.Merin
.Merin is a ransomware cryptovirus that encrypts digital data to prevent users from accessing it. To regain access, the .Merin victims are asked to pay a ransom for a decryption key that can reverse the applied encryption.
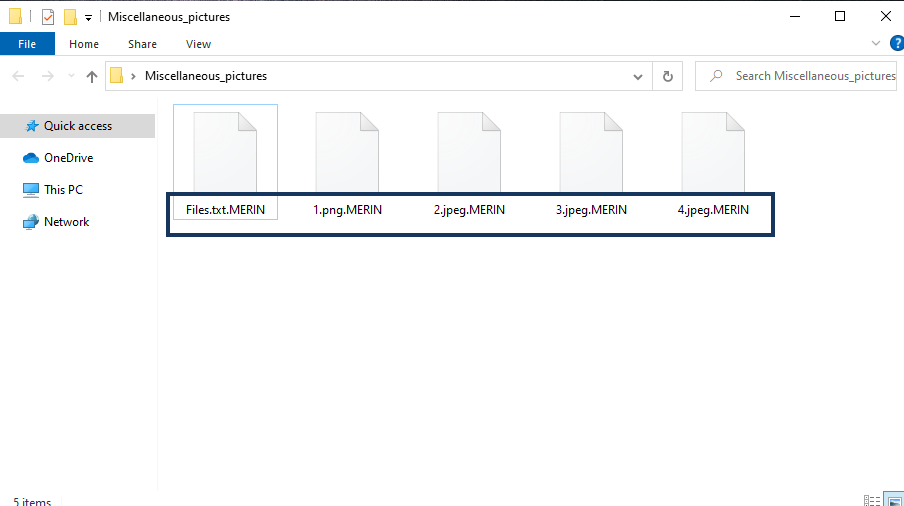
The .MERIN File
The following text aims to educate you about the .Merin Ransomware virus and its features, as well as the methods to safely remove it from your system.
Ransomware can become part of your system secretly the moment you interact with any of its numerous transmitters which could be spam messages, malicious email attachments, fake ads, infected software installers, torrents, and more. Once it has successfully compromised your machine, the malware can scan its hard drives to “decide” which of your files belong to its list of target files for encryption. Usually, these are some of the most commonly used file types such as text documents, video and audio files, images, archives, etc. Then, once all targeted data types have been accounted for, the ransomware will silently run a file-encrypting process and will encode each and every detected file in such a way that the file is rendered inaccessible without a decryption key. Once all of your files are locked, you will receive a frightening alert in the form of an on-screen message or a text file. This message will tell you that to unlock your files and use them again you will have to pay a ransom to the hackers who’ve encrypted your information.
On this page, however, you will find a removal guide designed to help you avoid the ransom payment and remove the .Merin Ransomware from your computer. Sadly, Ransomware is one of the most challenging forms of malware that you can face, so we suggest you carefully read the rest of this article to learn what to do if you’ve got the .Merin Ransomware virus.
The .Merin virus
The .Merin virus is a Ransomware threat that encrypts all types of digital data and requests a ransom payment to decrypt them. Most often, the .Merin virus restricts access to digital documents, archives, databases, images, audio files, video files, and system records.
One of the common ways to get infected with malware of this type is by clicking on the attachments of spam messages. In such instances, if you open an infected email and download its attachment, the virus will contaminate your system. You should keep in mind that practically all downloadable files (images, documents, .exe files) can carry the infection. You may also become contaminated with .Merin by clicking on shady-looking pop-ups on the Internet. Therefore, our advice is to try to avoid them all because, typically, it is rather difficult (if not impossible) to tell the difference between malicious and legitimate ads. What’s more, some of them might even look like system alerts and requests, making it more likely for you to get tricked into clicking on them.
The .Merin file encryption
The .Merin file encryption is a stealthy file-locking process that begins as soon as the Ransomware infects the computer. The .Merin file encryption prevents users from accessing their digital data until they pay a ransom for its decryption.
Many web users ask us about what can be done if a dangerous threat like .Merin compromises the computer. Perhaps the worst news is that whatever you try to do – pay the ransom to the hackers or remove the virus – there is no guarantee that the encrypted files will be restored. If you don’t want to send money to some anonymous hackers, however, we suggest you try to fight the infection with the help of our removal guide. The suggested anti-malware tool on this site may also help you scan your entire computer and get rid of the virus. There is even a section with instructions for data recovery that could potentially help you save some of your files without giving the hackers any of your money.
SUMMARY:
| Name | .Merin Ransomware |
| Type | Ransomware |
| Detection Tool |
.Merin Ransomware Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment