Makop
Makop is a ransomware infection that is specialized in encrypting valuable user files and keeping them inaccessible until a ransom is paid. Makop sneaks inside user devices with the help of a Trojan horse, system vulnerabilities or compromised web content.
The file-encrypting Ransomware infections are nowadays some of the most harmful computer threats that users may encounter. The worst thing about them is that the digital files they have encrypted may not be recovered, regardless of what you do. However, the victims of Ransomware should always try to explore all the alternatives that are available in order to minimize the damage and restore any information that can be restored.
Our focus in this article is to help users deal with a cryptovirus named Makop. This new infection of Ransomware has been attacking an increasing number of web users lately. That’s why, our goal in the next lines will be to give readers helpful information about how the virus works, what distribution channels it uses and what you can do to remove it. We also have prepared a set of removal instructions that can support those of you with Makop in their system to remove the malware and possibly get some of their files back without any money being paid to anonymous cyber criminals.
The Makop Ransomware
The Makop virus is malware of the ransomware class that can encrypt digital files and blackmail the owners of the files to pay ransom for them. The victims who have been infected with the Makop virus may not be able to access their information, use their computer and store data on it unless they remove the ransomware.
The hackers who are in control of the infection normally offer a special decryption key to their victims, which can restore all files to their original state. However, they demand a ransom payment in order to send it. The required ransom money in some situations may range from a few hundred bucks to a couple of thousands. However, payment of the money may not be a good solution, because the promised decryption key may not be available to the victims even after they pay the required ransom. As soon as the crooks receive the money, they may not send it and may disappear. Or, they may try to ask for another ransom payment and keep threatening you about the future of your files. That is why we would recommend our readers to take the alternative approach and remove Makop with our instructions instead of sending money to some crooks. After they successfully clean the computer, they can try some of the possible file recovery options listed in the removal guide below.
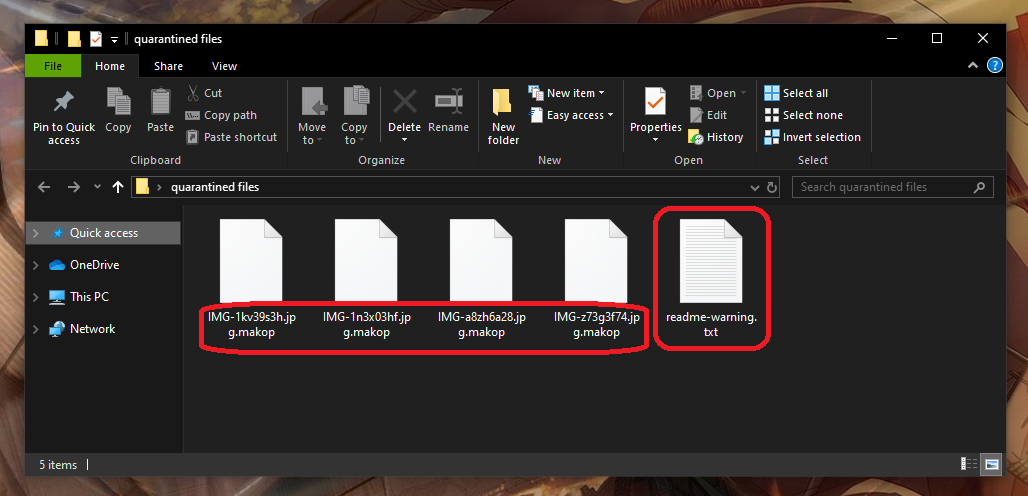
The Makop file encryption
The Makop file encryption is a method used by cybercriminals to restrict access to user files. The Makop file encryption prevents anyone from opening and using the encrypted information unless they have a working decryption key.
As we explained above, however, it may not always be possible to obtain such a key. This should not discourage you, though, because if you manage to remove the ransomware from your system, you may still be able to recover some of your files by alternative means or use personal backups to copy them back on the computer.
SUMMARY:
Remove Makop Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Reply