Oadesovern
If your Apple iOS device has been infected with Oadesovern, then you have landed yourself what is known as a browser hijacker infection. Browser hijackers like Oadesovern are not inherently harmful, but their presence on your device is still rather undesirable.
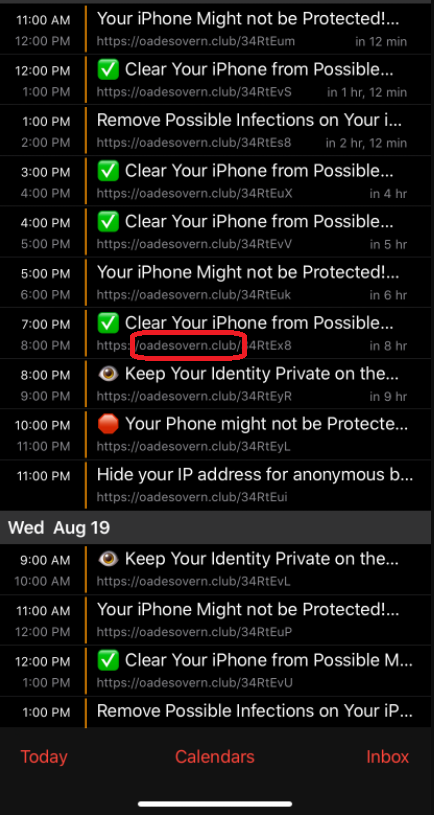
The Oadesovern Virus will spam your calendar with fake notifications.
Browser hijackers like Oadesovern, Click Subscribe and Smmsky.co are tools designed to generate paid banners, popups, box messages and various other forms of online ads directly in the browsers of web users. And to do this, they tend to embed ad-generating components in the Chrome, Safari or other main browser of the infected device. Furthermore, they also have a tendency to meddle with the settings of said browser.
For instance, they may change the default search engine to one that better suits their agenda. And they may also replace your browser homepage with a new one that they are tasked with driving more traffic to. Similarly, browser hijackers like Oadesovern have garnered a reputation for triggering sudden page redirects during browsing sessions – also with the aim of popularizing certain pages.
However, the above is fraught with risks of landing on unsafe websites and potentially even of encountering viruses and malware. That is not to say that Oadesovern is itself a virus, too, though. Browser hijackers don’t possess the harmful capabilities that Trojans, ransomware and other actual malware representatives do.
But that risk alone is grounds enough to remove this browser hijacker from your iPhone or iPad. And to assist you with this task, we have put together a removal guide that you will find right below this post.
SUMMARY:
| Name | Oadesovern |
| Type | Browser Hijacker |
Remove Oadesovern Virus
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and clean up your phone’s calendar events if they are infected.
2. Find browser extensions related to the threat and how to remove them.
3. Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment