Microsoft.Photos.exe
Microsoft.Photos.exe is a completely legitimate executable file belonging to a Windows application. Recently, however, there have been reports that this .exe has been flagged as a virus by well-known AV vendors.
Malware could disguise as Microsoft.Photos.exe and cause havoc on users’ PCs.
To be infected with a computer virus is an awful experience indeed. Most of the malware infections worldwide are caused by Trojan horses. That’s why we have assembled several articles to discuss various versions of Trojans. In this particular one we will be elaborating on the features and effects of Microsoft.Photos.exe. Hopefully our article and the Removal Guide attached to it will be exactly what you are looking for to successfully fight this unpleasant infection.
What is Microsoft.Photos.exe?
At first, the majority opinion was that this is a false-positive, but there are also reports that some windows apps were exploited through vulnerabilities through trojans. We can not tell you if this is the case, but we will proceed with the idea that you have been breached by a trojan. The correct path the .exe should run from, is C:\Program Files\WindowsApps\(…)\Microsoft.Photos.exe. If it is not running from there, or even if it is, but you have reason to suspect it is a trojan, we advise you to fully complete the guide below, even if just for the sake of safety.
The Microsoft.Photos.exe Virus
As an exemplary Trojan, Microsoft.Photos.exe possesses certain characteristic features common for all the existing versions of this type of malware. Among them are:
- Its ability to self-install on the victim’s PC.
- Its ability to infect all sorts of online content (please, take a look at the potential sources of this virus kind mentioned below).
Possible ways of catching the Microsoft.Photos.exe Virus (or another similar virus)
As the most multifunctional kind of malware, the Trojan group is also characterized by a great number of potential sources. The most likely ways to catch such a threat are listed below.
- Via clicking on a malicious online ad: Not all the pop-ups and banners you come across while surfing the web are safe. Most of them are harmless. Nonetheless, the ones generated by suspicious websites are particularly shady, as they might redirect you to locations contaminated with malware and you may get a virus in the form of a drive-by download.
- Via applying fake updates: You may sometimes see fake update requests displayed on your screen. As soon as you accept to apply them, you can automatically get infected with such a Trojan. The tricky part is that it is extremely difficult to tell the real update notification from the malicious one. That’s why we recommend that you always manually check for updates via the built-in feature of Windows to avoid any suspicious requests.
- Via opening a malicious email (as well as any of its attachments): It is possible to catch Microsoft.Photos.exe by opening an infected email. We suggest that you open only the ones that come from senders you recognize. All others cannot be considered trustworthy. Also, do not forget that Trojans could come with infected images, documents, .exe files. To avoid an infection, you should also avoid all email attachments that you do not expect to receive. What is even more disturbing about that potential source is that the Trojan will most probably come accompanied with another virus, usually Ransomware. You may be aware of the fact that the infections caused by Ransomware are particularly hard to be removed and the files, encrypted by the virus, may be lost forever.
- Via visiting a contagious website like a video or a torrent-distributing one: Any web pages that seem suspicious should be avoided, especially the illegal ones that distribute torrents, movies or software. They are very likely to be infected with malware.
What might result from an infection with the Microsoft.Photos.exe Virus?
There are a great number of possible negative effects such viruses may have on your PC and on you. The most disturbing ones are: stealing important data (such as bank account credentials); keeping track of you as an individual (such viruses might be used for taking control of all components of your system remotely and spying on you via your web camera or microphone); spreading viruses across the web (such malware might be helping a Ransomware version get around easily and sneak into your system); exploiting your PC resources (such malware is fully capable of hacking your PC and turning it into a bot so as to use all the resources it has); committing various crimes on your behalf (via hijacking your identity by using the data you enter on your PC to access accounts). Of course, the awful consequences of any infection caused by a Trojan are not limited to the ones above and there may be many more possibilities.
What to do in case of contamination?
In such a case, carefully read the instructions below and implement them even more cautiously. They are available in the Removal Guide just after the table at the end of this article.
SUMMARY:
Name Microsoft.Photos.exe Type Trojan Detection Tool
Microsoft.Photos.exe Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
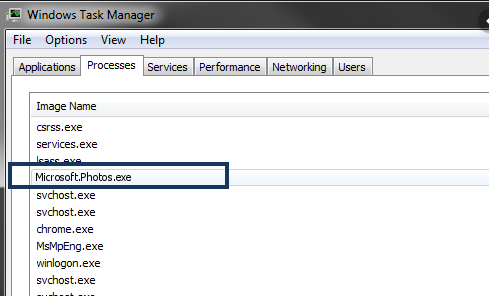
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Hi I am not 100% sure but I think I have been infected with the trojan explained here. My firewall randomly asked if I would “cancel or allow” a connection from Microsoft-Photos.exe to the internet. I’ve never seen this exception asked of me before and so now I am somewhat paranoid about this.
First of all, I am not able to access the folder in which the .exe is located. I can find it by enabling Hidden Files in my view finder but cannot open WindowsApps folder even as an administrator (I am the administrator). Are these telltale signs of an infection my machine? Are there any other surefire ways of identifying this infection? Very behind the scenes, I don’t like this at all…
According to what you’ve told us here, it is highly likely that you have the virus on your PC. It is possible that it stays dormant or doesn’t do anything overly malicious but you must still take precautions. Have a look at our guide and try completing the steps. After you are done, come back here, to the comment section, and told us what happened.
I have:
1. cleaned the registry with CCleaner
2. conducted a malware scan
3. cleaned junk files (temporary files and folders)
4. updated all PC drivers
5. run system file checker (sfc)
6. installed all pending windows updates
Unfortunately I am still unable to access the folder, access is still denied. Is there anything specific you can think of that I should look for in Startup tab and/or Processes tab?
You say “access” the folder, but what about simply deleting it? Or you have tried that already and it still doesn’t work?
How do I block thhis acces?
127.0.0.1 down.baidu2016 .com
127.0.0.1 123.sogou. com
127.0.0.1 http://www.czzsyzgm. com
127.0.0.1 http://www.czzsyzxl. com
127.0.0.1 union.baidu2019 .com
Simply go back to the Hosts file and delete those IPs from it. After that, save the changes to the file.