The threat actors are North Korean hacking group
Back in January, Google’s Threat Analysis Group (TAG) reported the discovery of a hacker group operating from North Korea that targets cybersecurity researchers. Apparently, the members of the group pose as fellow researchers to gain the trust of their potential victims and lure them into exposing themselves to cyber attacks.

According to Google’s TAG team, the hacker group is most likely backed and sponsored by the ruling party in North Korea. The TAG team also reported that the members of the hacking group have established an extensive network of fake social media account profiles designed to gain the trust of potential targets of the group. Among the social media platforms where hacker profiles have been found are Twitter, LinkedIn, and Keybase. Additionally, the hackers have created a fake cybersecurity blog and used their social media profiles to link to it in order to increase their perceived credibility.
The main tactic of the hackers would be to reach out to their targets (who mostly are cybersecurity researchers) with an offer of collaboration on some security research. If the potential victim takes the bait, the hacker would usually send them a Visual Studio project loaded with malware that serves as a backdoor. In other instances, the targeted researcher may be lured to go to a fake cybersecurity blog that contains browser-exploiting malware.
The SecuriElite hacker company
Yesterday, on the 31st of March, Adam Weidemann, a member of the Google TAG team gave an update on the situation with the North Korean hacker group. He reported in a post that the hackers have modified their tactics in an attempt to gain more credibility by creating an entire fake cybersecurity company with its own website and profiles on social media that link to it.
The name of the fake company is SecuriElite, and it has apparently emerged on March 17. According to the company’s site, its operation is based in Turkey, and it focuses on providing its clients with host security assessments, penetration tests, and exploits for different operating systems and software products.
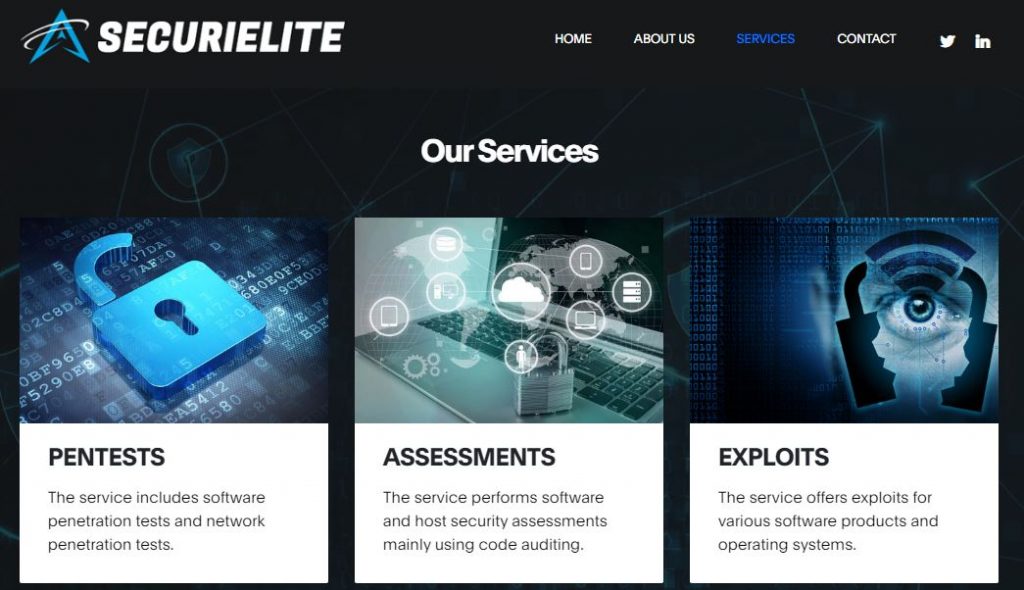
A PGP public key is linked on the website to supposedly further increase the company’s credibility, but the hacker group is already known for using misleading links in order to trick its targets into opening a page that contains browser-exploiting scripts.
Furthermore, the members of the fake company’s team, too, have their own social media profiles, which are different from the ones used by the hacker prior to the emergence of SecuriElite. Their goals are the same – to lure researchers by recruiting them to a research collaboration or by making them a job offer. However, with the added credibility of a (fake) cybersecurity company at their back, the likelihood of success goes up. In one occasion, one of the hackers even presented themselves as the Human Resources director of a company called “Trend Macro” – a blatant attempt at gaining the victim’s trust through association with the legitimate and well-known company Trend Micro.
Measures Taken
Google’s TAG team established a link between the North Korean hackers and Internet Explorer zero-day attacks that took place at the beginning of the year. According to the team, it is highly probable that the hacker group now has access to additional exploits that they would use against any potential victims they may manage to lure in the future.
Google has already reported the known fake profiles linked to the hacker group to the respective social media platforms and has added the SecuriElite website to Google Safebrowsing.

At the moment of writing, both the SecuriElite Twitter and LinkedIn accounts have been suspended and a Google warning comes up if you try to visit the site from the Google search engine. However, the site itself is still up, and it is highly possible that some of the fake social media hacker accounts are still up, so the threat isn’t fully gone and so cybersecurity researchers are advised to stay alert and watch out for any requests made to them that could be traced back to the fake company’s site or that come from other organizations or individuals the credibility of which cannot be confirmed.


Leave a Comment