Newsbreak.com
Newsbreak.com is a form of unwanted software that modifies a web browser’s settings without a user’s permission. Typically, Newsbreak.com replaces the default search engine or the homepage and injects unwanted advertisements into every web page the user visits.
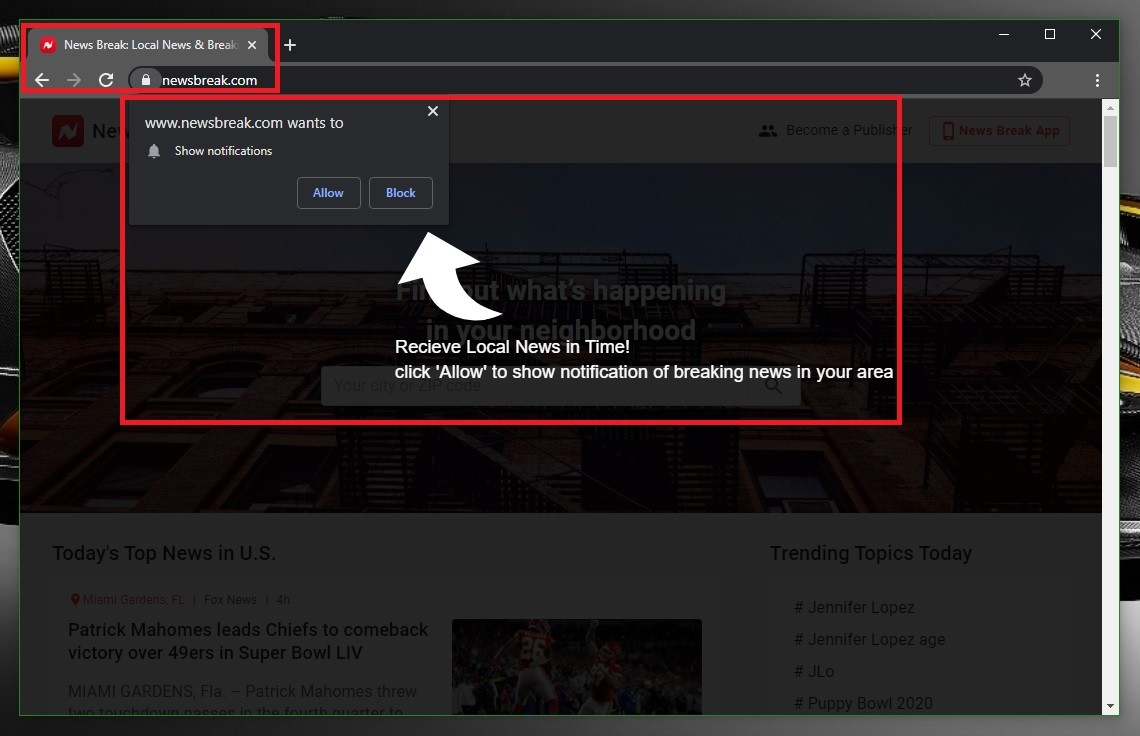
Newsbreak.com will try to trick you into subscribing to its notifications
The reason you reached this website is most probably the huge amount of pop-up ads, box messages, banners, and redirect links that have started to appear in your web browser lately. You may also have had your browser’s homepage or search engine changed, regardless of which browser you are using – Chrome, Opera, Firefox, Safari or another popular browsing app. You may have started to experience automatic redirects to different web pages full of sponsored content in addition to the other issues. These are all sure signs that you have been infected with a Browser Hijacker and, more precisely, one of the latest representatives of this software group, an app called Newsbreak.com. The intrusiveness of this application and the aggressive nature of the ads that it displays typically raise a lot of questions and are the likely reason you are seeking a way to remove it. Yet, before you scroll down to the removal guide that follows and learn how to uninstall Newsbreak.com, we suggest you read the information in the next lines and learn what’s under the iceberg’s tip and why you should be careful with this app.
Like any program that falls in the Browser Hijacker category, Newsbreak.com has been designed to distribute and strategically display hundreds of pay-per-click ads on your monitor. It typically does that in such a way that the ads are really hard to navigate past. The ultimate agenda is to collect as many clicks as possible on the displayed ads, because this is how the Browser Hijacker’s developers profit, thanks to a popular business strategy called pay-per-click.
Here, we would like to stress the fact that programs like Newsbreak.com are not the same as viruses and malware. Their presence on your machine and their ad-generating and page-redirecting activities may create browsing disturbance, but they are not intended to damage your computer. A real virus, on the other hand, has the ability to self-replicate, steal valuable information, spy on you, and extort money from you. A Ransomware, for instance, can encrypt your files, while a Trojan Horse can steal your passwords (among other things). A Browser Hijacker cannot perform any of these criminal actions.
However, we cannot ignore the fact that, in rare cases, programs such as Newsbreak.com may lead you straight to Ransomware, Trojans, and similar kinds of security hazards. They don’t do it deliberately but sometimes the pop-ups and the box messages they randomly display on your screen may not be what they seem. And if you click on them, they may redirect you to websites that are malicious. This is the main reason why our “How to remove” team advises the web users to avoid interaction with the hijacker’s ads, and why uninstalling this unwanted software as soon as possible is the best course of action.
Another thing related to the hijackers that is less dangerous in nature, but still disturbing is how the Browser Hijacker may affect the performance of your computer. Often the developers of such software will claim that if you install a program like Newsbreak.com, it will boost your browsing experience, or improve the safety of your OS. However, it may do the exact opposite, and ruin your browsing activities, not to mention how much system resources the hijacker may use to display so many ads, and how this activity may slow down your entire device, leading to issues like screen freezing and crashing of your browser. All of the above is precisely why we suggest you use the guide below and remove all of these problems by simply uninstalling Newsbreak.com from your machine.
SUMMARY:
| Name | Newsbreak.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Newsbreak.com
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment