Netwalker
Netwalker is a malicious computer program that has been designed to prevent you from accessing your files and ask you to pay a ransom for them. Netwalker has features of a Ransomware cryptovirus and uses a data encryption algorithm to restrict your access to a variety of user files.
The Ransomware category of malicious software has undergone a huge boom in both the number of viruses that are created and in terms of how advanced these viruses are. Netwalker, for instance, is an infection that can sneak in the system without the users’ knowledge and encrypt their files in no time. Next, the malware will leave a message in a text file and will ask the victims to transfer a certain amount of money for a decryption key.
In general, the concept of all Ransomware threats follows the same principle – the infection enters the system of an individual silently (usually this can happen with the help of a Trojan horse backdoor, a malicious file or a cracked software installer) and without visible symptoms restricts access to something in order to demand a ransom.
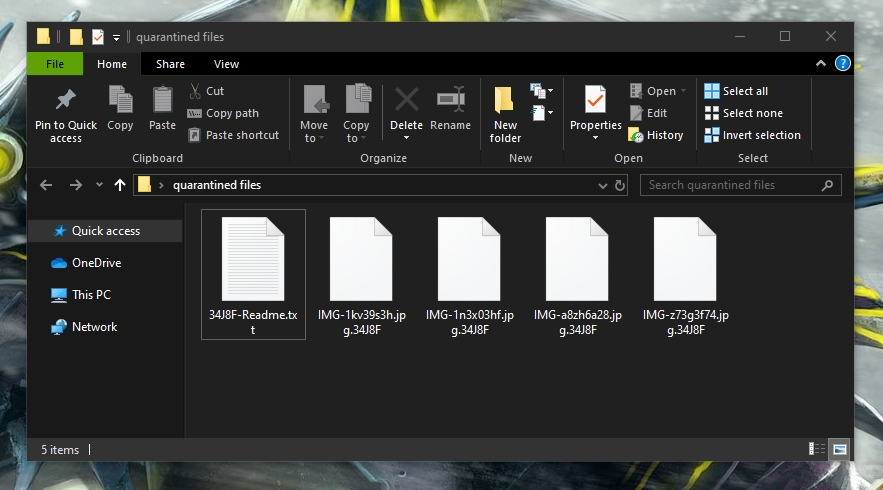
In case that your digital information is the target of the infection, none of your files will be accessible and their file extension may be changed to a different one that no program can recognize and read. This is enough for the hackers behind the virus to place their threatening message and ransom demands. The victim is typically immediately requested to pay a fixed amount of money in order to receive from the crooks a secret decryption key that can unlock the restricted files. Obviously, not everyone would be prepared to pay the ransom – some victims may see this as the only solution while others seek alternative solutions and professional help to remove the ransomware and recover their files.
The Netwalker Ransomware
The Netwalker ransomware is a malware component used to hack Windows computers and then lock the files on their hard drives. The way the Netwalker ransomware operates is very stealthy as the malware does not show any red flags that can give it away before it has been completed.
Many people come to realize that they have been infected only after the ransomware has encrypted their files and has placed the ransom message on their screen. Transferring the required money, however, should not be your initial action even if you value the files that the Netwalker virus has encrypted. The reason is, you may never save your files from the encryption even if you fulfill all the hackers’ demands. In many cases, the cyber criminals behind the ransomware don’t keep their promises and get the money without giving the users a working file decryption key.
The Netwalker file decryption
The Netwalker file decryption is a process that enables victims of the virus to liberate their files from the applied encryption. The Netwalker file decryption normally needs a special key to complete successfully, but you can always try some other options.
In the second part of this article, there is a free removal guide that you can use for an alternative recovery of your computer and your files. We strongly advise you to remove Netwalker with the help of its instructions and try the file-restoration suggestions in the data-recovery section.
SUMMARY:
Netwalker Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Reply