This page aims to help you remove Mamba Ransomware for free. Our instructions also cover how any Mamba encrypted files can be recovered.
In the article below we are going to tell you everything about Mamba Ransomware – also known as HDDCryptor. This program is extremely malicious and may become the reason for the encryption of many files, which are very important to you.
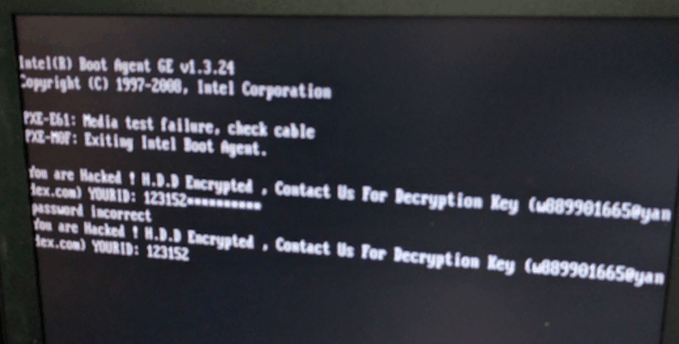
“You are hacked! H.D.D. Encrypted” is the trademark opening statement of the Mamba Ransowmare.
What exactly is the Mamba Ransomware?
Ransomware-based programs are extremely dangerous and malicious. This is one of the fastest developing types of viruses in the world. There are various subtypes of Ransomware:
- Mobile-based Ransomware – these programs attack mobile phones, lock their screens up and then demand ransom for making the screens accessible to the victim users again.
- Monitor-locking Ransomware – what is typical of this subtype is the fact that no files are really encoded. Such a program resembles the mobile Ransomware, but works on computers. Only the screen is locked and then ransom is wanted for unlocking it.
- Government-exploited Ransomware – some state security agencies use Ransomware-based programs to fight cybercrime, for example, or violation of copyright policies. The program would lock up the criminal’s computer and a fine will be required for decoding it.
- The famous file-locking Ransomware – this is the most widely spread type of viruses. The ones of this subgroup infect your PC, collect data about the files you use most and then encrypt them, most usually with a double key. This key’s two parts are different – the Public one you get right after the process of encoding your files has been finished. For the second component the hackers, who are attacking you, want ransom and you get a special alert notification on your screen letting you know, how and in what currency you should pay. There could even be a specific deadline stated.
- HDD-encrypting ransomware – these viruses usually target your HDD, changing the Master Boot Record so that you are not even able to boot your PC into Windows
What type of threat does Mamba Ransomware belong to?
Mamba is an example of HDD-encoding Ransomware. This subgroup’s members usually enter your PC with the assistance of a Trojan horse virus. The Trojan is the one who ensures the safe passage and once both viruses have finally gotten inside your system, they may proceed with their further plans and intentions. Mamba, for example, starts the actual encryption process after carefully defining which files exactly are used most frequently. Then all of them get locked up. The Trojan, on the other hand, stays hidden until the moment comes for the implementation of its own plan. If you want to learn more about Mamba you can check out the report by KasperskyLabs.
What might work in the fight against such a virus?
Sadly, the truth is such a version of malware is extremely difficult to be counteracted. The affected user may need special advice or tips from a professional or the help of an extremely powerful anti-malware tool to win such a battle against Mamba Ransomware. What is even more disturbing is the fact that even paying the requested ransom may not be what it takes to set your encrypted files free. The hackers might just run away with your money and leave your encoded data inaccessible forever. That is why we recommend that you don’t choose to immediately pay the demanded sum. What we can advise you to do is to try to cure this awful contamination with the help of other means – software, tools, tips or the assistance of experts. Try everything before you proceed with giving your money to criminals, because paying them might even be considered a crime.
For instance, you may try to save your files and destroy the infection via using our own Removal Guide on this page. We do not promise that these tips will help you decrypt your files, but they will certainly help remove Mamba. Either way, it doesn’t hurt to try as you lose nothing. Another possible decision which is rather wise is to go and see a professional who has dealt with similar infections. Such experts could be of great help because they may have their own know-how. What else you could do is to purchase a specialized anti-Ransomware program but only after consulting someone in that area for advice.
The only guaranteed solution
The only solution that guarantees a complete success in the fight with Ransomware is preventing it. Prevention should become your daily routine. There are some general tips we could share with you. First of all, avoid the possible sources of Ransomware – do not authorize any macros in any document that has come to you from the web. Stay away from email from unknown senders – do not open them or download any of their attachments. Also, scan your PC regularly to avoid even more cyber threats. And the essential advice when it comes to Ransomware: please learn to keep copies of your important data. Back up as many of your important files as you can, as Mamba Ransomware targets files and if you have copies stored on a separate drive, no one will be able to blackmail you.
- Insert the DVD (or the USB) into the computer, then run the computer and choose to boot the OS from the DVD/USB. You may have to change Windows boot priorities from the bios by pressing Del
- When Windows boots from the DVD/USB select Windows Repair
- Open the Command Prompt and write the following commands inside: enter: bootrec / fixmbr, bootrec / fixboot and bootrec / rebuildbcd
- Your Windows OS should now be able to boot normally. You can proceed with the removal of the virus as usual.
SUMMARY:
| Name | Mamba |
| Type | Ransomware |
| Detection Tool |
Mamba Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

hi, I did all the instructions on how to recover from Mamba. But still the disks are encrypted and I cant access them nor get into safe mode.
Kindly advise since this solution does not work.
Hi Imo, were you able to repair the master boot record (MBR) as written in the first step?
Hi Imo,
this is a guide on how to remove the ransomware from your system. On Step 5 you can visit the link on how to decrypt your files or use the software we provided there. Mamba is still a new kind of ransomware and researchers are still trying to find a way on how to devrypt the files. So i would suggest to you to check this link https://howtoremove.guide/how-to-decrypt-ransomware/ once in a while to see if there is a decryptor for Mamba encryption.
You are most welcome Imo 🙂
Did you check our article on How to Decrypt Ransomware?