This page aims to help you remove the .Meds Virus for free. Our instructions also cover how any .Meds file can be recovered.
.Meds
.Meds is a ransomware of the DJVU/Stop ransomware strain. Its sole reason to exist is to extort money from victims in the form of bitcoin payments.
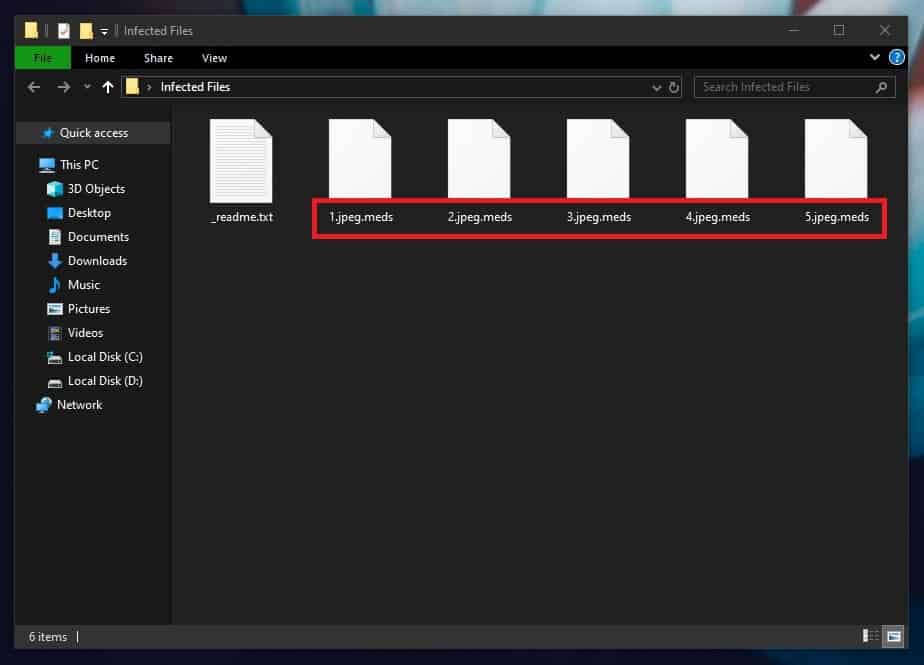
The .Meds Virus will encrypt your files
Ransomware viruses are feared computer threats. Their numbers have been rapidly increasing, and new sophisticated infections have been targeting the computers of unsuspecting web users. One of these new Ransomware variants is called .Meds, which is an example of what is also known as a cryptovirus. This infection typically causes harm to its victims by applying a secret encryption to their files in order to allow the hackers behind the threat to blackmail the users for the access to the sealed data. The placed file-encryption is considered so difficult to remove that the victims often see no other option but to pay the demanded money with the hope that they will regain access to the affected files.
Luckily, there are other alternatives which don’t involve paying a ransom to some anonymous hackers, and in the next lines you will learn more about them. Below, we have published a detailed removal guide, with the aim of helping those affected by .Meds. The removal guide contains manual steps and a professional removal tool as well as a section with instructions on how to potentially recover some of your locked files without paying a ransom.
The .Meds virus
The .Meds virus is eponymous with the file extension, but its real name is DJVU. The .Meds virus is just the latest of the DJVU ransomware to sweep the internet.
Ransomware viruses like .Meds, Seto, Moka have a set of traits that ensure they secretly infect the system and perform the malicious action they have been created for. One of them is their stealthiness. Such infections are able to avoid detection from the majority of antivirus programs. The reason is, the file-encryption they use is a process that is neither malicious, nor harmful or damaging in any way. What the encryption does is, it simply makes the files stored on the system inaccessible without the application of a special decryption key. The problem is that you don’t initially have that key and the only people who possess it are the cybercriminals behind the Ransomware. In order to obtain it, you are supposed to pay the demanded ransom sum.
The .Meds file extension
The .Meds file extension is an encryption that takes over files and appears only when the file is fully locked. If you don’t see the .Meds file extension on all files, immediately shut down your machine and unplug it from the power source so you can stop the ransomware from encrypting at least some of your files.
The most common question we get asked from victims of Ransomware is about what can be done when you have already been infected and the malware has placed its encryption to your photos, videos, documents and other files. Unfortunately, we have to say that your options are limited and none of them guarantee that you will regain the access to your data. Even if you decide to pay the ransom the hackers demand, that still doesn’t mean that you will receive the decryption key and get your files back. The crooks may never send you anything in exchange for you money. Or, if by any chance they do, that key may never work.
So, with this in mind, it’s probably best to try other alternatives, such as the ones described in the removal guide below. Another possibility is to try to recover your files from system backups or personal backup copies from external drives or cloud storages. In the event that none of these suggestions helps, you may also want to check one of the free decryptor tools listed on our website. Before you start any file-recovery attempts, however, it is important to remove .Meds from the system. This is essential if you want to be able to use your machine and we advise you to not waste any time and eliminate the infection at once!
SUMMARY:
| Name | .Meds |
| Type | Ransomware |
| Detection Tool |
.Meds Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Hello,
I’ve been attacked with the ransomware .meds.
I have succeeded in getting back my data on the PC, and removing it.
But my problem is that all files on my external hard disks are Infected, do you have an idea how to release the files that are on the externals ?
Can’t you do it in the same way you have gotten the data on your PC back?
No the PC has a window software that can be restored to previous version.
The external hard disks don’t have that system so we need a Decrypter to release the files.
I have your problem too???
Can you give me the way to back my data as you do?
Please assist me how you’re able to remove the extension virus
Hi. im infected with .meds ransomware. please help me to decrypt my files. all of my personal data encrypted with .meds extension. when decryptor of this ransomware will make?
127.0.0.1 player.kmpmedia.net
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
You aren’t supposed to have all those IPs in your Hosts file, so our advice is to delete them ASAP from the file, and save the changes to it.
This meds file virus has dealt with all my files pls I need an assistance to recover my files back…I will appreciate the person thanks.. 07067756731 is my number