This page aims to help you remove .Meka for free. Our instructions also cover how any .Meka file can be recovered.
The Meka Virus is a harmful PC program with Ransomware characteristics
The Meka Virus is programmed to locate and encrypt important files in the systems of its victims. The encryption used on the files renders them inaccessible and the only way to regain access to them is through obtaining the decryption key.
The Meka virus is a threat specifically created to make you pay for that decryption key. The Meka virus even presents its victims with a detailed set of ransom payment instructions which they are supposed to follow. The ransom instructions are provided within a notepad file that the Ransomware generates once it finishes encrypting the targeted data files. If the transaction isn’t made within a short deadline of 72 hours, the requested sum doubles.
The Meka virus is a Ransomware infection that is able to carry out its encryption activities in full stealth. The Meka virus would normally not get noticed by a conventional antivirus program. The encryption process it uses isn’t harmful to the files, which is partly the reason why many security programs may not flag it as something malicious. This, in turn, allows the Ransomware to “kidnap” all of the important data its victims without getting intercepted in any way.
If you have recently found yourself in a situation where this threat has taken hold of your personal data and is not letting you access it, you need to be well informed regarding the options you have at the moment.
The Meka virus is piece of malware that’s supposed to get you to release the demanded ransom – this is what its creators’ sole goal is. However, the people behind the Meka virus couldn’t care less about what happens after you pay. You may get the private key that will unlock the encrypted data in your computer, but it is just as likely that the hackers choose not to send you anything in exchange for your money. This is why you must never choose to go for the payment option before you have exhausted all other possible alternatives.
This Meka Virus is a particularly harmful computer infection and releasing the files it encrypts can’t be guaranteed. However, there may still be some potential solutions which do not involve a ransom payment, and you can find some of them inside the guide from this page.
.Meka
.Meka is a virus program for PC created with the intention to blackmail the infected users. .Meka will block access to your most valuable files and wait for you to pay a ransom for their release. This virus locks the files through data-encryption.
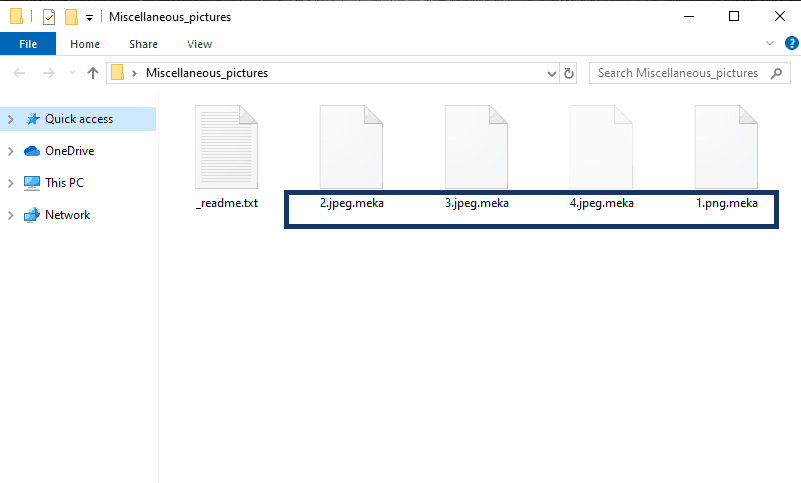
Once the .Meka Virus has infected your computer it will stealthily encrypt your files.
Ransomware is a very dangerous category of computer programs, the purpose of which is to stealthily enter the computers of their potential victims, and lock the screen or the files in the attacked machine. These viruses do that in order to later blackmail their victims – they show a message on the computer screen, and in this message, the victim is notified about the requested ransom payment. If the payment isn’t made, the screen or the files would stay sealed for good.
The .Meka virus
The .Meka virus is a type of money-extortion malware that keeps your files encrypted until you make a ransom payment to the hackers behind it. The .Meka virus makes its ransom demands known via a note it generates on your screen once it locks the files.
The screen-lockers and the encryption-viruses are the two most common forms of Ransomware. The screen-lockers are the ones that are easier to deal with. Getting your computer’s screen blocked by a huge banner that covers everything may sound scary but it is actually not that difficult to deal with the malicious program that’s caused the lockdown on your screen. However, the .Meka virus, the one we will be focusing on in this post, is from the second subcategory of Ransomware – the encryption-viruses (cryptoviruses for short). Those threats are much more advanced than their screen-locking counterparts, and dealing with an infection from such a virus may not always be fully possible. Still, we’ve done our best to share with you helpful information which may allow you to make an informed decision with regard to what to do if the insidious .Meka Ransomware has locked up your data and is currently blackmailing you for a ransom.
The .Meka file
The .Meka file is a file that has been locked by this virus and which cannot be accessed through regular means. Any .Meka file could be opened with the application of the correct decryption key. This key, however, is in the hacker’s hands.
The first reaction of many users who come to face the consequences of such a virus attack is to go directly for the payment of the ransom without even trying to seek potential alternatives. This is not a very wise thing to do for two reasons. The first one is the fact that even if you pay the demanded sum, you may still be left with no way of accessing the files on your computer that the Ransomware has locked-up. In order to render your data inaccessible, Ransomware cryptoviruses use the file-encryption method, and the only surefire way to open an encrypted file is by using the correct decryption key. Of course, the hackers have the said key, and their goal is to make you pay for it. However, it is totally possible that they refuse to sand the key to you even after you complete their demands. Many are the unfortunate users who have wasted their money in vain by sending it to Ransomware blackmailers without receiving a decryption key afterwards.
The second reason why we making an immediate payment as soon as you notice the lockdown on your files is because there may be other ways to restore your data that may allow you to hold on to your money. However, to try those methods, you’d first need to ensure that the malware is no longer present in your system. If you follow the instructions below, or if you use the linked professional removal tool, you should be able to make quick work of .Meka and eliminate it from your system. Afterwards, we advise you to check the recovery suggestions from the second section of our guide. Sadly, they may not be effective in all cases, but it is still important to try them first before you opt for any other course of action.
The Meka Ransomware
Meka Ransomware is a specific form of computer malware specialized in blocking access to its victims’ digital data. The Meka Ransomware virus targets different types of data and encrypts them using a military-grade encryption algorithm which prevents any program from opening the affected files. During the encryption process, the Ransomware generates a private key – this key can be used to unlock the sealed files, but only the hackers who have created the virus have hold of said key.
The Meka Ransomware is a malware program that is designed to extort money from you by offering you this private key in exchange for a ransom. The Meka Ransomware generates a notepad file that contains instructions on how to make the payment and get the key. There’s even a “discount” period of a couple of days during which you only need to pay half of the ransom sum. If the files that this malware has affected are really important to the user, the latter may indeed be willing to issue such a payment if they can afford it. However, we must warn all of our readers that paying the demanded sum may not always end well.
The Meka Ransomware is a threat solely created to get you to pay the ransom – there is little else that the hackers behind it care about. Therefore, it’s possible that the decryption key for the Meka Ransomware encryption never reaches you. The hackers could simply be lying to you about sending you a private key – they may not really intend to do that after you pay them. Another possibility is that you receive a key that isn’t able to unlock your data. In either case, there’s a big chance of wasting your money for absolutely nothing.
The Meka Ransomware is a very advanced form of malware and there’s sadly no surefire method of dealing with the lockdown it places on your files. The Meka Ransomware can be removed but that would still not release the files. And, as we said, even paying the sum requested by the Meka Ransomware may not yield any satisfactory results. That being said, there are still some potential alternatives available out there which can help you ameliorate the consequences of this malware attack and we wish to share some of them with you.
SUMMARY:
| Name | .Meka |
| Type | Ransomware |
| Detection Tool |
.Meka Ransomware Removal Guide
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

I think anyone would refuse “they refuse to sand the key”,
Sanding the key would be super tiring, it is not like sanding the wood.
# localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Those IPs aren’t a problem – they are actually supposed to be in your Hosts file so don’t touch them and simply move on to the next step.