Nlah
Nlah is a kind of malware that security analysts categorize as ransomware due to its ability to encrypt digital files. The attack of Nlah is very dangerous and can lead to irreversible loss of data for the victims.
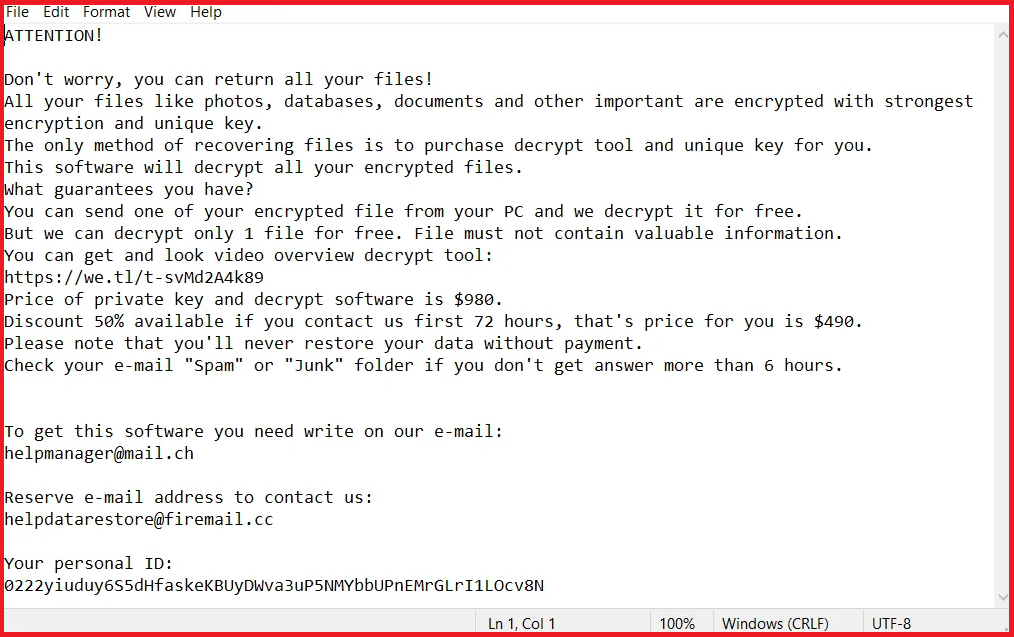
Once the Nlah Virus is finished with the encryption of your files it will display this message.
The viruses in the ransomware category like Nlah, Pezi and Mzlq are generally considered to be some of the most destructive and stealthy pieces of malware that can be found on the Internet. This is mainly because sometimes there may be no solution that can undo the encryption that these viruses apply to the files of their victims. You may be permanently restricted from accessing your digital documents, text files, images, videos, audios, personal collections, archives, databases and other types of files and not even sending the ransom amount that the hackers require will be able to guarantee that you can access them again. For one, the crooks may never send you the decryption key they promise and for another, since file encryption is a tricky process, there is a high chance that it may not be decryptable due to mixups in the code itself.
Still, this should not discourage you from seeking alternative solutions. Moreover, there are some methods that may potentially help you minimize the loss of valuable data and, on this page, we will tell you more about them. We also have a detailed guide that explains how to remove Nlah from your computer. However, whatever course of action you choose to go for, one thing is sure: before trying any data recovery method, make sure you have completely removed the ransomware virus from your device. This will ensure that no encryption will be applied to the files that you manage to recover or the new files that you will create.
The Nlah virus
The Nlah virus is a stealthy ransomware infection that is quite successful in remaining hidden from most antivirus programs. The Nlah virus can operate without triggering a response from the security software which helps catch its victims by surprise.
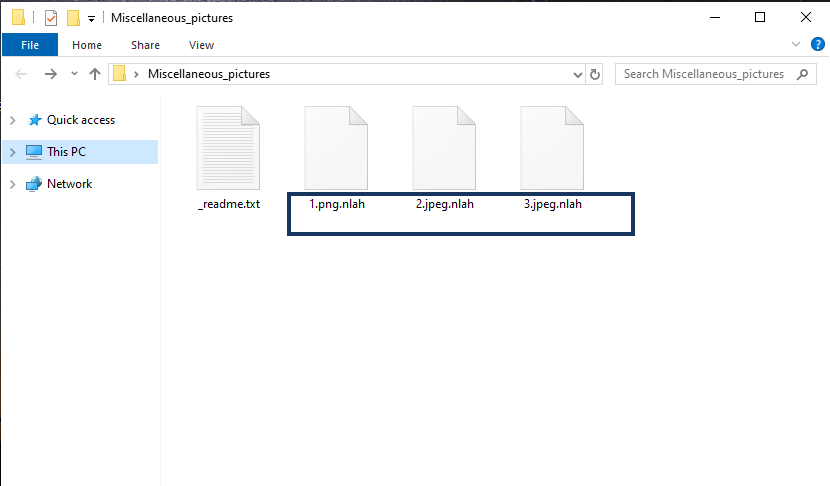 The Nlah Virus will start encrypting your files as soon as it has infected your system.
The Nlah Virus will start encrypting your files as soon as it has infected your system.
The stealthiness of ransomware infections like this one roots in the fact that the file encryption they use does not corrupt or destroy the files to which it is applied. Encryption, in general, is just a method for data protection that is used to limit the access of people who don’t have the corresponding file decryption key. It finds its wide implementation in many sectors where digital information should be shielded from unwanted eyes. Unfortunately, cybercriminals have found a clever way to exploit file encryption for their blackmail purposes by creating ransomware programs like Nlah.
Still, there is a simple and reliable way to protect your files and that is the good old file backup. By keeping copies of your most valuable data on an external drive, cloud storage or another device that is not connected to the Internet, you can always have access to your information. Even if ransomware encrypts the originals, the only thing that you will have to worry about is how to remove the infection so that you can copy your files back to the computer.
The Nlah file extension
The Nlah file extension is an odd combination of symbols and letters that is attached to the end of every encrypted file. The Nlah file extension replaces the regular file extension and effectively prohibits the identification of the file format by other applications.
SUMMARY:
| Name | Nlah |
| Type | Ransomware |
| Detection Tool |
Remove Nlah Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment