*Nood is a variant of Stop/DJVU. Source of claim SH can remove it.
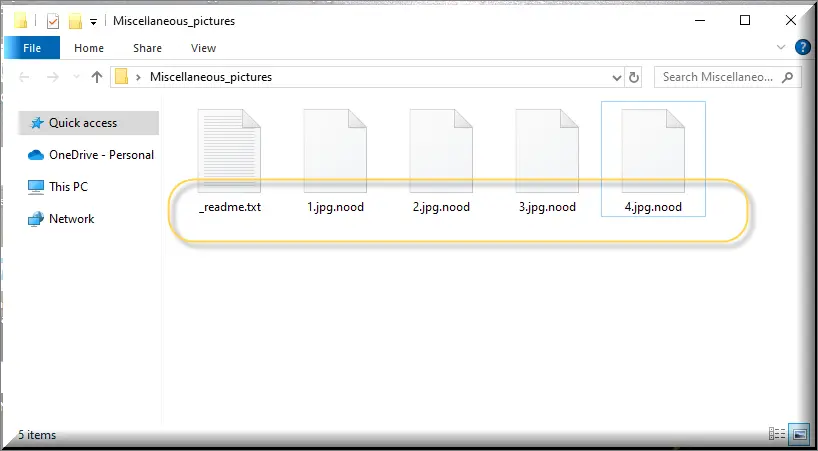
The Nood File
The Nood file encryption represents an emerging ransomware threat that employs sophisticated techniques to encrypt users’ files. It meticulously scans compromised devices for critical documents, images, archives, and databases, subsequently locking them using an intricate encryption algorithm. Attempting to access these files triggers a ransom demand notification, compelling users to pay a sum of money. Failure to comply with these demands could result in permanent data loss, with the ransomware displaying no discrimination between personal and work-related files. The Nood file encryption poses a significant danger to both individuals and organizations, highlighting the severity of this cybersecurity menace.
How to decrypt Nood ransomware files?
Decrypting files encrypted by Nood ransomware is no straightforward task. Its encryption methods are intricate and multi-layered. The first step is to identify the exact variant infecting your system. Armed with this knowledge, you can search for decryption tools tailored to that specific variant. However, a robust defense against ransomware encompasses not just recovery but prevention. This involves maintaining regular backups, keeping software updated, fortifying your system with reliable antivirus software, and resisting the temptation of paying a ransom, which are the cornerstones of cybersecurity in the age of ransomware.
How to remove Nood ransomware virus and restore the files?
Effectively removing the Nood ransomware and restoring the files necessitates a reputable antivirus software for a comprehensive scan and malware removal. If you have maintained backups, the path to recovery becomes clearer. In cases where decryption seems elusive, seeking legal remedies becomes essential. Prevention, however, remains the most potent strategy. Regular software updates, vigilant cybersecurity practices, and robust data backup measures serve as effective deterrents against future ransomware attacks.
The Nood virus
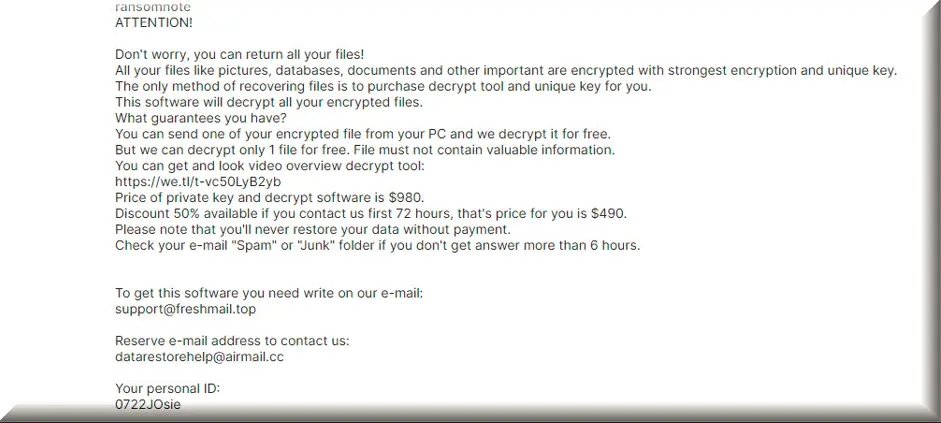
The Nood virus is a recent ransomware variant that specializes in seizing your data and holding it hostage. Once it encrypts your files, it demands a ransom to unlock them. Understanding where this malicious software typically lurks is crucial. Ransomware often infiltrates computers through deceptive email attachments, disguised as legitimate files, or via malicious links on suspicious websites. Once inside your system, the Nood virus targets files that are of high importance for the victim and demands payment for their release. Dealing with these threats can indeed be stressful, especially if you lack the knowledge to resolve them.
Nood
Dealing with the aftermath of a Nood, Wiaw or Wisz infection can be genuinely terrifying. While some may consider paying the ransom as a way to retrieve their data, it’s important to understand that compliance with the demands of some anonymous cyber criminals doesn’t always guarantee data recovery. Therefore, seeking assistance from experts is often a more reliable option. Additionally, maintaining up-to-date software is a critical preventive measure to thwart Nood ransomware attacks, as it helps fortify your system’s defenses against these insidious threats. And last, but not least, it is a great idea to develop a habit of regularly creating copies of your most valuable digital data on external drives or cloud storage because, in this way, you can always have access to it and easily restore it in case of a ransomware attack on your computer.
.Nood
The .Nood encryption applied to your files renders them completely inaccessible, leaving you with a demand from hackers to pay a ransom to regain access. If the locked files hold significant value, be it for work, education, or personal reasons, you may find yourself in the unfortunate position of having to pay a substantial sum to the hackers behind the virus to recover your data. The cyber crooks primarily employ the .Nood encryption for monetary extortion, using the locked files as leverage for blackmail. The good news is that removing the Ransomware is typically manageable. However, the real challenge arises when the files remain locked even after the virus is eliminated.
Nood Extension
There are different types of ransomware, and the one that ends with the Nood extension is one of the worst, as it prevents you from accessing your files. Even if you pay, there’s no promise of getting your files back. Another type is the so-called screen-locking ransomware, which doesn’t encrypt your files like the Nood extension, but makes your computer screen unusable by displaying a full-screen message on it until you pay. Some ransomware even targets mobile devices like phones and tablets. These ransomware variants can enter your device through emails, suspicious websites, or infected downloads, so it’s essential to be cautious when browsing the internet and avoid clicking on anything that looks fishy.
Nood Ransomware
The motive behind the attack of the Nood Ransomware is to enable the hackers responsible for the virus to extort a ransom from you in exchange for the decryption key. Some users might contemplate paying the ransom as a solution. However, the issue lies in the fact that even after sending the money, your files may remain locked and inaccessible. Trusting these individuals is risky as their promises regarding file restoration could prove false. Their primary goal is to extract money from you, with little regard for the fate of your data. Therefore, our suggestion in to seek other solutions for Nood ransomware removal and file recovery, such as those that you can find in the guide below.
What is Nood File?
A Nood file is just a regular file on your computer that the ransomware has locked. You usually need a special key to unlock it. To avoid this problem, always back up your files. If you get hit by ransomware, it might be worth asking an expert for help, even if it’s costly. You can also look online, where people might share ways to deal with it. Removing the virus is the most important step, and you can follow the removal steps provided below. Once the virus is eliminated, you can explore the Nood file-recovery section of our guide for alternative solutions. While we can’t guarantee success, it’s worth trying these options before considering paying the ransom.
SUMMARY:
| Name | Nood |
| Type | Ransomware |
| Detection Tool |
*Nood is a variant of Stop/DJVU. Source of claim SH can remove it.
.Nood Ransomware Removal

Ransomware-based malware like .Nood is notoriously difficult to remove. In order to make things as simple as possible, in this first step, you should save this page as a bookmark in your browser so you can have immediate access to it.
Next, restart your computer in Safe Mode (follow this link with instructions if you need assistance). It will be simpler to notice ransomware-related background activities when your computer is in Safe Mode and just the bare minimum of apps are running.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Nood is a variant of Stop/DJVU. Source of claim SH can remove it.
The only way to fully get rid of .Nood’s malicious activity is by stopping everything that’s connected to it.
Open the Processes tab in the Task Manager (CTRL+SHIFT+ESC) for a comprehensive look at the present condition of the system.
The first thing you should do is search for processes that are associated with the ransomware. If you find a potentially harmful process, right-click on it to open a menu with the option Open File Location.

If you have any reason to believe the files of that process are malicious, you should have a virus scanner check them out.

If the files come as malicious after the scan, you may end the process by right-clicking on it and selecting End Process from the list of options that pops up. After that, delete all of the dangerous files associated with it and their folders.
Keep in mind that the ransomware may run more than one malicious process. So, pay attention and check the files of any program that raise a red flag for you.

If your computer has been infected with a dangerous software such as the .Nood ransomware, you should definitely look for signs of a hack. Copying and pasting the following into the Windows search bar should work:
notepad %windir%/system32/Drivers/etc/hosts
As soon as you’ve pressed Enter, a Notepad file named Hosts will open. Go to Localhost in the text and look for suspicious IP addresses:

If nothing unusual catches your attention, you may safely close the file.
If you detect any malicious IP addresses, such as the ones shown above, report them to us in the comments below this article. Then, please bear with us while we look at them and get back to you as soon as possible.
Many harmful programs may operate invisibly by altering the system’s startup options or the options in other important system settings. As a result, it’s critical that you search your System Configuration and open the Startup tab to check what is going on there.
Type msconfig in the Windows search field and hit enter to open System Configuration.
Next, click on the Startup tab and check if there are startup items that are not legitimate.
There are several ways to detect apps that don’t seem to belong in any of the default startup programs. For instance, an item with an “Unknown” Manufacturer should catch your attention. The same is valid for items with random names.
If you find anything unusual, carefully disable it (remove its checkmark), after that click the OK button at the bottom of the screen to save your changes.


*Nood is a variant of Stop/DJVU. Source of claim SH can remove it.
The majority of malware infestations might add potentially harmful registry entries to the system. Therefore, in order to remove .Nood, you need to open the Registry Editor (type Regedit in Windows search bar and press Enter) and search it to see if there are any ransomware-related files or folders that need to be deleted.
You can save time by entering the malware’s name into a Find box (press CTRL+F on the keyboard) and start a search by clicking on the Find Next button. Then remove any ransomware-related entries that have been found.
However, if you’re not familiar with registry files, you should proceed with caution when deleting any discovered entries. If you delete them without actually knowing what are you doing, you risk removing genuine data from other apps that aren’t linked to the infection, and this might damage your system.
In order to get the best results, we recommend that you use a ransomware removal tool like the one linked in this post and do a thorough system scan with it. As a result, the registry will be clear of harmful files you’re unaware of, and you’ll be protected against unintended system damage caused by deleting valid files by accident.
If you can’t find anything related to the ransomware’s name with the Find function, then you may need to manually go to each of the following five locations:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Simply copy each of them in the Windows search field and press Enter to open it. Then, search for any recently added files and folders that look suspicious.
Finally, open the Temp (Temporary Files) folder and select everything that is inside. You should remove these temporary files if you want to get rid of all traces of .Nood from your computer

How to Decrypt .Nood files
In the aftermath of a ransomware attack, multiple strategies exist for restoring encrypted archives. But, it’s important to understand that the success rate is intertwined with the particular ransomware that has contaminated your files. The cornerstone of your recovery journey is pinpointing the exact ransomware type, which is possible by lookint at the encrypted file extensions.
New Djvu Ransomware
The latest representative in the Djvu ransomware landscape is the STOP Djvu malware, marked by the .Nood extension on encrypted files. A dedicated decryptor fitting this version is available through the link below.
How to Decrypt
Initiate by downloading the decryption tool on your computer and launching it up with elevated rights. Before navigating further, get acquainted with the outlined terms and conditions. Activating the “Decrypt” feature gets things underway.
It’s important to comprehend that this tool might be ineffective against cryptographies driven by new offline keys or online encryption methodologies. Should you have any uncertainties or thoughts, feel free to use the comments section below this post to share them.
Attention! Before delving into decryption, meticulously inspect your computer for traces of malignant ransomware remnants and rogue registry inputs. For cleaning your device of malicious content, use the vouched-for security software and the online virus scanner on this page.

Hello sir! I got the ransomware and all my files has .NOOD, please help me, all my files are important.
please help me, i got the new .nood ransomware
Hi,Jerome, the antivirus program on our site will help you remove the virus(es) on your computer that caused the files to be encrypted. If your files are encrypted by an ONLINE KEY you will not be able to decrypt them. If an OFFLINE ID is available for the variant you are dealing with and your files were not decrypted by Emsisoft Decryptor, then you most likely were encrypted by an ONLINE KEY and those files are not recoverable (cannot be decrypted) unless you pay the ransom to the criminals and receive the private key if your files were encrypted with an ONLINE KEY, the only other alternative to paying the ransom, is to backup/save your encrypted data as is and wait for a possible future solution.
i have also this .nood virus.. and all of may videos and important files are encrypted or lock…. it is more than 2 tb files… i hope some IT expert got this solutions
Hi elcho,
by any chance do you know if you are infected by offline or online encryption? did you check the link at the end of the guide? There is a decryptor that can tell you that.
online encryption.