MainCaptchaNow.top
MainCaptchaNow.top is a browse-redirecting and site-promoting tool that changes the settings of the users’ browsers without permission and causes the generation of obstructive ads. MainCaptchaNow.top also frequently page-redirects the browsers to various sites, some of which may not be safe.
Our goal within the next lines will be to help you deal with an annoying software component for browsers like Chrome and Firefox by removing it from your system in case it is causing disruptions while you are browsing the Internet. Some of the “abilities” of this app is to redirect the users to various pages on the Internet and to show ads in their browsers. Additionally, it may install a new search engine service in the browser, replacing the previous one, as well as change the address of the homepage and the address of the new-tab page. It is likely that these changes would be advertised as useful for the user. In fact, MainCaptchaNow.top is probably going to be promoted as a useful add-on for the browser that would make one’s web experience more pleasant and safer. However, one thing to note here is that the changes may be quite invasive and you may not be able to opt-out of them or to cancel them once they have been imposed unless MainCaptchaNow.top gets uninstalled. Also, the random popping-up of ads, banners and page-redirects on your screen while you are trying to find something on the Internet could also be quite irritating, to say the least. Not to mention that the new search engine or the homepage that has been set as default on your browser by the annoying app are likely not going to be anywhere as useful as advertised. In fact, they may make it quite more difficult for you to actually find what you are looking for on the Internet. All of this leads us to the conclusion that MainCaptchaNow.top, Fast Captcha, Main Captcha Top and Main Captcha Now Top, are nothing more than another representatives of the well-known category of potentially unwanted software known as browser hijackers. In case you’d like to find help with removing the hijacker, you can find it in the following list of instructions.
One more thing…
A very important aspect regarding the apps of the browser hijacker category like MainCaptchaNow.top is that, while they are not as dangerous as Trojans, Ransomware and other similar infections, they are not software that we would advise you to put your trust it. The issue here is that you won’t really have a say in what advertising and commercial content gets brought to your screen by the hijacker. Usually, such apps try to access your browser history and cookies and determine what ads you may be interested in but there’s nothing to say that the algorithm of the hijacker won’t determine that you need to be presented with ads from unreliable sources. And if this happens and you click on some sketchy ad that is linked to a dangerous site, you could get all kinds of nasty infections and malware in your computer. We already mentioned the Ransomware and the Trojan Horse threats but you should know that these are only two examples of the many malware programs that you could encounter if you are not careful with what content you interact with while online.
SUMMARY:
| Name | MainCaptchaNow.top |
| Type | Browser Hijacker |
| Detection Tool |
Remove MainCaptchaNow.top Virus
If you’re not acquainted with browser hijackers, it may be tough for you to uninstall MainCaptchaNow.top, but the simple instructions listed below should make it easier to do so:
- If your browser has been hijacked, open it and click on the main menu icon to get back in control of it.
- Next, choose More Tools (or Add-ons).
- The next step is to locate and open the Extensions tab.
- All currently installed extensions will be shown in the browser’s extension list. Click Remove/Trash Bin next to the MainCaptchaNow.top extension to get rid of it.
- If you don’t see MainCaptchaNow.top, but you believe other extensions are interfering with your browsing experience, know that you can remove them without any risk for the normal operation of your OS.
- After that, open a new tab and do some browsing to observe how the browser responds.
If intrusive pop-ups and warnings persist in your browser after removing any extensions you think are hijacker-related, you may need to search for and remove any additional potentially unwanted components that may have been installed on your system using the comprehensive steps below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

To begin, save this page as a bookmark in your browser so you won’t lose it. This will come in handy when need to go back to the instructions again after a system restart,.
Speaking about a restart, in order to proceed with the MainCaptchaNow.top removal, we recommend that you restart your PC in Safe Mode (please click this link for more instructions).
Restart your computer according to the instructions from the link and then follow this removal guide’s steps to complete the MainCaptchaNow.top removal.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
This step requires you to identify and terminate any background processes, related to MainCaptchaNow.top, that are currently active on your PC.
Press CTRL+SHIFT+ESC to open the Task Manager, and then select the Processes tab to see what’s running (the “Details” Tab for Windows 8 and 10).
Right-click on any hijacker-related process and select Open File Location.

After that, you may use the powerful online virus scanner shown below to look for hijacker-related code in the files created by that process.

This will tell you whether you need to stop the process and delete the folders that contain hijacker-related files. To stop a dangerous process, right-click on it in the Processes tab and select End Process.

In the third step, open your Control Panel (From the Start menu) and go to Programs >>Uninstall a Program to eliminate MainCaptchaNow.top from your list of installed programs.
Go through the list of programs on your computer and look for any that were just installed. Uninstall MainCaptchaNow.top if it appears in the list. You should also uninstall any freshly installed apps that you suspect are infected with the hijacker.
Once you’ve completed that, go to the bottom-left corner of the screen and choose the Start button. Type msconfig in the search bar and press Enter. When you’re done, you should see a new window called System Configuration on the screen. Click the Startup tab to check if MainCaptchaNow.top has been added there.
Disable the startup items that you think are linked to the browser hijacker by removing the tick from their checkboxes, and then click OK to save your changes.


To check for unusual changes and signs of hacking, such as new IP addresses, open your computer’s Hosts file.
Use the Windows+R keyboard shortcut and paste the following text into the Run dialog box to speed things up:
notepad %windir%/system32/Drivers/etc/hosts
Then click OK, go to the Hosts file and find Localhost in the text. It should be somewhere at the bottom of the page. Under Localhost, check if any strange IP addresses have been added without your knowledge or approval.

Please let us know if you see anything unusual in the comments below so we can look into it.
Next, close the Hosts file and use the following steps once you’ve opened Network Connections (search for it by using the Start menu’s search bar).
- Select Properties by right-clicking on the network adapter presently in use.
- Select Internet Protocol Version 4 (ICP/IP) from the Properties window.
- Click on Advanced once you’ve set the DNS to Obtain DNS Server Automatically.
- Open the DNS tab in the Advanced box, then make sure you’ve removed everything that’s been added there as rogue DNS. Then click OK to apply the changes.


Here’s how to undo any browser modifications that may have been done by MainCaptchaNow.top to your browsers without your knowledge. These steps should be performed on all installed browsers on your computer, regardless of how often you use them if you want to stop the MainCaptchaNow.top invasion once and for all.
Locate and right-click on the shortcut icon of your web browser.
To get started, hover over the pop-up menu that appears on the screen, and then choose Properties.
Note: The sample images below show Google Chrome, but the instructions are the same for Firefox and Internet Explorer (or Edge).

In the Properties window and choose Shortcut from the top menu with different tabs. Pay attention to the Target section and if you notice that anything has been added after .exe, remove it and then click “OK” after you are finished.

![]() Remove MainCaptchaNow.top from Internet Explorer:
Remove MainCaptchaNow.top from Internet Explorer:
Open IE and click the gear symbol in the upper-right corner of the browser window to access the Manage Add-ons menu.
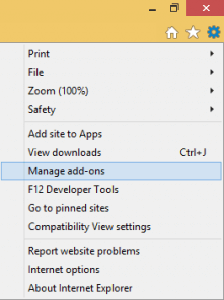
In the Add-ons window, look for and remove the browser hijacker if you see it there.
The next step is to click the gear symbol once again and then choose Internet Options from the menu that appears. If you don’t like the URL of the home page, make sure you change it. Click “Apply” once you’ve entered the URL you want for your default home page.
![]() Remove MainCaptchaNow.top from Firefox:
Remove MainCaptchaNow.top from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.
Start the browser and click the Firefox menu button in the upper-right corner of the screen. Then, select Add-ons and open Extensions from the menu on the left side of the screen.
Use the “Remove” button next to any extensions you suspect are interfering with your browser’s functionality to get rid of them and check if your browser returns to normal once you’re done.

![]() Remove MainCaptchaNow.top from Chrome:
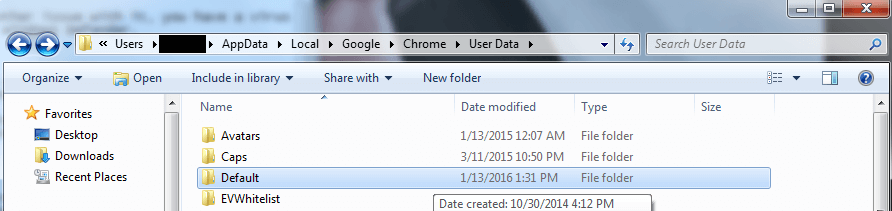
Remove MainCaptchaNow.top from Chrome:
First, close Chrome so that you may get rid of the MainCaptchaNow.top extension.
Then, open Computer and navigate to: C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data.
That’s where your Google Chrome user data is located.
You should rename the “Default” folder in User data to “Backup Default“. Then, restart Chrome and check to see whether the hijacker has been removed.

Browser hijackers have been known to make changes to the registry to help them stay in the system for as long as possible. Therefore, in the guide’s sixth step, we’ll show you how to locate and delete system registry entries linked to hijackers.
To begin, enter Regedit into the Start menu’s search box and press the Enter key. A window for the Registry Editor will appear on your screen immediately after you do that. You may use the Find dialog box to look for the hijacker’s name by pressing CTRL+F at the same time and typing MainCaptchaNow.top in it. Look through the registry for any matches and delete everything you discover.
If you get no results from your search, use the left panel of the Registry Editor to go to the following three locations:
- HKEY_CURRENT_USER—-Software—–Random Directory. You can ask us in the comments if you can’t decide which directories are related to the hijacker.
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
Look in each of the directories listed above for anything with a strange-sounding name. If you discover files or folders connected with MainCaptchaNow.top, you must be very cautious while deleting them.
Attention! If you’re not sure which files and folders in the registry are associated with the browser hijacker, leave them in place. In order to avoid accidental system harm, please use the powerful malware-removal program we’ve referred to on this page, our free online virus scanner, or another trusted software of your choice.

Leave a Comment