This page will help you to understand the potential harm the Onclicktop.com Virus could cause to your PC and personal information. The Onclick.com Virus removal information and guide are suitable for all versions of Windows. It is valid for all browsers: Chrome, Firefox and Internet Explorer.
Introduction
Onclicktop.com Virus is considered to be one of the least harmful viruses. However, it is normal for people not to get scared or to become alert enough when they hear the word “least”, BUT in reality a virus is a virus. When a virus enters your body it eventually makes you sick, though, sometimes slowly. PC systems work the same way: they slowly get harmed, but there is a treatment, i.e, a safe removal process that can ‘heal’ them.
What is the Onclicktop.com Virus?
Have you ever wondered why there are more ads on your screen than you wish to look? Have you ever wondered why you computer suddenly turn on “automatic mode” and random browsers and/or websites open without you doing anything? This is what Onclicktop.com Virus are: excessive random opening of websites and/or too much pop-up ads on your screen. Hackers are smart people and they know how to make things look attractive to you, so that you go to their malicious content and do their job. It is always safest not to click on unfamiliar links and/or content and to uninstall immediately everything you find suspicious or is asking for paid updates.
How harmful is the Onclicktop.com Virus and what are some ‘red lights’ to look out for?
As we said, every virus is harmful. Onclicktop.com Virus could infect your system to the point where you could experience slowness in the work process, randomly copied and/or misplaced files on your computer and when you open the copied one it turns out to be empty, missing files, blockage of certain programs on your PC, random glitches, etc. Hackers use viruses to get to your personal files, passwords, stored information on the internet, to track your browsing habits or words typed. That way they literally follow you and know every single thing you do and/or watch on your PC. They use all information obtained for illegal and malicious purposes. Thus, we advise you to strictly follow the removal guide so that you don’t become one of their victims.
Which browser should I use?
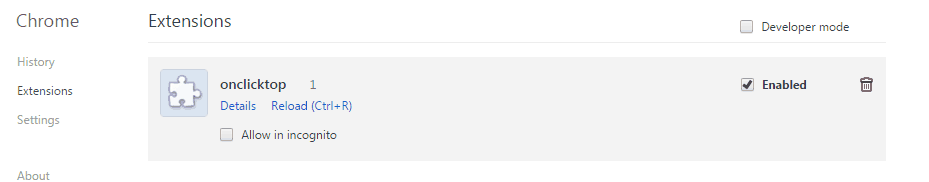
You can use any browser you want: Chrome, Firefox or IE (Internet Explorer). However, the Onclicktop.com Virus is most commonly found when using the Chrome browser. Why? Because of the privacy and security settings, as well as the fact that statistics show that Chrome is the most preferred browser to be used, makes it even a more desirable target for hackers and easier to spread malicious viruses. Firefox, on the other side, has tightened up their security practices. For instance, flash is no longer available, so if you want to watch a video on YouTube, per say, you have to download it through a third client. Internet Explorer belongs to the “older generation”. It is mostly used by folks who are not used to the two newer browsers. Because of the low number of users and lack of proper maintenance it makes itself a very easy target to those willing to damage your PC or steal your private information. Usually, people who use Internet Explorer are not very tech-savvy and not too well educated on computer viruses and their potential harm, so that eases the hackers even more.
What should I avoid?
- Avoid clicking on random banners that pop-up on your screen;
- Avoid viewing unfamiliar websites or the ones with shady URLs;
- Watch out for ‘crazy’ hyperlinked texts as some are simply lies;
- Pay close attention to what you are downloading and always scan the downloaded files;
- Anything offered for free in the form of coupons or prices raises a red flag. Remember that there is no such thing as free lunch.
SUMMARY:
| Name | Onclicktop.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Onclicktop.com Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment