Nerbian RAT
Nerbian RAT belongs to the notorious class of malicious code known as Trojan horse viruses. Therefore, it is highly important that Nerbian RAT is removed from the infected system as soon as possible.
Nerbian RAT is one of the latest releases of this malware category, but this is the most numerous category of them all. And millions of new variants are developed and released every year. That goes to show two things. One is how useful and dangerous these viruses are, which is what makes them the weapon of choice for so many hackers and cybercriminals. And another is how vital it is that users invest inadequate protection measures against such threats.
Below we will cover exactly what kind of damage you can expect to face when dealing with viruses like Nerbian RAT. But for the moment let’s focus on one of this type of malware’s main features that has largely made it so popular. Namely, its stealth. Trojan horse viruses are infamous for their ability to avoid detection and they have mastered many a technique in order to ensure this. For instance, some variants are quite capable of switching off your antivirus system once they’ve entered the system and have obtained admin rights.
And very commonly Trojans like Nerbian RAT, Bloom.exe, Energy.exe will masquerade as system files or system processes in order to fool you into thinking they are legitimate system components. This is where we should point out that Nerbian RAT may very well be doing the same, and it has likely burrowed deep in your OS. And therefore, it’s important that when undertaking the necessary steps to remove this threat, you follow them exactly as described in the removal guide below. Accidentally deleting a genuine system file could potentially lead to irreversible system damage, and you don’t want that. But if you would rather trust a professional software application to handle this job instead, then we have one of those available for you on this page as well.
What Nerbian RAT is capable of doing
There are very many different things that software of this type can accomplish on your computer. And that is also why hackers and cybercriminals tend to favor Trojans over other types of malware – because they are simply so much more versatile.
We can give you several examples of the types of things a variant such as Nerbian RAT may be programmed to do on an infected machine, but keep in mind that this list is by no means exhaustive.
For instance, Trojans are very commonly used as backdoor malware to allow other malicious code into the infected system (e.g. ransomware). Trojans can also be set to exploit your system’s resources for cryptocurrency mining, spam distribution and involving other computers in botnets. But perhaps one of the most popular usages is theft. Trojan horse viruses can track you in every way possible to obtain information about your social media profiles, your financial credentials, various forms of correspondence, personal information, etc. And that illegally obtained information can, in turn, be used for all sorts of other wrongdoings.
SUMMARY:
| Name | Nerbian RAT |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
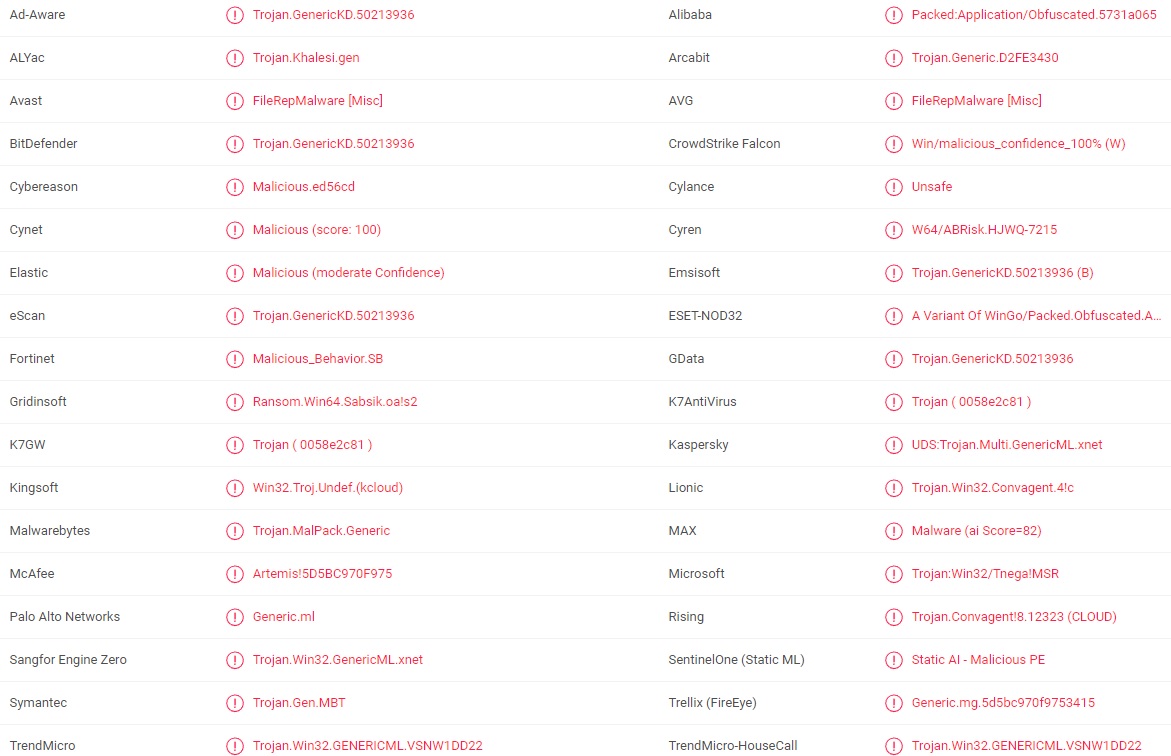
| Detection Tool |
Remove Nerbian RAT Malware
If you are looking for a way to remove Nerbian RAT you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for Nerbian RAT and any other unfamiliar programs.
- Uninstall Nerbian RAT as well as other suspicious programs.
Note that this might not get rid of Nerbian RAT completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment