The new technique to avoid malware detection
A new example of how malware creators are evolving their methods to avoid malware detection has been spotted by security researchers.
Professionals have discovered a previously unseen technique that allows threat actors to download and execute malicious DLLs (ZLoader) without including any malicious code in the original spammed attachment macro.
Instances where ZLoader infections have been spreading through this method have recently been registered in the United States, Canada, Spain, Japan, and Malaysia.
According to cybersecurity researchers, the malware that is being distributed in this way is a version of the notorious ZeuS banking Trojan, and is famous for its ability to aggressively exploit macro-enabled Office documents as a way to sneak inside the system.
Once it successfully enters the attacked system, the malware can steal passwords and personally identifiable information from users of the targeted bank.
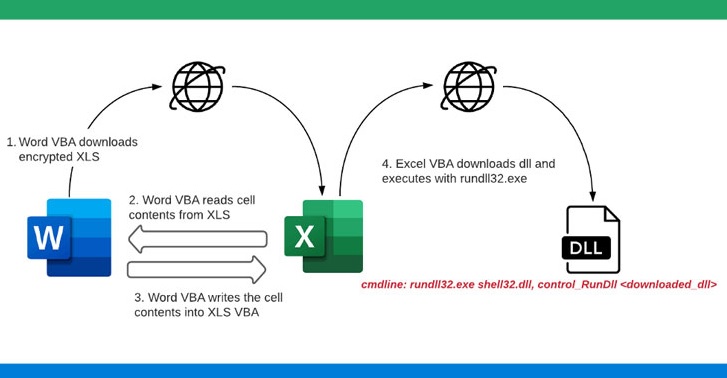
From what researchers have discovered, the infection chain begins with a phishing email attachment containing a Microsoft Word document that downloads a password-protected Microsoft Excel file from a remote server as soon as it is opened. It’s worth mentioning, though, that macros must be enabled in the Word document in order to initiate the download.
As per the details that are available, as soon as the XLS file is downloaded, Word VBA reads the contents of the cells in the XLS file, generates a new macro for the same XLS file, and uploads the contents of the cells to XLS VBA macros as functions.
When the macros are prepared, the Word document then changes the registry policy to “Disable Excel Macro Warning” and executes the malicious macro function included in the Excel file. Next, the Excel file downloads the ZLoader payload which then gets executed using Rundll32.exe.
By default, macros are typically disabled in most cases due to the huge security risk they pose and the number of malicious threat that use them as an initial attack vector. However, from what has been discovered, threat actors are creating very appealing and credible-looking social engineering lures to mislead users into activating macros. And with the macros security warning disabled, the attacks are often successful and can remain undetected for long.

Leave a Comment