This page aims to help you identify and remove any Microsoft Scam. Our Microsoft Scam removal instructions work for every version of Windows.
The Microsoft Scam is an umbrella term used to refer to any type of online scam, in which the scammer tries to trick their victim, by making the latter believe that their computer has been infected, and that a Microsoft representative offers them help.
In the lines below, we will go over the most common Microsoft Scam types, and we will tell you how to recognize, and avoid them. In many cases, such scams may be related to Trojan Horses, which may have entered the system. Because of that, the article, you will find a removal guide, which will aid you with the removal of any Trojan that a Microsoft scam may have gotten in your machine.
Microsoft Scam Call
The Microsoft Scam Call is one of the most commonly encountered types of Microsoft-related scams. The gist of the Microsoft Scam Call is that you receive a call from a crook, who tells you he/she is a Microsoft representative.

The Microsoft Scam Call is supposed to make you believe a Microsoft official has contacted you.
The scammers would typically claim that there is some kind of issue with your system, and would offer to help you solve it.
After gaining your trust, the perpetrators may ask for your usernames, passwords, and other similar sensitive details. Also, the people behind this scam may direct you to a legitimate site, from which you are supposed to download a software tool that would allow the “Microsoft representative” to remotely access your computer under the premise that they need to do that in order to fix the purported system problem.
If you submit to any of the scammer’s demands, you’d be putting your system, and virtual privacy in serious jeopardy.
Microsoft Phone Scam
The Microsoft Phone scam is fortunately easy to figure out – Microsoft officials would never directly contact you via a phone call. So, a Microsoft Phone scam is any unexpected call from a person presenting themselves as a Microsoft official, and warning you about issues in your system.

The Microsoft Phone Scam is easy to avoid if you are careful.
If you are wondering how they got your number, the scammers usually use publicly available phone databases, which is why they may also know your name, location, and other personal details.
Microsoft Support Scam
The Microsoft Support Scam is another flavor of the Microsoft scams, which could be quite convincing to the less experienced users. Here is how the Microsoft support scam functions: some unsafe and misleading malvertising ad lands the user on a phishing page that looks exactly like Microsoft’s support site.

The Microsoft Support Scam uses shock and intimidation to trick the users.
As soon as the page opens, two pop-ups appear on the screen. One of them is designed as a warning, telling the user there’s a malware in their computer, and giving them a fake Microsoft support team number. The other pop-up is designed as a sign-in form, and the user is asked to provide their username and password.
The reason this scam works is because the two pop-ups basically block the browser. If you get on such a Microsoft Support scam-page, you won’t be able to close the pop-ups, the current tab, or the browser itself, by clicking on the X buttons. You will also not be able to switch to another tab or window. This may instill panic in the less experienced users, and intimidate them enough for them to call the fake support number, and provide their login details. There, however, is an easy way to unblock the browser – use the Ctrl + Shift + Esc key combo to open the Task Manager, go to the Processes tab, find the browser processes, right-click on the one corresponding to the tab of the phishing page, and select End Process. If the Task Manager has also been blocked, you can always simply shut-down your machine through its power button, and then turn it back on.
Microsoft Scam Email
The Microsoft Scam Email is another scam scheme similar to the ones we’ve already mentioned above. In the case of the Microsoft Scam Email scheme, the user is contacted via an e-mail letter, and is told that their Microsoft account would be deactivated unless the instructions from the message are followed.

To avoid the Microsoft Scam Email, never trust random questionable emails.
The user may be required to provide a username and a password, to call a fake support number, or to pay a fee. In any case, make sure to never respond to such emails – Microsoft would never contact you in this way, asking you to do any of those things.
Microsoft Account Scam
The Microsoft Account Scam is any type of a scam related to Microsoft, in which the user is threatened that they may lose access to their account unless they complete the demands of the scammer (who is impersonating a Microsoft official). A Microsoft Account Scam, for example, is the email scam we told you about in the previous paragraph.
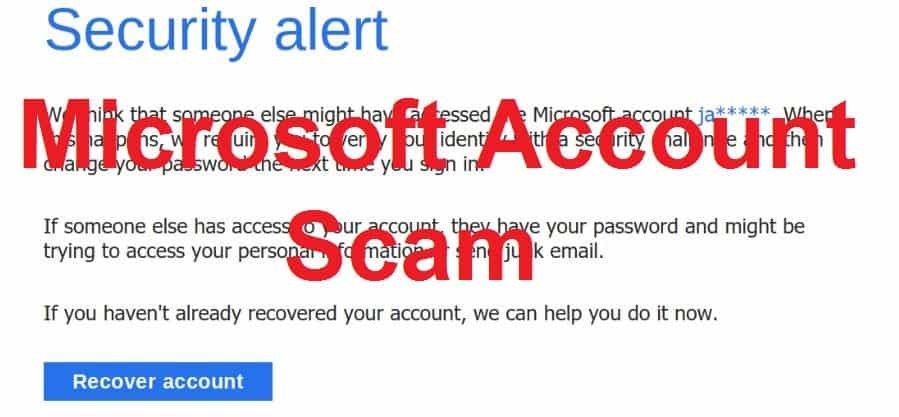
The Microsoft Account Scam tries to make you believe your account will be deactivated.
Microsoft Account scams could also be conducted not only through e-mail, but also via phone, phishing pages, and even through fake optimization software.
What gives this type of scam away is the warning that you’d lose access to your account if you don’t do as you are told – Microsoft wouldn’t ever contact you under such a premise.
Microsoft Virus Scam
The Microsoft Virus Scam is the kind of scam that uses a scareware program, which is presented to the user as a seemingly legitimate security tool. In reality, the Microsoft Virus Scam program is actually closer to a malware. It displays a fake warning message on the screen, telling the user their machine has been infected.

Fake security software is usually used in Microsoft Virus Scam schemes.
This scam is similar to the Microsoft support scam, but the difference is that the fake warning comes from a program in your computer, and not from a website. The text in the warning may tell you to contact a certain number, or provide some personal details like usernames and passwords in order to receive help with the removal of a non-existent virus.
This scam is potentially one of the most problematic ones as it may be difficult to recognize. The best precaution against it is to never install unverified software in your computer, and to only use trusted and popular security tools. If somehow, some purported security tool has gotten in your computer without you having deliberately installed it, it’s better to remove it from your computer, and not trust any warnings it may show you.
Securing your computer
It is highly likely that a Trojan Horse virus may have entered your computer if you have followed any of the scammers’ instructions. In some cases, the scam itself is made possible by the presence of a malware program in your computer (see the Microsoft Virus Scam). This is why we urge you to visit the removal guide you will see below, and follow its steps in case you have become the target of any type of a scam, similar to the ones explored in this article.
SUMMARY:
| Name | Microsoft Scam |
| Type | Trojan |
| Detection Tool |
How to Remove a Microsoft Scam
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment