Mpaj
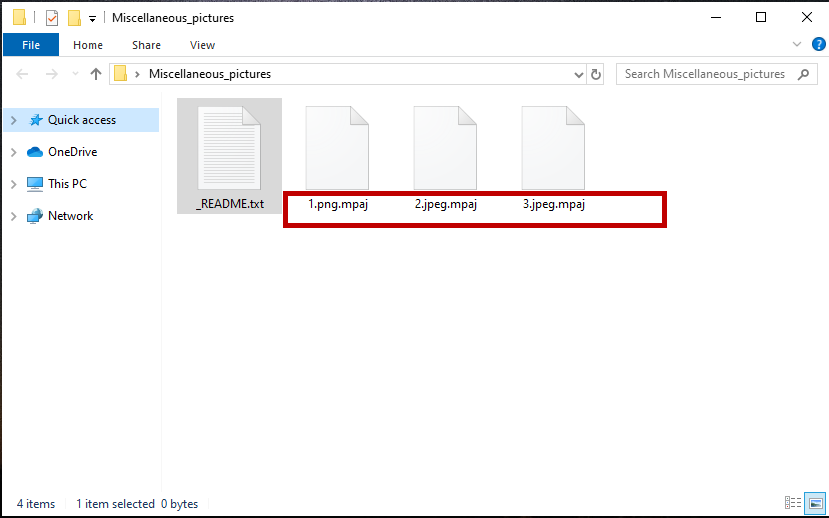
Mpaj is a malware program that attacks Windows computers with the goal of denying its victims access to their own data files. Mpaj belongs to the file-encrypting Ransomware category as it uses data encryption to lock the files of the attacked users.
The Mpaj Virus Ransomware file encryption
This malware type is very common and it is also highly effective in staying unnoticed while secretly applying encryption to the users’ files. The goal of this virus is to force its victims to pay money in order to restore access to the encrypted data. Only then would the hackers behind the Ransomware (supposedly) allow their victims to recover the locked files. However, it is unwise to trust any promises made by the same people who are responsible for your inability to open and use your own personal data. After all, the hackers behind Mpaj are after your money and they couldn’t care less if you actually get to restore your files or not. This means that it is definitely within the realm of possibility that they may refuse to provide you with the means to release your data even after you’ve followed their instructions and paid the demanded ransom sum.
The Mpaj virus
The Mpaj virus is data-targeting malware that seeks to prevent its victims from accessing the files stored on the attacked computers. The Mpaj virus then displays a ransom note that informs the victim they must pay a ransom to restore their data.
For users who don’t have any too important files on their computers’ hard drives, such a malware attack wouldn’t be all that devastating since Ransomware viruses cannot cause any other issues. Viruses like Mpaj typically cannot corrupt the system, steal sensitive data from the computer, or spy on their victims. Instead, they simply encrypt the files of the user, making them unavailable.
Another scenario in which the effects of a Ransomware attack would be all but nullified is when the victim has backups of their important data. In such a case, even if the original files on the computer are locked, the user would still have accessible copies of those files on their backup location. Of course, in either of those cases, the virus would still need to be removed in order to prevent future encryption of new files or the encryption of the files located on the backup when it is connected to the computer.
The Mpaj file decryption
The Mpaj file decryption is the recovery process the completion of which would make the encrypted files free again. The Mpaj file decryption requires the application of a special key that is unique for each PC that the Ransomware virus has infected.
Of course, this key is what you are supposed to receive from the hackers after you pay the ransom. However, as we said, trusting the promises of those cybercriminals is inadvisable. Instead, our advice for you is to remove the virus using the instructions you’ll find down below. Then, after the Ransomware is no longer on your computer, you can move on to the recovery section of the guide, where you will find some free alternative file restoration methods that may help some of you bring your data back.
SUMMARY:
| Name | Mpaj |
| Type | Ransomware |
| Detection Tool |
Remove Mpaj Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

my computer is attack by .mpaj ransomware. please help me how to remove and recover my files.
Heelo Eugene, you can remove the virus from your computer by following our guide, but this is one of the newest ransomware variants and file decryption is not possible yet.
hi, my all videos my images files have been damaged corrupted ,its shows same extension mpaj ive tried alot of things but none are useful to decrpyt my data any ideas hwo can i recover them,,?
Hello karan, your PC seems to have been infected with one of the newest ransomware virus variants and at this point file recovery is not yet possible.
help me please.. is online id have a hope to be recoverd?
Hi marwa, unfortunately at this point file recovery from this particular ransomware virus is not possible.