Notification-phone1.best
Notification-phone1.best falls into the category of so-called browser hijackers for iOS devices such as iPhones and iPads. Notification-phone1.best embeds itself in the main browsing program on these devices and significantly alters their behavior.
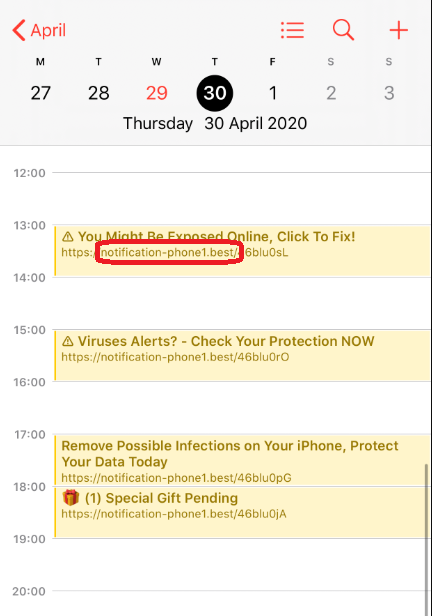
The Notification-phone1.best Virus will spam your calendar.
Hence, Notification-phone1.best can integrate with Safari, Chrome and most other web browsers that are compatible with Apple devices. But what’s important is the actual changes that they start making to the browsing program in question. Namely, these include the replacement of the homepage and/or default search engine with new web addresses. In addition to that, users begin to experience page redirects that take place spontaneously during their online sessions and send them to various sponsored sites.
Furthermore, software of this type is particularly well-known for generating popups, banners and various other types of online ads on the screen of the infected device. This is perhaps one of the most frustrating functions of apps like Notification-phone1.best, as it interferes with people’s browsing experiences more severely.
The only way you can rid yourself of all these unwanted effects, however, is by removing Notification-phone1.best itself. And although this process may not seem too intuitive, we have prepared a removal guide for you below that will show you exactly what steps to take in order to quickly eliminate this hijacker.
And just to ease your concerns, if you have them – Notification-phone1.best is not a virus. This is a common misunderstanding that many users have regarding browser hijackers. But the only association that software like this has with viruses is that its representatives may potentially expose you to unsafe web locations that, in turn, could be harboring ransomware, Trojans or other malware.
SUMMARY:
| Name | Notification-phone1.best |
| Type | Browser Hijacker |
Notification-phone1.best iPhone Removal
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and clean up your phone’s calendar events if they are infected.
2. Find browser extensions related to the threat and how to remove them.
3. Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment