Nefilim
If your computer has been infected by Nefilim, you may lose access to a large portion of your files. Nefilim is one of the latest ransomware cryptoviruses to be released on the public. And the effects of variants like Nefilim are considered to be among the most devastating of all types of malware.
The NEFILIM virus will encrypt your files and leave a message in a .txt file.
Nefilim is called a cryptovirus because of the way it operates. Namely, malicious programs of this kind are designed to apply complex encryption algorithms to specific files types that they locate on their victims’ computers. For instance, this may be pictures, audio and video media, executables, text documents, and on occasion even system files can be targeted by ransomware.
The objective of this encryption process is to make the files in question inaccessible, so that the victim users are forced to pay ransom to the hackers behind the infection. The ransom, in turn, is for a decryption key which the hackers promise to send upon receiving your payment. And, in theory, once you receive the decryption key and apply it to your locked data, you should be able to regain access to it once again.
But that’s just theory. In practice things are not at all guaranteed to go as smoothly and there’s a fat chance of you wasting a large amount of money on a solution that won’t work. Therefore, when dealing with infections of this type, it’s advisable to seek alternative options and explore those before resorting to the ransom payment.
The Nefilim virus
The Nefilim virus is highly dangerous and must be removed from your computer as soon as possible. It may happen that the Nefilim virus will encrypt whatever files you manage to salvage all over again, and you will have exhausted your restoration opportunities.
This is why we have designed a special removal guide that you can use free of charge right on this very page. It contains instruction that you must follow very thoroughly in order to have this ransomware completely eliminated from your PC. And it’s also important that you do this before you attempt to recover your encrypted data in any way – even if it’s by means of paying the requested ransom.
Speaking of file restoration, in the same guide below you will reach a second part that is devoted to this subject. We have included a number of suggestions that may prove helpful in recovering the data that’s been locked by Nefilim. However, bear in mind that due to the nature of this process and the malware in question, not all of these suggestions may work in each individual case. But we do, nevertheless, encourage you to try and see what might be successful for you. Of course, if you have copies of your files stored on a separate drive or device, then you’re all set and all you have to worry about is the removal of the virus itself.
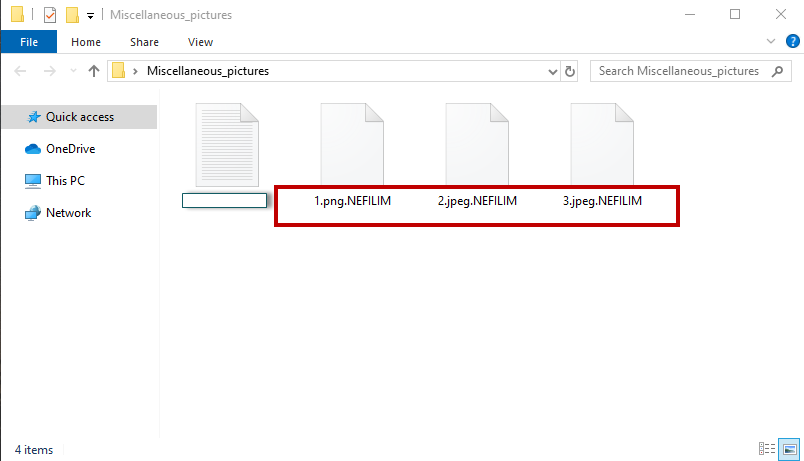
The Nefilim file extension
The Nefilim file extension represents the suffix that you see right at the end of the names of the encrypted files. Basically, it is because of the Nefilim file extension that no program will be able to identify the file format and read it.
SUMMARY:
| Name | Nefilim |
| Type | Ransomware |
| Detection Tool |
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment