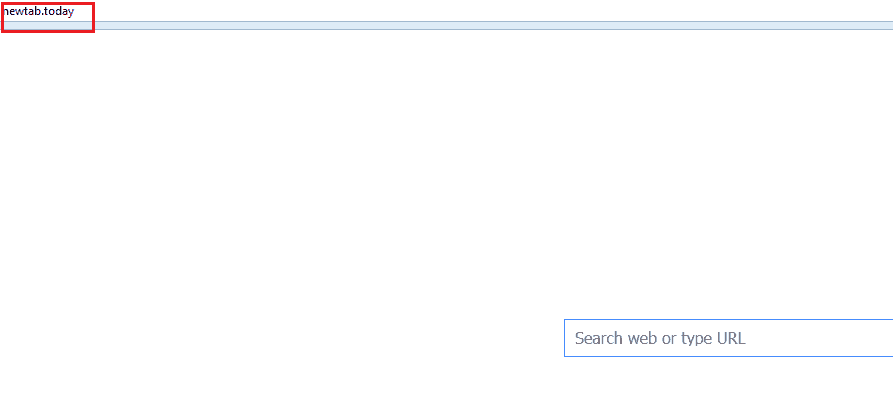
This page aims to help you remove Newtab.today. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Browser hijackers have been annoying users worldwide almost for as long as the internet has been around and not much has changed about them over the years. They still integrate with the Chrome, Firefox, Explorer or other popular browser, and change certain aspects of its settings. Most commonly these include setting a new browser homepage or changing the default search engine to a sponsored one, in addition to also adding a new toolbar. Furthermore, users often report that the new search engine redirects their searches to different unfamiliar pages they never intended to visit in the first place. Thus, even the newest browser hijackers like Newtab.today still exhibit these very same qualities, as well as a number of others that we will describe in this article. What’s more, since many users have concerns that Newtab.today may be a virus, we will address those as well and shed a little light on what software of this type is really all about. And last but by no means least, we will provide users with a set of useful instructions on how to remove this browser hijacker permanently, along with all its irritating symptoms.
Browser hijackers – how dangerous are they really?
Let’s start with the most pressing issue and that is whether or not you have something to fear from Newtab.today. The good news is that this is not a virus or harmful program of any type. Browser hijackers in general are considered to be potentially unwanted programs (PUPs), but that’s still pretty far from malware. However, they’re also not really in the same category as your average useful programs, such as the browsers you use, the games you play or the messaging programs you may use for communication. These are a type of programs that serve third parties and may have potentially negative effects on your system, especially over long periods of time.
Such are, for example, a noticeable slowdown of your computer. This is caused by the background processes that programs like Newtab.today run constantly, such as traffic data collection and the generation of all the endless popups, banners, box messages and other online ads on your screen. These activities consume valuable system resources such as RAM and CPU time, in addition to free disk space. So your system ends up overloaded with various unnecessary processes that certainly don’t benefit you in any way. Speaking of traffic data, you may or may not know that software like Newtab.today actually monitors your browsing patterns in order to extract certain important information for itself. This includes the sites your visit, the things you search for using the sponsored search engine, etc. And with the help of all this data, the hijacker can determine which of its ads will be more appealing to you, so it can then re-position them accordingly.
And the reason why these ads are so important to the developers of programs like this is because that it essentially their way of earning revenue. The majority of these popups and banners on your screen are all paid and the developers benefit from them as per Pay Per Click or Pay Per View remuneration schemes. Another important subject we should certainly touch on is the fact that Newtab.today could possibly also result in more serious consequences than a mere system slowdown. Due to the unwanted changes it can administer to your system registry in combination with the constant page redirects, you could face the risk of running into actual viruses like Trojans and ransomware. So from that perspective you can certainly consider Newtab.today to be a safety hazard.
For this reason, we think removing similar software the optimal course of action. And once you have done that you can also make sure that you don’t get infected again. The most common source of browser hijackers and similar advertising software is program bundles. These are seemingly regular programs that are typically distributed on various file-sharing sites for free. However, the developers include other programs in their installers, so that an inexperienced user will install them all without even realizing it. It’s likely you ended up with Newtab.today this very same way. And the trick is to simply customize the setup yourself by utilizing the Custom or Advanced option. It will give you more freedom to determine what goes in your system and what will be excluded.
SUMMARY:
| Name | Newtab.today |
| Type | Browser Hijacker |
| Detection Tool |
How to Remove Newtab.today
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment