Mapsanddrivingdirections.com
If you have recently noticed unpleasant activities occurring in your browser such as random redirects to unknown sites and webpages as well as different intrusive ads getting streamed to your browser screen, then you are probably dealing with Mapsanddrivingdirections.com or any other potentially unwanted application (PUA) of the browser hijacker category.
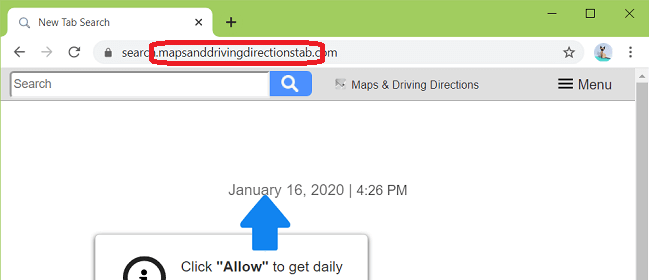
The Mapsanddrivingdirections.com virus will redirect your browser.
Aside from the ads and page redirects, it’s also likely that a hijacker tries to make certain alterations to the browsers that you use (Internet Explorer/Microsoft Edge, Opera, Firefox, Chrome or any other). Such alterations may include replacement of the starting page and the new-tab page of the browser, replacement of the default search engine, different modifications made to the toolbar of the browser and other similar modifications. Normally, a hijacker wouldn’t really ask for your permission in order to impose the changes. Also, in most cases the said changes don’t really give you anything useful and are typically seen as unwanted as they mostly serve the needs of the hijacker when it comes to streaming ads to your screen. For example, the newly imposed search engine that your browser has received might give you modified search results for each of your searches. That way, you might land on pages brought to you by the new search engine that aren’t really the ones that you have been looking for and are instead web locations that the hijacker app is supposed to promote. It’s likely going to be the same with your starting page and new-tab page – they would probably be of sites that the pesky software on your browser is supposed to advertise.
Potential dangers
Of course, some of you might say that this isn’t a big deal – after all, it’s not like the Mapsanddrivingdirections.com is some kind of insidious Ransomware or Trojan Horse virus. However, while it is true that most hijacker apps are nowhere near as harmful as real computer viruses like the ones mentioned above, it is still within the realm of possibility that a browser hijacker could indirectly expose your machine to certain security risks. Such a risk could be any of the ads or page redirects that might get streamed to your screen while you are browsing. If a certain ad that isn’t reliable or safe gets displayed on your screen and you click on it, you could easily end up having your machine targeted by different malware threats the likes of Spyware, Rootkits, Worms and, of course, Ransomware and Trojan Horse viruses. Therefore, we strongly recommend you take away Mapsanddrivingdirections.com or any other hijacker that might be currently residing on your computer as this will surely make your computer much less likely to get infiltrated by malware. Something that needs to be pointed out here is the fact that it is usually somewhat tricky or at the very least non-intuitive to remove a hijacker since most such apps lack built-in uninstallation options. Therefore, anyone who wants to get rid of an app such as Mapsanddrivingdirections.com would need to resort to a bit more advanced methods. There are typically two effective courses of action in this case. The first one is to manually locate any data related to the unwanted hijacker that’s on the computer and remove it from there. On this page, we have posted a set of instructions to guide you through the process of manually removing the unwanted app. However, if you don’t’ think the manual method is for you, know that there’s also the automatic one – using a trusted specialized removal software could also help you eliminate a hijacker like Mapsanddrivingdirections.com. Such a software tool has been included in the guide from this page so know that you can use that as well when trying to remove the hijacker app from your machine.
How can a hijacker get to you?
If you open a shady e-mail and click on its attachment, if you download some sketchy file, if you open some questionable online ad or offer and if you visit some obscure and unreliable site, you could easily land a hijacker on your PC. The same could also happen if you install some new program (especially if it is freeware) on your PC using the Quick setup configuration. Bear in mind that it is always better to go for the Advanced setup settings if such are available as they could allow you to see if some unpleasant app like Mapsanddrivingdirections.com has been bundled with the program you’re trying to install. If you ever see something like that, be sure to uncheck it before you continue as this will prevent the potentially unwanted software component from getting installed on your machine alongside the main program.
SUMMARY:
| Name | Mapsanddrivingdirections.com |
| Type | Browser Hijacker |
| Detection Tool |
Mapsanddrivingdirections.com Pop-up Ads Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment