My4gdatavr.xyz
My4gdatavr.xyz is an application that can flood you with advertisements, reroute you to unknown sites, substitute the search engine and/or the address of the browser’s homepage and trigger several other types of web browsing disruptions. Normally, My4gdatavr.xyz may attach to popular browsers like Chrome, Firefox and Edge as a browser extension.

Apps such as My4gdatavr.xyz, Agafurretor and iStart Search Bar are generally known as browser hijackers. They typically display annoying advertisements that would certainly frustrate anyone who encounters them in their browsers. Sadly, the browser hijackers are quite common pieces of software and a popular source of web browsing nuisance that many web users do not even know how to cope with. Nearly everyone who encounters such an app, however, is seeking to remove it and uninstall all its components and browser changes, since it is typically very difficult to browse the internet in peace when a browser hijacker operates in their browser.
Applications like My4gdatavr.xyz are really difficult to remove correctly from a device. Normally, the first thing that may come to your mind when you want to get rid of My4gdatavr.xyz from your computer is to access the Control Panel and try to uninstall it from there.
When it comes to dealing with browser hijackers, however, your attempts to uninstall the software from your computer’s Control Panel or from the application extensions tab may not always be enough to completely eliminate the unwanted app. You most definitely will have the nagging software back to annoy you the very next moment you open your browser even if you have just seemingly removed it. That’s why you definitely may need some support to uninstall My4gdatavr.xyz the right way.
Fortunately, you are on the right place because our “How to remove” team has prepared a step-by-step removal guide with detailed guidelines no how to detect and deal with the browser hijacker quickly and effectively. If you are not excited about the idea of tinkering with your computer’s settings, however, don’t close the page. Down below there is also a professional automatic removal tool for self-help that can do the job for you in just a few clicks. Just check out the removal guide section where you will find all the details and directions you will need.
Do not postpone the removal of My4gdatavr.xyz
The main reason we usually advise our readers to get rid of browser hijacker applications like My4gdatavr.xyz is that they may sometimes be unreliable. While such apps definitely are not so dangerous as viruses and malware programs like ransomware, or Trojans, they should be taken with a grand of salt, particularly because of the random advertisements they tend to show on your monitor.
It’s a well-known fact that the online advertisements can be unsafe if their origin is some low-quality or sketchy website. The security risk is even greater when apps like My4gdatavr.xyz keep spamming you with click prompts and auto-redirects to different web locations. Thus, even though the browser hijackers don’t intentionally expose you to risky commercial material, this doesn’t change the fact that you may accidentally click on some sketchy internet pages that get promoted on your screen. And, you surely don’t want to get infected with a nasty Trojan or a ransomware virus if you do that. And that is why it might be a better option to simply uninstall the ad-generating app beforehand.
SUMMARY:
| Name | My4gdatavr.xyz |
| Type | Browser Hijacker |
| Detection Tool |
Remove My4gdatavr.xyz Virus
To try and remove My4gdatavr.xyz quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the My4gdatavr.xyz extension (as well as any other unfamiliar ones).
- Remove My4gdatavr.xyz by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of My4gdatavr.xyz and any other suspicious items.
If this does not work as described please follow our more detailed My4gdatavr.xyz removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove My4gdatavr.xyz from Internet Explorer:
Remove My4gdatavr.xyz from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
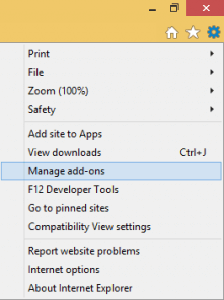
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
![]() Remove My4gdatavr.xyz from Firefox:
Remove My4gdatavr.xyz from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

![]() Remove My4gdatavr.xyz from Chrome:
Remove My4gdatavr.xyz from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
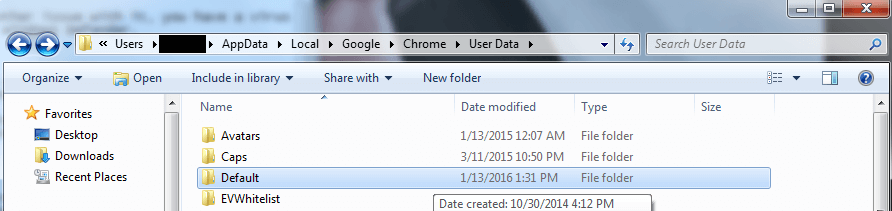
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment