Mool
Mool is a ransomware variant that encrypts the files on its victims’ computers. As a result, Mool makes those files completely inaccessible and then demands a ransom payment for the files to be unlocked. In this article, we will explain how Mool operates and we will also show you how to remove this virus from your computer manually.
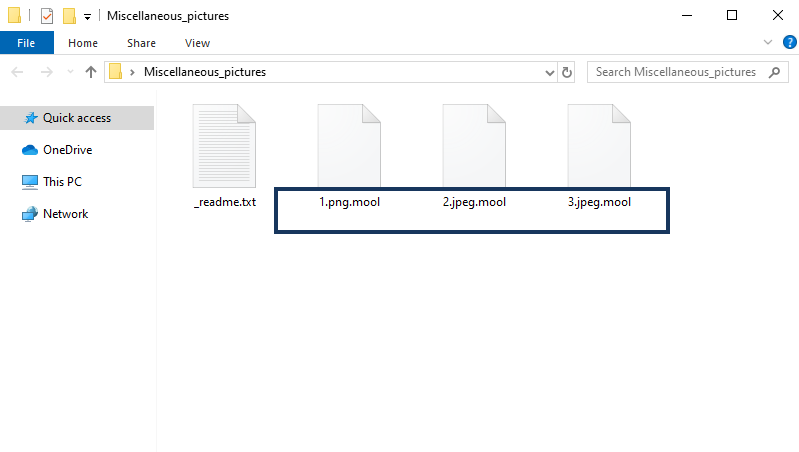
The Mool Virus will encrypt your files and leave a _readme.txt file behind
If you have been attacked by this particular ransomware representative, then you were most likely informed about it via the ransom notification that was placed on your screen. It most probably contained some information regarding the fact that you won’t be able to open your files anymore. But its main focus would have most probably been on the ransom payment that the hackers demand in exchange for a special decryption key. Usually they also resort to various scare tactics, such as threatening to delete the key after a certain time unless the payment is made, or even deleting the encrypted data.
Don’t give into these threats. While they may or may not necessarily be true, their main goal is to throw you off balance and prevent you from thinking clearly about the whole situation. Truthfully, you do have other options available to you. There are alternative ways that you can try to restore your files that won’t cost you anything. And if those fail and if you so choose, you can always resort to making the ransom payment. But before you do so, know that either way you may be facing the permanent loss of your data. We cannot guarantee that the restoration methods we offer here will work in each and every individual case. But neither can the hackers promise that they will in fact send you a key, or that it will even work.
Be that as it may, however, your first step should be to remove Mool from your PC as soon as possible. If you don’t and you attempt to recover your files using whatever means you decide to, those files may end up getting encrypted immediately after, leaving you back at square one. We have included a detailed removal guide just below this article in step-by-step form, which you can follow in order to get rid of this virus.
The Mool virus
The Mool virus uses encryption as its main weapon, which allows it to go unnoticed. The Mool virus will typically not trigger most types of security software while it is encrypting the files on your machine.
This is a very curious (in a rather morbid way) phenomenon and it is owed to the encryption process itself. Encryption is in itself not a malicious thing, and realistically, it doesn’t harm your data. Encryption exists as a way to protect data, and it’s something so widespread that we rely on it every day to complete basic tasks. Every payment you make online, every purchase, every entry of personal or otherwise sensitive information is protected by means of encryption.
Alas, cybercriminals have come up with a way to make this among the most lucrative extortion schemes on the internet, generating billions of dollars in profit through blackmail. And since it has emerged in the early 90s, ransomware has gained incredible momentum. In fact, millions of new ransomware variants surface each year, and their numbers increase exponentially. This goes to show how awfully difficult it is for victims to deal with these types of viruses. A piece of malware like Mool could very well be the end of your files as you know them. There’s simply no telling whether the decryption key that you pay for (if you choose to go down that road) will actually work as it should and will decode your data. And sometimes it may not be possible to extract copies from system backups, which is something we will show you how to try later on in the removal guide.
Furthermore, the fact that the hackers behind ransomware like Mool ask to be paid in bitcoins or other types of cryptocurrencies has also played a huge role in the increase in popularity of this particular criminal scheme. Cryptocurrencies ensure that the wallet that you send your money to cannot be traced to a person or location. And this makes it incredibly difficult for the relevant authorities to counteract such viruses.
The Mool file distribution
The Mool file may have landed in your system via several very common malware distribution channels. But the most likely way you could have gotten the Mool file is through an infected message of some sort.
For example, it’s typical for hackers to send various phishing emails that are disguised as legitimate organizations or companies that you may or may not have dealings with. And the body of the email may be trying to get you to click on an included link or enclosed attachment. That is where the malware is embedded, and if it is not the ransomware directly, then it’s probably a Trojan horse that is set to download the ransomware. This is what’s known as a backdoor virus.
Other common methods of distribution for malicious software of this type include the so-called malvertisements. These are online ads that hackers have embedded with viruses, and once you click on a fake ad like this you automatically land the infection. Ransomware like Mool can also have gotten into your system if you downloaded some pirated content, for example. Cracked software or illegally distributed movies and music that are available for download on torrent sites and other such platforms can potentially be laced with all sorts of security threats.
This is why one of our main tips on preventing future attacks of this kind is to stay away from these potential ransomware sources. Try to critically assess any incoming messages and determine whether they are indeed safe to interact with. And do your best to avoid visiting sketchy or suspicious web locations, as well. Last but not least, in case Mool really did enter your system through a backdoor helper, after you have removed it, be sure to scan your system for the presence of Trojans and remove those if necessary, as well.
SUMMARY:
| Name | Mool |
| Type | Ransomware |
| Detection Tool |
Remove Mool Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Hi. My pc was attacked with .mool virus. I am unable to find decrypter for it can any one help me in finding solution.
Hello Suhas, if you cannot find a decryptor in our page I’m sorry but your files cannot be recovered yet.
my file also was attacked by .mool virus. What should i do for Decrypter my files . is there any solution for It ?
Hi Janesh
did you follow the guide in this article ?