This page aims to help you remove Microsoft Edge Critical Error Red Screen Scam. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Microsoft Edge Critical Error Message
“Microsoft Edge Critical ERROR” is a fraudulent error message that pretends to be from Microsoft to make you think that your computer has been infected by a virus or is damaged. The purpose of the “Microsoft Edge Critical ERROR” message is to try to scare you to call any of the numbers listed and receive further guidance.
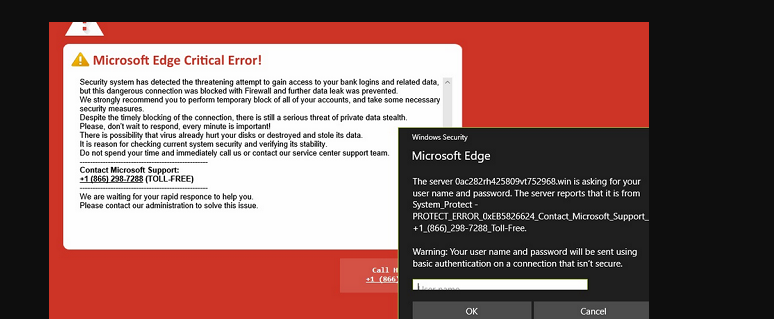
Microsoft Edge Critical ERROR is a false error message displayed by a malicious website
Browser Hijackers are a type of annoying page-redirecting applications that typically work as browser extensions and are promoted as useful tools that would improve the user’s online privacy, surfing experience, browser speed or some other aspect related to their Chrome, IE, Firefox, Opera or any other browser that they might use. However, there’s a reason why such applications are referred to as hijackers and page-redirects. Most such browser extensions can actually be extremely irritating and obstructive as they oftentimes seek to manipulate and modify the user’s browser in a variety of ways. Common examples are when a hijacker tries to open new pages and tabs and redirect the user to unknown sites or when it replaces the default search engine, the new-tab page or the homepage of the browser. In the lines below, you will have the opportunity to learn more about Microsoft Edge Critical Error Red Screen Scam (and whatever you do, please DO not call number 866 393 7989 or 855-247-2962) – one newly reported representative of this class of intrusive software applications. I you have recently gotten Microsoft Edge Critical Error Red Screen Scam installed on your system and made part of your browser, then it is likely that you’d want to have it uninstalled and fully removed from your system which is why we have also prepared a guide that might help you do that manually. Also, on this page we have posted a anti-malware tool which can also help you deal with the hijacker so you can also make use of it in addition to the removal guide for even better results.
Microsoft Edge Critical Error Red Screen
Considering the nature and purpose of page redirects and hijackers like Microsoft Edge Critical Error Red Screen Scam, it should also be fairly obvious that such applications aren’t really created to serve the needs of the end users. If you land a hijacker, it is rather likely that you’d not get anything beneficial out of it.
It should come as no surprise to anyone that page-redirecting and browser-modifying software the likes of Microsoft Edge Critical Error Red Screen Scam typically has one sole purpose, that purpose being to promote different sites, we stores, search engines, software products, online services and others. All in all, most hijackers such as this one are primarily used as advertising tools and through them, their creators are capable of earning quite substantial amounts of income. The way revenue is gained through such hijackers is typically via models known as Pay-Per-Click or Pay-Per-View.
There might be certain hijacker-like browser add-ons which might come with some useful feature that would make their stay on your system worth it despite the annoyance they bring but instances of this are quite rare which is why it’s generally simply better to eliminate any hijacker that makes its way inside your computer system.
One more reason to remove Microsoft Edge Critical Error Red Screen Scam
Apart from the fact that it is annoying, there could be several other possible issues that might come with a hijacker installed on your PC. While this sort of irritating browser extensions aren’t really viruses and do not normally seek to carry out any harmful processes on the PC they’ve been installed on, you should still be cautious around them. The various page you could get redirected to as well as the potential online ads that such browser redirects could trigger might not always be coming from the safest and most reliable of networks. The developers of most hijackers do not really care about the quality and reliability of the advertising materials that their products display. The hijacker is usually only a medium between the end user and the ad creators so even if a certain advert redirects to malicious and illegal sites that distribute viruses like Trojans and Ransomware, the creator of the hijacker wouldn’t really be concerned with that. On the flip side, if you click on a unreliable ad, you risk landing some nasty malware infection – there are all sorts of malicious viruses out there that you might get your system exposed to if you aren’t careful – Trojan Horses, Spyware, Worms, Rootkits, Ransomware, etc.
Fending off hijackers
The good news here is that, as long as you adhere to several simple (yet very important!) online safety rules, you’d be avoid the installation of pretty much any hijacker or other unwanted program that might come your way. First of all, remember to never go to sites that have shady and low reputation or one that are straight up illegal. Also, do not click on those big blinking and shiny banners that you see all the time on certain sites that have more ads than necessary (consider getting an ad-blocker). Also, never open or interact with the contents of e-mails and other web messages that look like spam. Lastly, when installing any new software, make sure to check for optional clauses that offer to install additional applications alongside the main program since in many cases this is how a lot of hijackers get distributed – through file-bundling. If you see such potentially unwanted bundled applications inside the setup menus of a program you are about to install, make sure to uncheck them before you continue.
SUMMARY:
| Name | Microsoft Edge Critical Error Red Screen |
| Type | Browser Hijacker |
| Detection Tool |
Microsoft Edge Critical Error Red Screen Scam Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment