New.lightfoot.top
New.lightfoot.top is a piece of software that, similarly to most other browser hijackers, can be added to your browser in order to tinker with its settings and display nagging ads on your screen while the browser is being used. For this reason, New.lightfoot.top is categorized as a browser hijacker.

The majority of browser extensions and add-ons out there are helpful software tools that are supposed to improve your overall experience while surfing the Internet by offering you some useful function or making your browser safer and better optimized for your specific needs. However, there are also those extension-like apps that would actually worsen the way your browser functions by filling its tabs with nagging ads and page-redirects and/or by making unwanted alterations to the search engine tool of the browser, to its starting page or to the toolbar. Pretty much every browser can be affected in such a way so it doesn’t matter what your default browsing program is – Chrome, IE, Firefox, Edge as well as most other browsers out there are all susceptible to this kind of unpleasant effects caused by a specific type of software components that are usually referred to as browser hijackers.
As the name suggests, an app of this kind is capable of hijacking your browser without your permission. But what does “hijacking” mean? Is it similar to a malware infection with a cyber threat such as a Trojan horse or maybe a ransomware virus? Fortunately, this isn’t what we are talking about here. For all intents and purposes, browser hijacker apps are not in the same category of software as actual malware viruses such as the ones we mentioned above. Of course, this certainly doesn’t meant that hijackers are not unwanted. Quite the contrary – pretty much every user who comes to face the effects of a browser hijacker on their main browser, quickly realizes that the best thing they could do in such a case is to remove the pesky app and, in that way, bring the browser back to its regular state.
This brings use to the main topic of this article – the removal of New.lightfoot.top. Understandably, if you currently have New.lightfoot.top component inside your PC, you’d most likely want to have it uninstalled at once. If that’s indeed the case with you, we advise you to have a look at our removal guide.
If you think that you might not be able to manually deal with the steps in the guide, remember that you can always ask for our assistance through the comment section on this page. Also, you might have noticed that there’s a removal program added to the guide – this is a professional removal tool that can take care of New.lightfoot.top for you so you could also use that as means of eliminating the intrusive piece of software that you are currently struggling with. The important thing is to make sure that New.lightfoot.top or Fast Captcha are removed from your machine because hijackers, though not rel viruses, could actually sometimes make your machine less secure.
Dangers of browser hijackers
New.lightfoot.top is likely not going to try to steal or encrypt your data, corrupt your OS, block your antivirus program or spy on you – those are criminal activities normally carried out by malicious malware threats like Trojans, ransomware, spyware and rootkits. In comparison, hijackers are mainly utilized within the online marketing industry as means of allowing for greater exposure of certain products, sites, online stores and web services through the intrusive and oftentimes aggressive advertising campaigns that such apps tend to conduct. However, your PC is likely to stay unharmed. The problem here is that the different ads you might come across on your screen while New.lightfoot.top is active inside your PC might be unsafe or at least might link you to some sketchy sites or display to you misleading web offers and download requests. With that in mind, it should be pretty obvious why you ought to get rid of New.lightfoot.top at once instead of allowing you to operate from within your system.
The key to keeping your machine clean in the future
Of course, it’s always better to prevent the installation of hijackers in the first place. But how can one do that? Well, for starters, by avoiding questionable download sources and websites in general and also by never opening any obscure spam messages and fishy-looking ads. One very important thing that a lot of users tend to forget is to always go for the detailed setup options such as Advanced, Custom or Manual when setting up new software on your PC. Through those options, you should be able to see if there aren’t any bundled and potentially unwanted apps put inside the main program’s installers and leave them out if you think they are not to be trusted.
SUMMARY:
| Name | New.lightfoot.top |
| Type | Adware/Browser Hijacker |
| Detection Tool |
Remove New.lightfoot.top Virus
To remove New.lightfoot.top and stop it from interrupting you when you are browsing the web, this is what you must do:
- If there is a suspicious recently-installed program on your computer with which the hijacker may have been bundled, delete that program.
- Use the Processes tab of the Task Manager to identify any rogue hijacker processes and to stop them.
- Reverse any changes that the hijacker may have made in the system Registry, the Tasks Scheduler, the DNS settings, or the Hosts file. Also check the startup items list.
- You must also remove New.lightfoot.top extensions that may have been installed in any of your browsers, and then clear the browsing data.
For best results with the removal, we advise you to take the time to read the detailed instructions for each of those steps that you will find in the next lines.
Detailed New.lightfoot.top Removal Guide
Before you begin, it may help you with the removal process if you disconnect your PC from the Internet until you delete New.lightfoot.top. The idea is to stop the hijacker from reaching out to the servers of its creators and potentially acquiring resources from there that may hinder your removal attempts.
Step 1
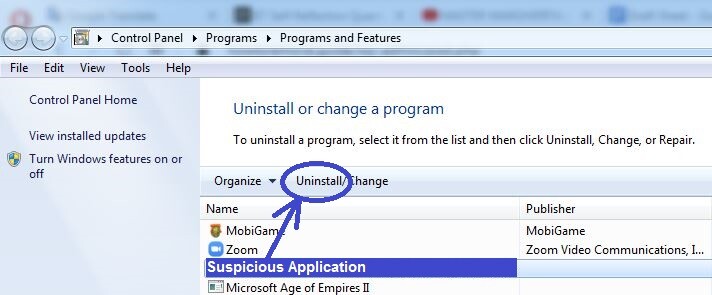
You can see what programs are currently on your computer by typing appwiz.cpl in the search bar of the Start Menu and by pressing Enter. Your task is to find anything that has been recently installed that may have secretly introduced New.lightfoot.top to your computer and browser. If such a program can be seen in the Uninstall a program list, click it, click Uninstall, and proceed with the steps of the uninstallation manager. While going through the uninstallation process, make sure that you choose the removal settings that would delete everything from the potentially undesirable program so that nothing from it is left on in the system.
If currently you are not allowed to perform the uninstallation, try again later, after the other steps from this guide have been completed.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
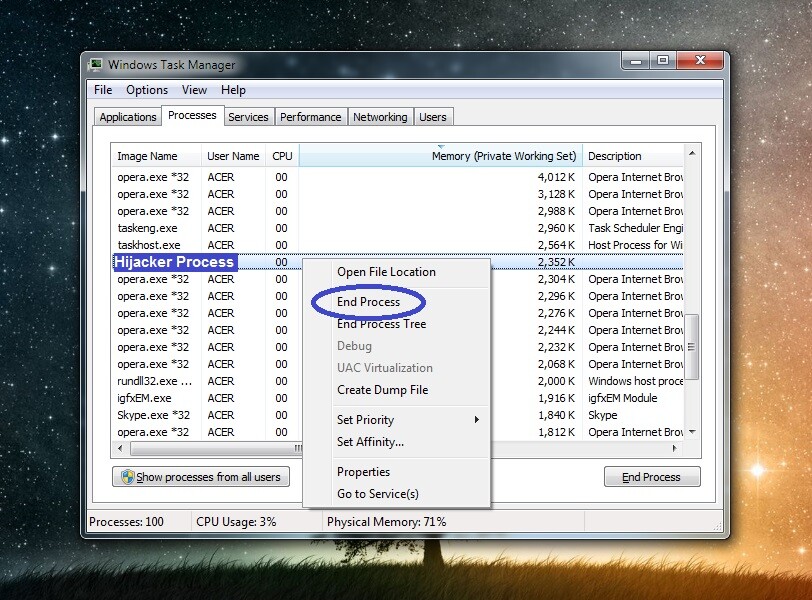
Press at the same time the Ctrl, Shift, and Esc keys and select Processes in the Task Manager window that will pop up on your screen. Now look through what items are shown in the list – you should be searching for anything that seems related to New.lightfoot.top and/or to the program you may have uninstalled in the previous step. Also, look for items that have unusual names and high usage of virtual memory and CPU (look in the Memory and CPU columns). If anything suspicious is found in the Task Manager, try to find information about that process on the Internet – there will likely be reports on cyber-security sites of that process being unwanted if it is indeed linked to the hijacker. Another thing you can do to figure out if a suspected process is rogue is to right-click on its entry from the list, click on Open File Location, and then scan each file in the newly-opened folder. We recommend using the free scanner we’ve provided below for that task.


If it turns out that any of the processes in the Task Manager is likely rogue and/or connected to New.lightfoot.top, find the directory where the File Location folder of that process is, then end the process (right-click on it and then select End Process), and finally erase the location folder.
Step 3
Some hijackers may have ways of re-launching their processes and restoring their data – prevent this from happening by entering Safe Mode.
Step 4
In this step, you will go to several areas/settings types of your system and attempt to override any changes that New.lightfoot.top may have made to them. To do this, open the Start Menu, and one by one type the items we’ve shown below in the search bar, pressing Enter after each, and then performing the respective actions for each item according to the instructions we’ve provided.
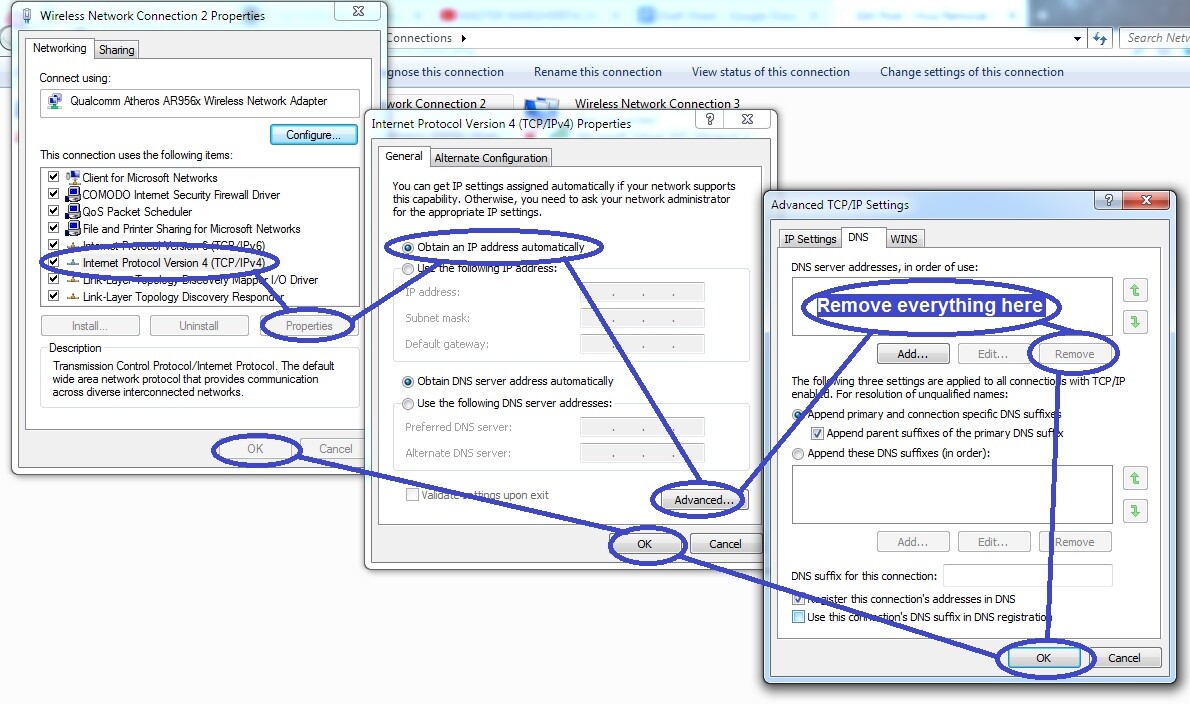
- Ncpa.cpl – In the Network Connections folder, right-click and open the Properties settings of the item that represents your preferred network. Find an item named Internet Protocol Version 4, double-click it, and, on the next page, click the Obtain an IP address automatically and the Obtain DNS server address automatically settings to enable them (if they are not enabled). Following that, go to Advanced, click the second tab (DNS), and delete anything that may be in the DNS server addresses list, after which select OK on everything.
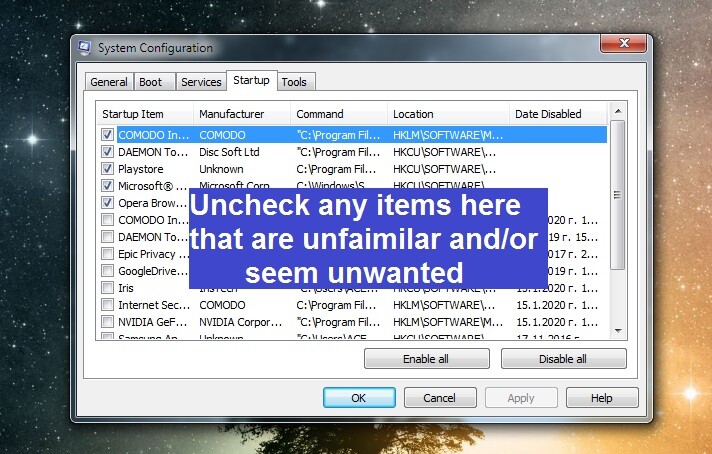
- msconfig – In System Configuration, go to Startup and there uncheck any items with unfamiliar or suspicious names or names that seem related to the hijacker or the program you uninstalled while completing Step 1. If you are on Windows 10, once open the Startup tab of the System Configuration window, you will first have to select Open Task Manager to get to the list of startup items.
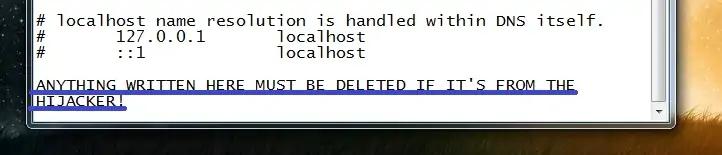
- notepad %windir%/system32/Drivers/etc/hosts – If the text file that opens (Hosts) has been modified by the hijacker, you should see IPs at the end of the text, right after the two “Localhost” lines. See if any IPs are listed there in your Hosts file and if you find anything, post it in the comments section below this post and wait for us to tell you if those IPs are rogue and if you will need to erase the from the file.
- Task Scheduler – After opening the Task Scheduler, open the Task Scheduler Library folder that you’ll see in the top-left, then look for rogue-looking and/or unfamiliar items shown in the list of tasks, and if you find anything that may need to be removed, right-click it and select Delete.

- regedit.exe – This is the executable of the Registry Editor, but before you could open it, Windows will ask you to allow the program to make system changes – click Yes when your permission is required.
In the Registry Editor, click on the Edit menu in the upper-left corner, then open the Find option, and type New.lightfoot.top in the small search bar window that opens. Click Find Next to perform the search and delete the item that gets found (if anything is found, that is). If an item was found, and you deleted it, perform another New.lightfoot.top search and erase the next thing. Rinse and repeat, until no more result for New.lightfoot.top are getting found. Also, you attempted to delete any program from the Uninstall a Program list in Step 1, search for items related to that program in the Registry Editor and delete them too.
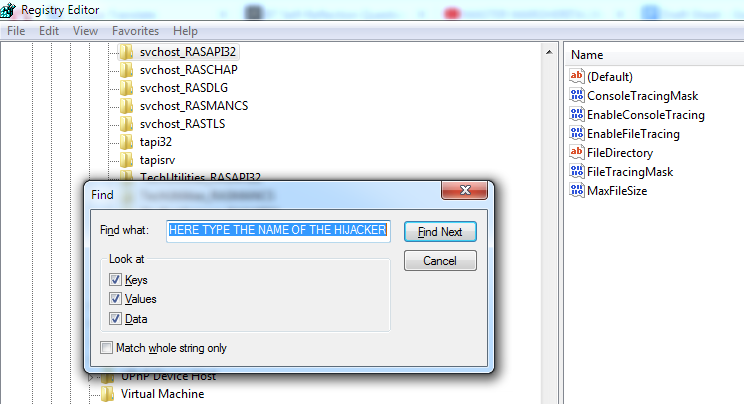
The final thing that you must do in the Registry is find the listed below directories (you can navigate to them in the left panel of the Registry Editor) and look for any subfolders in them that have unusual names – names that are long and seem to comprise randomly-arranged letters and numbers (something that looks like “093ur90343ur2094u290ri094ut“, for instance).
HKEY_CURRENT_USER/Software/Random Directory
HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
Step 5
Finally, you should ensure that your browsers are hijacker-free. Here’s how to do this:
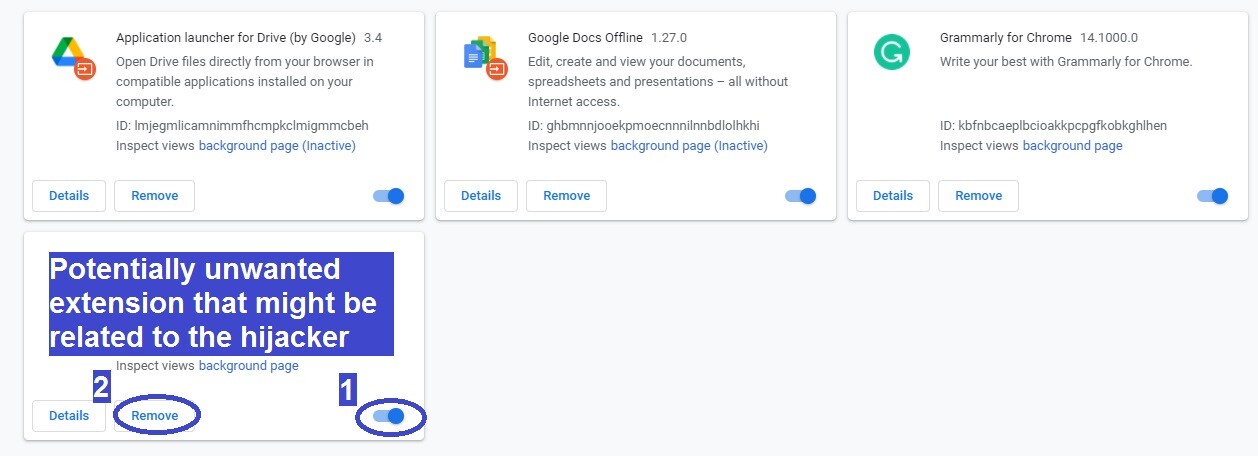
First, go to your main browser and launch it, open its menu (the menu icon of the majority of Windows browsers is in the top-right, the menu icon of the Opera browser is the big red “O” in the top-left). In the browser menu, click on Extensions (or Add-ons). If you are currently in Google Chrome, click More Tools > Extensions in the Chrome menu.
On the page with the browser extensions, disable anything that you don’t need and/or that you think may be related to New.lightfoot.top, and then delete that extension/s.
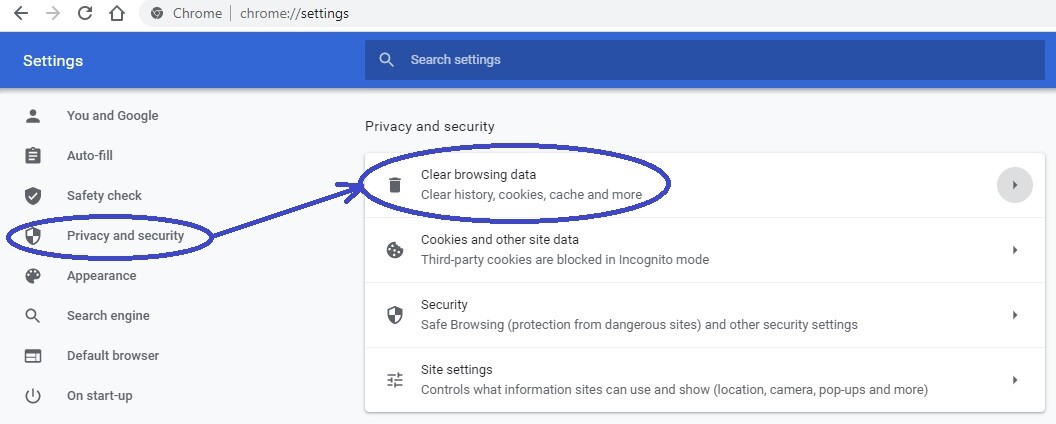
Click the browser menu again, click on Settings, and open the Privacy and Security section. If you don’t see Privacy and Security anywhere, then first click on Advanced and you should see it.
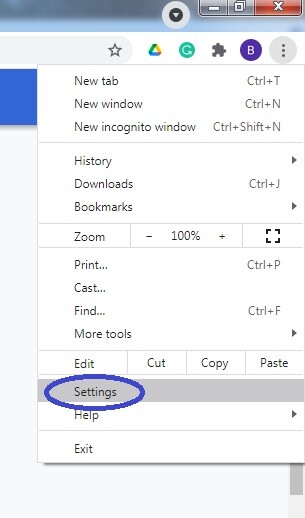
Locate an option labelled Delete browsing data/Clear browsing data/Clear data/Choose what to clear, and click it.
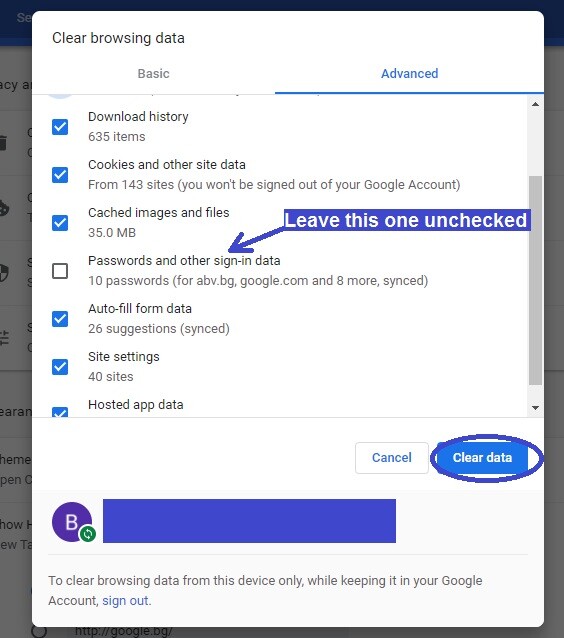
In the window that should pop up on your screen, select the Advanced tab if there is such a tab there, then check each data type except the Passwords saved in the browser, and then click on the Clear data/Clear option to delete any records that may have been left behind by New.lightfoot.top.
It’s important that the actions from this step are performed for every browser in the system and not only your main one.
If you are still having problems with New.lightfoot.top
If the problems with New.lightfoot.top persist, it’s possible that there are more rogue programs on your computer. For instance, Trojans and Rootkits are often employed to allow unwanted/rogue software to stay for longer in an infected system. This could be a possible reason why New.lightfoot.top is still in your system even after you’ve performed all the steps from the guide.
In such cases, it is advisable to clean the computer with a reliable anti-malware tool that can delete all rogue software in one fell swoop, thus not allowing the different rogue programs to help one another evade removal. If you are in a similar situation, we recommend using the security tool that is linked in the guide – it specializes in dealing with hijackers, adware, and spyware, while also being proficient at deleting Trojans and Rootkits, so it’s the perfect tool for the job.
New.lightfoot.top is a rogue application that generates aggressive ads and automatic page redirects inside Chrome, Edge, Firefox, and other popular browsers. New.lightfoot.top relies on file-bundling, spam online messages, and misleading browser pop-ups and links to get distributed and to attach itself to more browsers.
The purpose of software like New.lightfoot.top is to take control over certain settings and functions of the browser and to flood it with paid advertising materials. Remuneration models such as Pay-Per-Click and Pay-Per-View are employed in order to allow such browser-hijacking apps to generate income for their creators. This explains the reason why this type of software tends to be particularly aggressive and intrusive with its ads.
Although often referred to as viruses, most browser hijackers aren’t intended to cause harm to the systems they are installed in. That said, they are still undesirable programs and could be the source of numerous issues, especially if allowed to remain on the computer for extended periods of time.
New.lightfoot.top is not as dangerous as a Trojan Horse, a Ransomware cryptovirus, or another piece of advanced malware, yet it’s also not a safe app. The main dangerous aspect of New.lightfoot.top is its ability to automatically redirect the browser to potentially unsafe web pages.
If there is a hijacker like CaptchaResolverHere attached to any of your browsers, this means that using the infected browser would invariably lead to encountering numerous obstructive and potentially misleading ads as well as getting automatically redirected to sites that you don’t want to visit. For the most part, this is more of an annoyance rather than an actual security issue. However, it’s well known that browser hijacker creators aren’t picky with regard to the content that their software promotes. It is, therefore, perfectly possible (if not likely) that a rogue app like CaptchaResolverHere could land your browser on some sham or outright malicious webpage hosted by scammers or hackers and used to trick users into sharing personal details or downloading disguised malware such as Trojans, Spyware, Ransomware, etc.
To remove New.lightfoot.top, you will need to find and delete the program that helped it enter your program and also stop any rogue processes in the Task Manager. In addition, to remove New.lightfoot.top, you will also need to restore the regular state of your browsers.
There are four main steps that one must perform in order to manually delete this hijacker:
1. The first step is to carefully explore the Programs and Features list in the Control Panel, find in it any program that may be behind the hijacker infection and delete the said program.
2. The next thing to do is to open the Task Manager app and attempt to find and stop any rogue process that may be coming from CaptchaResolverHere.
3. The third important task is to revoke any unauthorized changes made by CaptchaResolverHere in the Hosts file, the Registry, the DNS settings, or the Startup items list.
4. Once everything else has been completed, the remaining thing to do is to get rid of any unwanted extensions in all your browsers, and then clear the browsing data (cookies, history, caches).

Leave a Comment