Mpal
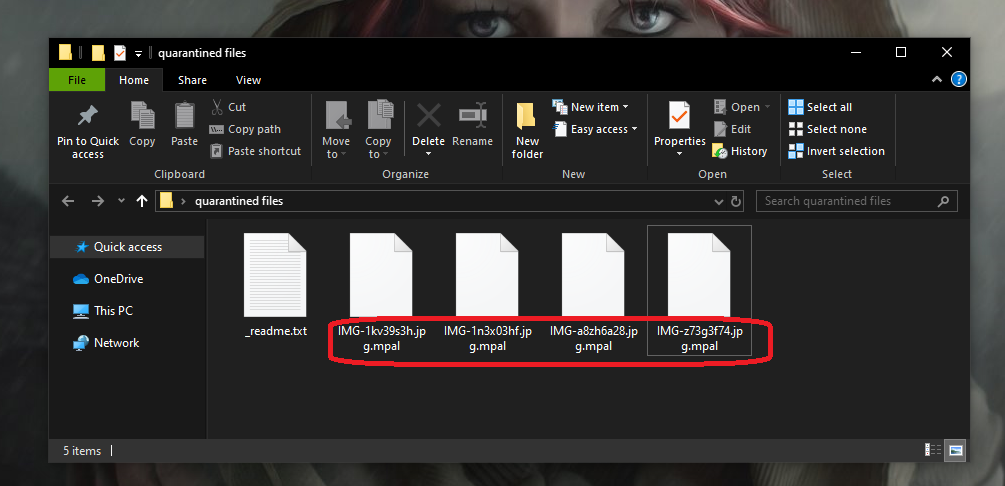
Mpal is a new virus threat that infects Windows computers and locks important files stored on them. Mpal can be described as a file-encrypting Ransomware virus due to the fact that it uses encryption to lock the victims’ files and then demands a ransom payment.
If the requested ransom isn’t paid in time by strictly following the payment instructions provided by the hackers, the user would never be given the chance to reopen their encrypted files. The encryption code applied to the targeted data is virtually unbreakable and the chances of recovering any data without receiving a special decryption key from the hackers are rather low. Still, this doesn’t mean you should pay the ransom right away after you realize your files have been locked and a ransom-demanding banner is displayed on your screen. When Ransomware like Mpal attacks you, the first important thing to remember is to try to retain your calm and rationally assess the situation. Maybe the files that were locked aren’t that important to you and aren’t worth your money. Or, maybe, you have previously set up backups of your most precious files that you’ve forgotten about. Also, it is possible that there are accidental backups of some of the files saved on other devices, on cloud storage, in your email, and so on.
The Mpal virus
The Mpal virus is a software threat of the widespread Ransomware category that blocks user data and then demands a ransom. The Mpal virus uses advanced encryption to achieve that so even if you manage to remove the malware, the files would still remain locked.
If you have already checked everywhere for potential backups of your data and have not found anything and if the virus has indeed managed to encrypt some files that are really important to you, then you must decide whether or not to pay the ransom. If you have the needed sum and can afford to spend it this way, paying may indeed be a possible way out of this. The problem is that, in a lot of cases, the criminals behind such viruses refuse to cooperate after the payment is made and simply vanish without providing their victims with a way to restore their files. This is why it is generally not advisable to make the money transfer, at least not before you’ve tried some other options.
The Mpal file decryption
The Mpal file decryption is the main data-recovery method that could allow users to regain access to their locked files. The Mpal file decryption is usually only possible if the user has the matching decryption key that the virus has specifically generated for their computer.
The problem is that you may never get hold of this key even if you send the hackers the demanded ransom sum. However, if you are interested, we can show you some alternative methods that you can try out in an attempt to recover some of the encrypted data. We can’t promise that those methods would get the job done but, in some cases, they might. Besides, they are free and won’t require you to contact the hackers, so there’s really nothing to lose if you give them a try.
SUMMARY:
Remove Mpal Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Reply