d rather remove Maggie Malware manually, we’ve created a detailed guide to help you do so. A professional removal program may be found further down the page for those who would prefer to remove the virus automatically.
Trojan infections are a major threat to any computer. After infecting a system, it is typical for them to linger around for quite some time because they may compromise the machine without causing any visible signs. And what is worse, you have no way of knowing how much harm they might cause or where they could be hiding in your system.
Even experienced computer users might fall victims to a Trojan like Maggie Malware and Altruistics. These threats pose major risks to the system and must be eliminated without a delay. You may become a target of many forms of harassment because Trojans are able to spy on you and steal sensitive information about you, your personal life, your online profiles, your place of employment, your banking details, and other data. It’s possible that threats like Maggie Malware may track down your keystrokes and read almost everything you type into the compromised computer. In this way, the crooks behind the Trojan may gain access to details that reveal your identity or financial status.
Data deletion is yet another way for Trojans to cause harm to their victims. They may do this in two ways: selectively, by erasing certain files, or by crashing the entire system. Furthermore, your hacked computer may be used to distribute viruses and spam to other computers.
Trojans are particularly dangerous because they often serve as entry points for other viruses and malware, most notably ransomware. Because of this, you should be very careful with Maggie Malware and promptly remove any related data from your hard drive. After that, you should do a thorough system check to ensure that no other infections have remained on the computer.
Instead of waiting to see what damage the Trojan may cause, it’s better to take immediate action to get rid of it. Prevention is also very important and should be taken seriously by anyone who is using a device connected to the Internet. One way to keep Trojans like Maggie Malware at bay is by using the most recent versions of your antivirus software and operating system. Avoid using out-of-date software to keep your computer safe from external attacks aimed at known vulnerabilities. In addition, stay away from sketchy web locations that could be used to distribute questionable content. These typically include low-quality sites, non-reputed downloadable platforms, e-mail attachments from unknown senders and spam. The best advice is to use extreme caution and critical thinking before engaging with any content on the internet that doesn’t look reliable, and invest in a trusted antivirus program that can keep your system safe.
SUMMARY:
| Name | Maggie Malware |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Remove Maggie Malware
If you are looking for a way to remove Maggie Malware you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for Maggie Malware and any other unfamiliar programs.
- Uninstall Maggie Malware as well as other suspicious programs.
Note that this might not get rid of Maggie Malware completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


*Source of claim SH can remove it.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment