*Source of claim SH can remove it.
Null Mixer
When it comes to malware, Trojans top the list as the worst and most complex threats that you may encounter. And since we’re talking about these kinds of threats, Null Mixer is one of the newest Trojan horse infections that has been found.
Our goal in this article and the Null Mixer removal guide that you will find below is to provide you with as much information as possible regarding the potential dangers posed by this kind of malware, the ways in which you are most likely to get infected, and the steps you can take to remove it from your computer. Hopefully, after you read it, you’ll be able to better understand the problem you’re up against and the measures you can take to prevent similar threats in the future.
What can the Trojans do?
The Trojans share a number of characteristics, but one of the most prominent is their versatility. Though we can’t tell you exactly what type of damage Null Mixer is doing on your computer, we can describe the most prevalent scenarios in which such a Trojan may be used:
Data corruption and deletion are two common outcomes of Trojan attacks. There are several professional contexts in which this may be the case, such as when a competitor is seeking to get rid of sensitive information that you may be in possession of. In fact, a Trojan might quickly wipe out everything on your disks and drives by formatting them.
Theft and eavesdropping. Hackers may monitor your computer’s activity with the use of Trojans like Null Mixer. They may remotely see and listen in through your camera and microphone. That way, the bad guys behind the malware can learn about your surroundings, your personal and professional life, and anything else that might give them an edge and allow them to blackmail, rob, and harass you. These are all very dire outcomes that must be considered very seriously.
Exploitation of system resources. Null Mixer is a Trojan horse that may be installed on your computer for system exploitation purposes. Thanks to the malware, your PC might be used in botnets to distribute spam or infect other machines on the same network. The percentage of computers used as bots thanks to Trojan infections is shockingly high—around 15% of all computers worldwide. The mining of cryptocurrency and the subsequent transfer of that crypto to the virus’s creators is another possible use of such malware.
Malware backdooring. If you are infected with a Trojan like Null Mixer, it may act as a go-between for you and some other malware, such as a ransomware crypto-virus that’s trying to encrypt your files. In this scenario, the Trojan will first compromise your computer and then download another virus to it.
NullMixer
It’s no surprise that NullMixer infection methods are as varied as their uses. Viruses like NullMixer are distributed throughout the Internet via social engineering to fool unsuspecting users into downloading the malware.
Spam emails are likely the most effective distribution strategy for this particular type of malware. The spam emails may pretend to be from legitimate organizations, such as banks, utility providers, or popular online retailers. These emails often include either an attachment to download and open or a link to click on.
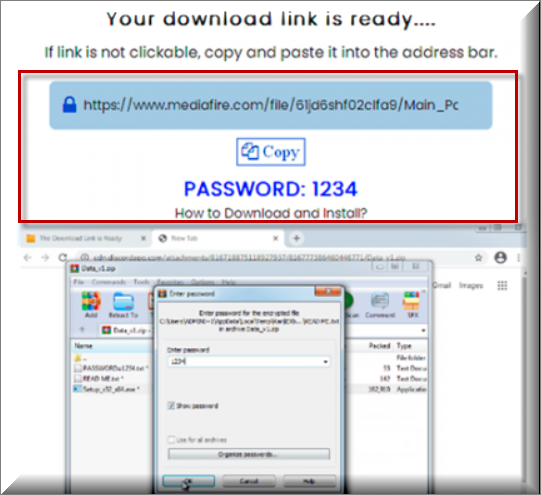
In addition, threats like Null Mixer might be found on malicious or otherwise questionable websites. The malware might be concealed in a piece of digital media like a movie, game, or torrent file. Or, it might be included in a pop-up or banner ad, and when you click on it, you’ll be sent to a website that will download the malicious software that was embedded in it.
The best way to protect yourself is to avoid any content that seems suspicious, and to buy good antivirus software that can find and remove potential threats before they can do any damage.
SUMMARY:
| Name | Null Mixer |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Remove Null Mixer Malware
If you are looking for a way to remove Null Mixer you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for Null Mixer and any other unfamiliar programs.
- Uninstall Null Mixer as well as other suspicious programs.
Note that this might not get rid of Null Mixer completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment