OfferCore is a browser hijacker application that can affect the way your web browser functions. OfferCore is known for delivering sponsored search results and ads on the screen by replacing the main browser’s search engine and homepage.
What is OfferCore?
OfferCore is a typical browser hijacker. It can modify your browser’s homepage and designate a new search engine as the default. During its presence on your computer, you may encounter incessant page redirects and an onslaught of aggressive ads, banners, and pop-ups across various websites. OfferCore can seamlessly integrate with nearly all well-known browsers, such as Chrome, Firefox, Edge, and Opera, taking control of them. Regrettably, restoring your browser’s settings to their former state and removing browser changes is only possible by completely uninstalling the browser hijacker. To aid in this process, we offer an in-depth removal guide to help you locate and safely eliminate OfferCore. Additionally, a professional removal tool is available to scan your computer for this and other undesirable software.
What is a OfferCore?
OfferCore is a potentially unwanted program (PUP) that is often categorized as adware. It is known for delivering intrusive and unwanted advertisements to users while they browse the internet. OfferCore may come bundled with other software and can be installed on a user’s computer without their explicit consent.
How do I get rid of OfferCore virus?
To remove the OfferCore virus from your computer, follow these steps:
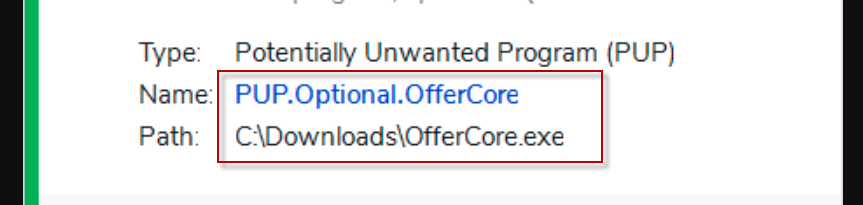
1. Use reputable antivirus or antimalware software to scan your system and detect any traces of OfferCore.
2. Uninstall any suspicious programs related to OfferCore using the “Add or Remove Programs” feature in your computer’s settings.
3. Remove any OfferCore browser extensions or add-ons from your web browsers.
4. Reset your browser settings to their default values to eliminate any browser hijacking caused by OfferCore.
5 Clear your browser’s cache and cookies to remove any remnants of OfferCore.
What is Pua Win32 OfferCore?
Pua Win32 OfferCore refers to a potentially unwanted application (PUA) that belongs to the Win32/OfferCore family of adware. It is known for displaying unwanted advertisements and potentially causing browser redirects. Pua Win32 OfferCore is often bundled with other free software and can be inadvertently installed by users.
What is Win32 InstallCore?
Win32 InstallCore is a type of potentially unwanted program (PUP) that is often associated with unwanted software installations. It is known for bundling additional software with legitimate downloads and can result in the installation of unwanted applications or browser extensions. Win32 InstallCore is typically classified as adware due to its intrusive advertising behavior.
The OfferCore virus
The primary objective of the OfferCore virus, like other browser hijackers, is to generate a multitude of online ads. As you initiate new browsing sessions, you may be bombarded with an array of pop-ups, banners, promotional messages, and vivid notifications encouraging you to click on various items. If you find yourself on this page, it’s likely that the hijacker’s activities have become too invasive to bear, and you have come to the realization that they cannot be stopped. This is because the ad creators compensate the browser hijacker developers to maximize ad exposure. In fact, the hijacker developers receive payment from advertisers based on user clicks on ads, following remuneration models such as the notorious Pay-Per-Click, which primarily governs the actions of programs like the OfferCore virus.
How OfferCore achieves its goal
In an attempt to increase user clicks and generate higher revenue for developers, browser hijackers like OfferCore typically that control of the default browser, installing a new homepage that directs users to specific sponsored sites. They may also swap the primary search engine with one that produces sponsored results and pay-per-click ads. In some cases, browser hijackers may further extend their reach by rerouting your web searches to sites tailored to your interests and recent search inquiries.
Nevertheless, being exposed to random sites featuring intrusive web ads like Wigglewurm or Just Cool Captcha is not only bothersome but can also inadvertently lead to encounters with security threats such as Trojans, ransomware, and other malicious software. This prospect can be quite alarming, and there are legitimate reasons to be cautious and avoid the sponsored content that OfferCore displays. It’s worth noting that seemingly legitimate ads can be employed to disseminate a wide range of computer infections. In fact, numerous ransomware cryptoviruses exploit infected ads to target web users.
As a precaution, we recommend our readers steer clear of arbitrary pop-ups, banners, and similar advertisements, and take appropriate measures to remove their source. There is no justification for jeopardizing your computer’s security by inadvertently engaging with potentially deceptive content.
SUMMARY:
| Name | OfferCore |
| Type | Adware |
| Detection Tool |
How to remove OfferCore Virus
To try and remove OfferCore quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the OfferCore extension (as well as any other unfamiliar ones).
- Remove OfferCore by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of OfferCore and any other suspicious items.
If this does not work as described please follow our more detailed OfferCore removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove OfferCore from Internet Explorer:
Remove OfferCore from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
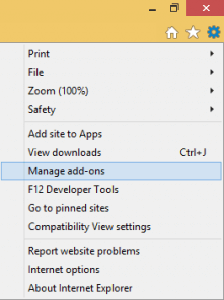
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
![]() Remove OfferCore from Firefox:
Remove OfferCore from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

![]() Remove OfferCore from Chrome:
Remove OfferCore from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
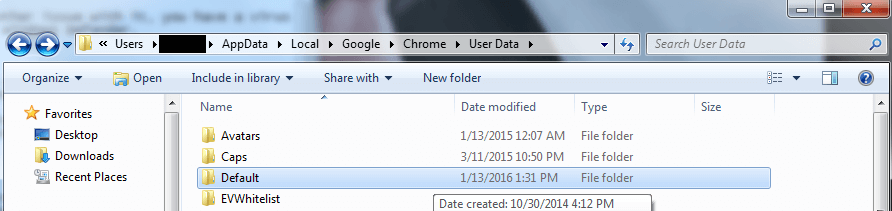
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment