*Oodt is a variant of Stop/DJVU. Source of claim SH can remove it.
Oodt
Oodt is an advanced file-encrypting Ransomware virus designed to force its users to release a ransom payment by locking up their files. Oodt initially infects the computer and encrypts the user files without any obvious symptoms, and then generates a ransom-demanding text file.
Unfortunately, a typical trait of most Ransomware threats is that they are able to stay undetected during the process of encrypting the files of their victims. This means that, if a Ransomware like Oodt infects you, it will most probably succeed in encrypting your data, and you won’t be able to notice that until it’s too late to intercept the process. There are some subtle symptoms that the most vigilant and lucky of users may notice, but this rarely happens. For instance, when the Ransomware is locking up user data, it actually creates encrypted copies of the targeted files and then deletes the original data, so, technically, once the virus completes its job, it leaves you with identical copies of your files, which copies, however, are encrypted. This is important because, during the time both the copies and the original files are present on your PC, you may notice that there’s less free storage space on the computer than usual and that can tip you off to the Ransomware’s presence. Additional potential symptoms are an unusual increase in the RAM and CPU consumption because the Ransomware requires some system resources to perform the encryption.
It must be said, though, that none of those symptoms are typically particularly visible, and it’s very rare for the victim to notice them in time to do anything about the ongoing encryption process.
The Oodt virus
The Oodt Virus is a Ransomware threat known for its use of AES-256 encryption that can lock all important data on your PC and keep it unavailable until a ransom is paid. The Oodt Virus is usually distributed with the help of stealthy Trojan backdoors.
The best you could against any Ransomware virus (or any piece of malware for that matter) is to simply prevent it from entering your system. Though there are many distribution channels used by Ransomware threats like Oodt, one of the most commonly used ones in recent years is to first infect the victim’s system with a Trojan Horse backdoor, which can then secretly download the Ransomware onto the targeted machine. Trojans are usually disguised as seemingly safe free programs that get uploaded on file-sharing platforms with low-security standards or get distributed via spam online messages. Therefore, to prevent future attacks from backdoor Trojans and Ransomware threats, we strongly recommend that you never download anything from questionable sources or click on any sketchy links present in suspicious online messages you may receive.
Of course, since you are here, we assume that you’ve already been attacked by Oodt and are now looking for a way to fight this infection and recover your files. Below, we will address the options you have and tell you which one we think may be the best for you.
The Oodt file extension
The Oodt extension is a custom file extension placed at the end of the name of each file encrypted by the Ransomware. The Oodt extension can’t be read by any software and keeps the encrypted files inaccessible until the corresponding decryption key is applied.

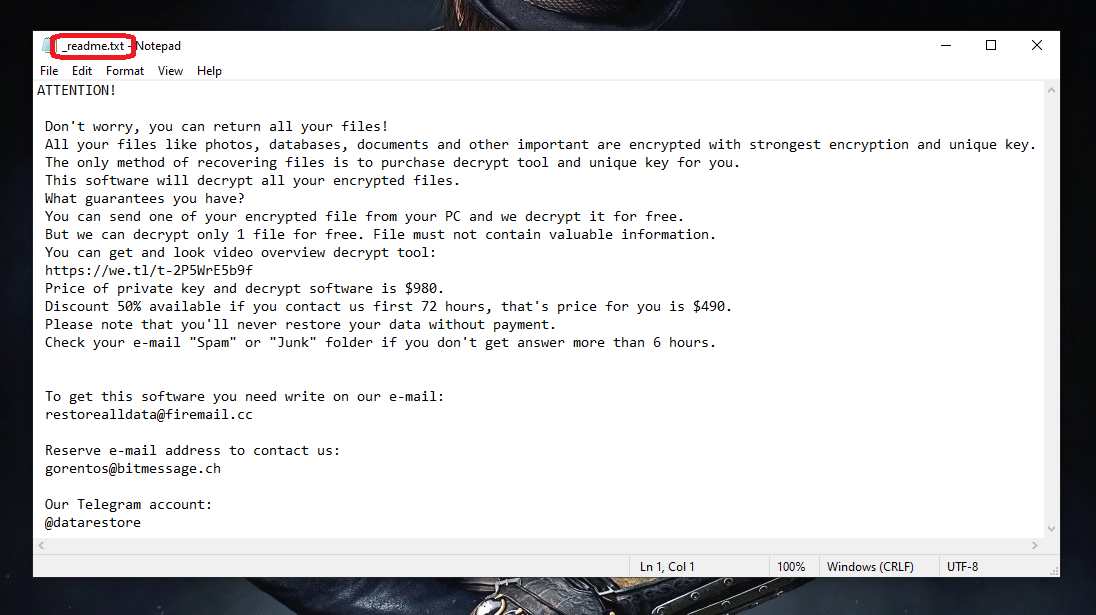
If Oodt has already encrypted your files, chances are you have seen its ransom-demanding message that it has created on your computer in the form of a readme.txt file. If that’s the case, you should already be aware that the hackers want you to pay them a certain amount of money in exchange for the private decryption key that can (supposedly) set your files free. There are two main reasons why we believe it’s best to not go for that option.
The first one is that you obviously cannot trust the hackers – for all you know, they could choose to never give you the key yet keep the ransom money you send them.
The second reason is that, even if everything works out as intended, you get the key, and recover your files, this will still not get rid of the malware on your computer and this may be a problem in the future.
With those two factors in mind, we strongly recommend that you first use the removal guide below and the How to Decrypt Ransomware article linked in and try to delete the virus and recover your data with their help, rather than interacting with the hackers and risking your money.
SUMMARY:
| Name | Oodt |
| Type | Ransomware |
| Detection Tool |
*Oodt is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Oodt Ransomware
To remove Oodt, first, delete any recently installed programs that may be responsible for the infection, then kill the Ransomware processes, and restore the changed system settings.
- You can search for rogue programs and uninstall them from the Uninstall a Program list in the Control Panel.
- All currently running processes are shown in the Task Manager, so o to it and quit anything you think may be harmful.
- Visit the System Registry, the Hosts file, and the list of Startup Items and delete/disable in them anything introduced by the virus.
- To remove Oodt, one last thing you must do is clean the AppData, LocalAppData, ProgramData, WinDir, and Temp folders from rogue data.
The steps listed above only outline the removal process – for more details and bonus tips, please, read the entire guide shown below.
Detailed Guide

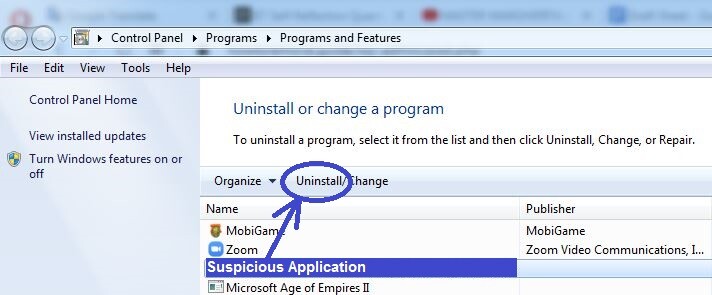
As we said, the first important step is to ensure that there aren’t any unwanted or malicious programs on your computer. All programs that you have knowingly or unknowingly installed on your PC can be seen in a list located in the Control Panel, so open the Start Menu and then click on the Control Panel icon. If you don’t see it there, simply type Control Panel in the search bar of the Start Menu and it will appear.
Once you open the Control Panel, locate and click on the Uninstall a Program button, and this will take you to the list of programs we mentioned. Here, you must use your own judgment to figure out if any of the listed items may be harmful and related to Oodt. It may help you if you look at the installation dates because, more than likely, if the program that infected you with Oodt is there, its installation date would be not long before the Ransomware encrypted your files. Also, needless to say, any other programs that seem unfamiliar, suspicious, and unneeded can also be regarded as potential “suspects”.
If you think you’ve found a program that should be removed, select it, select Uninstall (the button at the top), and complete the uninstallation process by following the on-screen steps. Make sure that you don’t allow anything related to the program to be allowed to stay on your PC.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Oodt is a variant of Stop/DJVU. Source of claim SH can remove it.
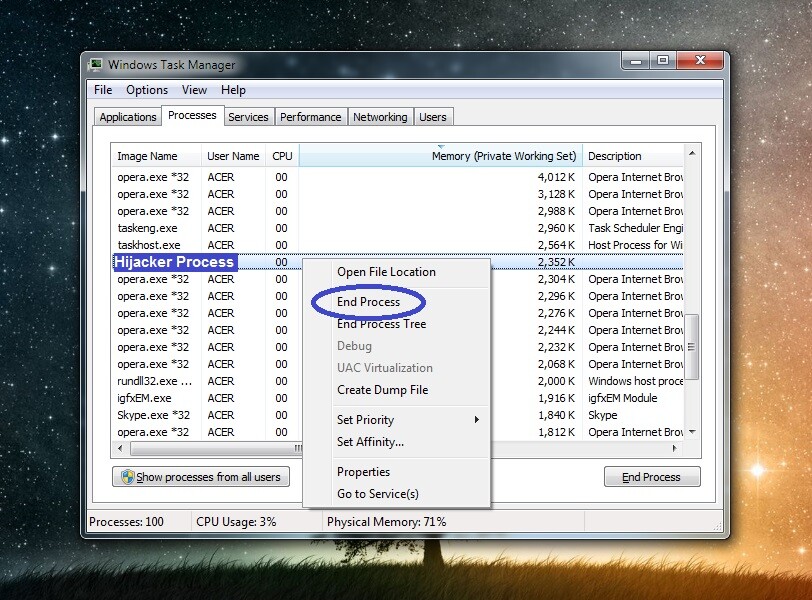
Now press together Ctrl, Shift, and Esc to start the Task Manager tool and check its Processes tab for any rogue processes. Here, yet again, you must use your judgment to figure out which process may be malicious. We suggest that you sort the items by the amount of virtual memory or processing power (CPU) that they are consuming so that the most resource-intensive ones would get grouped together. Then focus on those most resource-intensive processes, because most Ransomware threats require sizeable amounts of system resources to operate.
Obviously, it’s unlikely that there would be a process named Oodt, but if there are any items with unusual or unfamiliar names, it can greatly help you if you looked them up. If the process(es) you deem questionable is indeed related to Oodt, the chances of finding information on the Internet that confirms it is very high. If you do come across any such information during your online research, then what you must do next is go to the File Location folder of the process by right-clicking on the process’ entry in the Task Manager, and then select the first option from the menu.
Following that, once you are at the File Location folder, make sure to scan each of the files there with the powerful free malware-scanner available right below (it requires no installation and can be used directly from this page).


The first thing you should do if malware gets detected is Quit the harmful process – simply right-click it again and select the End Process button. Next, make sure that everything in its folder (including the files that didn’t get flagged as malicious) gets deleted. If you are not currently able to eliminate one or more of the files, leave them for now and focus on the next steps. Later, when you are finished with the entire guide, go once more to the File Location folder of the rogue process and delete it.
Note: If none of the scanned files got detected as malicious, but experts online are certain that the suspicious process you saw in the Task Manager is malicious, do not hesitate to quit it and remove all data related to it.

To ensure that the Oodt Ransomware doesn’t try to run its process or processes again, you must get your system into Safe Mode before you proceed to the next steps.

*Oodt is a variant of Stop/DJVU. Source of claim SH can remove it.
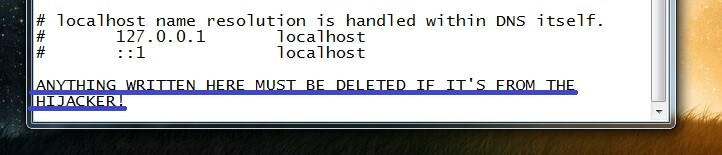
Now you must check the list of Startup items and the Hosts file of your system for changes made by the Ransomware and revert such changes.
Start by clicking the Start Menu, typing in it msconfig, and opening the first result that appears. You will see a window labeled System Configuration on your screen – you must go to its Startup tab. There, look through the listed apps, programs, and services, and if any of them appears unfamiliar or suspicious, uncheck them, and then select OK.
Next, select the Start Menu again and this type copy-paste in its search bar the following file location:
- notepad %windir%/system32/Drivers/etc/hosts
Press Enter to go to the specified file (Hosts) and when it opens, copy any text that may be written in it under “Localhost”. Then paste the copied text in the comments below this article and wait for our reply, in which we will tell you if anything needs to be done about the Hosts file. If there was no text below “Localhost”, simply go to the next steps.

Warning!: While searching for malware items in the Registry and deleting them, make sure that you only delete those items that you are certain are from Oodt. If you come across anything that you think should be deleted but aren’t sure, ask us in the comments about it. It’s very important to not delete Registry items that aren’t from the virus because doing so may cause system damage.
Start by typing Run in the Start Menu, then open the first shown item, type in the newly-appeared window regedit, and hit Enter. If you get asked for permission before you can open the Registry Editor, click on Yes.
Select the Edit menu in the Registry Editor, go to Find, and type Oodt in the search bar. Press Enter to begin the search, but know that even if there are multiple items related to the virus, the search will only show the first one of them, so delete whatever item gets found, and then search again.
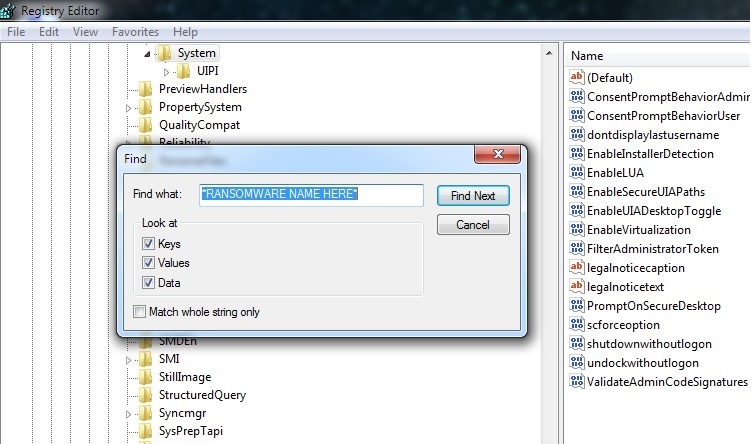
Do not stop doing this until all Oodt items are gone from the Registry and there are no more results when you search for the Ransomware’s name.
After that, manually find the following locations in the left panel of the Registry.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
Since you’ve deleted all Oodt items, do not expect to find anything with that name in those locations. Instead, be on the lookout for items with names that look random and out of place, such as, for example, “2398tu248j398rh983ur09tug389r“. Any items that have a name similar to that should be deleted (but it’s still better to first ask us about them in the comments).

For the final step, copy the next lines (one by one), place them in the search field below the Start Menu, and hit the Enter key after each to open the folders that they correspond to.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
All files that are in the Temp folder must be deleted from it. As for the other folders, delete only the files that have been created since the Oodt virus infected your PC.
If Oodt is still in the system
There could be many reasons for Oodt still being on your computer even after correctly completing these steps. In case you are still noticing the presence of the virus, the best advice we could give you is to either use a professional removal tool that can take care of the virus for you or bring the PC to a specialist.
As we told you earlier, in the article, a lot of Ransomware threats are helped by Trojans that can make the manual removal of the Ransomware virtually impossible (or at least way too difficult for anyone who’s not an expert). Therefore, we’ve also included on this page a powerful tool that can help you clean your entire system from rogue software, including the Ransomware virus as well as any other threats that may be hiding on the computer.
How to Decrypt Oodt files
To decrypt Oodt files, you first need to make sure that all malware data is gone from your PC. Then you should try the methods shown on our separate decryption guide, where you would hopefully find one that will let you decrypt Oodt files.
Before you try to get your files back, you must be certain that your system no longer has any malware on it. If you need to, use the free scanner from our site to test suspicious files for harmful code and delete anything that gets flagged as malicious.
Once you are sure your computer is clean, proceed to the instructions shown in our How to Decrypt Ransomware post. It’s important to understand that the removal of Oodt doesn’t free the files that it has infected, so you’d still need to find a way to free your files. We already mentioned why we consider the ransom payment to be a bad course of action, and it is why we’ve done our best to provide you with the most effective alternative recovery methods that we’ve been able to find in the article linked above.
Oodt is a PC virus that will lock all files in your system by applying encryption to them. Oodt will release the files only if you “purchase” a decryption key from the hackers behind this virus. If your computer has been invaded by this new Ransomware virus, you have probably noticed that you cannot open most of the files located there and that those files’ extensions have been replaced with some strange and unfamiliar ones. What this means is the Oodt virus has succeeded in encrypting your data, and the affected files cannot be opened without a special key. It is likely that you have already received a message on your screen from the hackers behind this virus, in which message you are given instructions with regard to a ransom payment that you are supposed to carry out. The creators of such crypto viruses promise their victims that the unique key that can unlock the files would be sent to them once they finish the payment.
The Oodt virus is a piece of malware capable of blocking access to valuable data in your computer and then asking you to pay a ransom. The Oodt virus belongs to the Ransomware category of computer threats. If the data Oodt has locked is very important to you, you might indeed be willing to go for the payment, even if the required sum is high. However, we must warn you that this might not go the way you’d expect it to. The hackers might refuse to provide you with a key even after you give them your money, in which case you’d be unable to do anything about it – your money would be gone, and your files would still be in their inaccessible state. This is why the preferable course of action here is to first try to deal with this situation on your own, without interacting with the hackers in any way. The guide on this page is supposed to help you ameliorate your current situation, and minimize the unpleasant consequences.
The Oodt file extension is a suffix placed at the end of your files’ names that replaces the regular ones. The Oodt file extension is part of the reason you can’t open your data after the encryption. If you decide to try some of the alternatives, it is important to first liberate your computer from the Ransomware’s presence. The first part of our guide focuses on the removal of Oodt and Pcqq, and we advise you carefully follow the steps in there in order to remove the infection. The encryption on your files won’t go away with the removal of the cryptovirus, but it is essential to have a computer clean of malware in order to try any of the recovery alternatives. Also, if you don’t eliminate the Ransomware, it might lock new files that you create in your computer.
As far as the alternative recovery options are concerned, undoubtedly the best one is if you have a full file backup on an external device or on a cloud. If you have some form of backup device, make sure you only connect it to your computer once the malware is no longer present in the system. Otherwise, the virus will probably lock your backup files as well. Sadly, most people don’t have exhaustive backups, so they need to try other methods to restore some of their data. We have included some potential recovery methods in the file-restoration part of the guide, and we advise you to have a look at them. We cannot give you promises about their effectiveness, but its still important to try them as this might help you get at least some of your files recovered.
The Decryption of the files encrypted by Oodt may be a lengthy process but this should not discourage you to try every available option. You can start with our comprehensive (and daily updated) guide on file decryption that can be checked out here.
In case that this guide isn’t enough to completely rid you of the ransomware and its traces, it might be a good idea to consider downloading the professional anti-virus program we recommend and scan your infected computer with it or try our free online virus scanner.

Leave a Comment