Ncov
Ncov is among the latest additions the category of malicious code known as ransomware. And more specifically, Ncov falls into the most dangerous subtype of file-encrypting ransomware.
This means that viruses of this type encode the files on their victims’ computers using a strong encryption algorithm. And as a result, these files becomes inaccessible to anyone, as no software or program can read or recognize them. Then, after all is said and done, the virus will usually reveal itself using a ransom note that is placed quite obtrusively either on the desktop of the computer and/or in the folders containing encrypted data. And the text in it will normally inform the victims of what has come to take place and how they will no longer have access to their own personal files. And if they are to ever regain access to said files, the victims are asked to pay a certain amount as ransom in exchange for which they are to receive a decryption key, which will undo the encryption. Hence, where the name ransomware comes from.
This is an all-too-common blackmail tactic that’s been used for over three decades now. But it wasn’t until the last decade that ransomware like Ncov really came to explode and become the type of massive threat that it is today.
With all that being said, however, you’re probably way more eager to know what you can do to solve this predicament, preferably without spending heaps of money. And there are actually potential solutions that don’t involve negotiations or dealings with cybercriminals. In fact, we strongly encourage users to explore alternative means of file recovery, and we have listed several such options in the second part of the removal guide below. Just be sure to complete the steps in the first part of the guide, as the removal of Ncov is essential to the safety of any files you manage to restore or any new such ones that you create later on.
The Ncov Virus
The Ncov virus is a sophisticated piece of malicious code that denies you access to the data stored on your computer. The file formats targeted by the Ncov virus are pretty much all the most popular and commonly found ones.
Hence, as a result of such attacks, users typically lose music, videos, pictures, all forms of text files, etc. And in some cases some may be able to cut their losses and just deal with the removal of the virus itself. But very often the loss of such data can result in quite substantial financial losses as well, especially when companies and organizations are targeted. Even so, recovering your files using alternative methods is still the advisable course of action, as it is the only way to discourage hackers from continuing with their criminal scheme.
The .Ncov Decryption
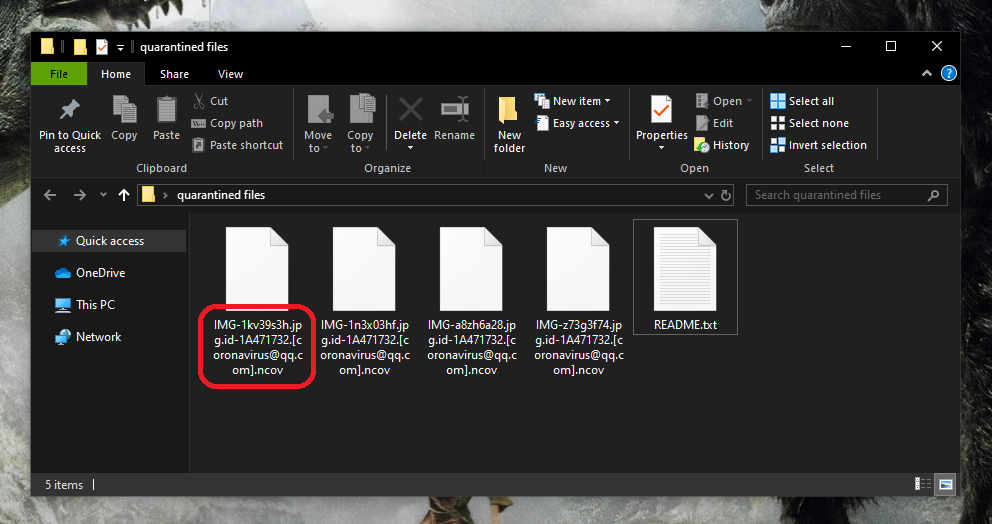
The Ncov file extension is the suffix added to the end of each file name of the data that’s been encrypted by this ransomware. The Ncov file extension pretty much blocks other software from being able to recognize the file format and would require a special decryption tool to return the files to their original state.
SUMMARY:
Ncov Ransomware Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply