Only Application
Only Application is a fake program that installs itself and asks for the user’s account and password credentials to initiate changes. Considering it was not installed with user consent, this makes Only Application a password-stealing trojan.
It can be quite unpleasant to get infected with a Trojan Horse like Only Application. Removing the malware can also be challenging because it can be very difficult to detect it inside the system. But letting the panic take over you is the last thing that would help you successfully remove the Trojan. That’s why we suggest you read the guide below, as it will give you some comprehensive explanation of how Only Application works, and what steps you can take to clean your computer from it.
Usually, a threat like Only Application can sneak unnoticed inside your system when you interact with seemingly harmless (but compromised) links, applications, email attachments, pictures, ads, torrents, videos, or whatever other type of internet content you might think of. The moment you interact with the malicious transmitter, the Trojan typically gets inside your system without visible symptoms. Due to this stealth, in many cases, the victims may need months, or even years to realize that a damaging threat has been lurking in their computer. What is more, it is difficult to identify the malicious operations of a Trojan, as they typically run in the background of the system. This is one of the main reasons why the cyber criminals love Trojans like Only Application so much, and use them commonly as tools for the completion of various types of crimes.
What is Only Application?
Only Application is a trojan horse infecting Mac users through unknown means. It displays malevolent behavior by asking for the user to input his password, which it then sends back to whoever created Only Application.
Trojan horses can be programmed to perform a variety of illegal acts. Practically, the list might be unlimited, but below you’ll see some of the most common, and feared activities the hackers could use this kind of software for:
- Ransomware distribution – Trojans might be engaged in distributing terrible threats like Ransomware, and other viruses. In most cases, the malware can act as a backdoor for the other virus infection, by sneaking in and creating system vulnerabilities, which can be exploited without the users’ knowledge.
- Espionage – Hackers with malicious intentions can use a variety of spying methods on your computer with the help of the Trojan infection. The criminals can obtain any type of data they want, including your passwords, credit and debit card details, internet account details, and even your keystrokes. They may also gain access to your webcam, and mic, and spy on you, and your home.
- System and file destruction – An infection such as Only Application can also be used to mess with your system, destroy information on your hard drive, or even crash your entire operating system. That’s why it is very important to remove the infection as quickly as possible before it manages to cause any serious and irreversible harm.
How can your system be protected?
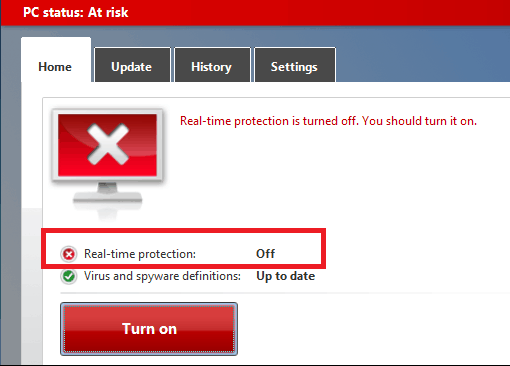
Make sure you update your system frequently to protect it from the latest viruses, and install the latest security patches to eliminate system vulnerabilities that Trojans like Only Application, or other malware can exploit. Also, try to avoid shady or illegal websites, spam emails, suspicious advertisements, and links from unknown senders, as you never know where they may redirect you to. Still, remember that the Trojans can be very stealthy, and that’s why, for optimal protection, it is best to invest in reliable security software. If you’ve been infected with Only Application, the removal guide below will help you clean up your system, but in case you face any trouble, do not hesitate to use the professional removal tool attached to it.
SUMMARY:
| Name | Only Application |
| Type | Trojan |
| Detection Tool |
Only Application Virus Uninstall
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment