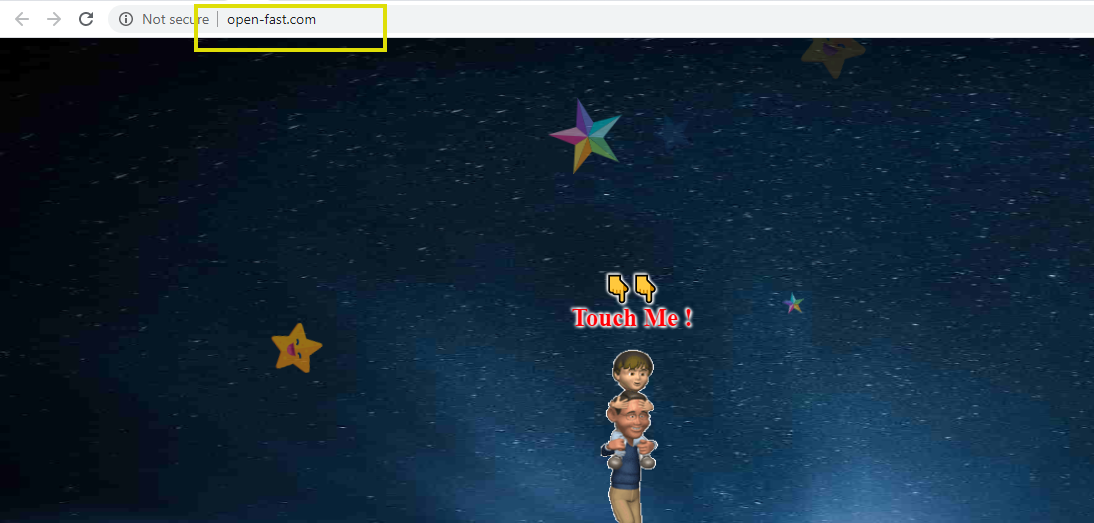
Open-fast.com
Open-fast.com belongs to the browser hijacker category and is generally considered as a potentially unwanted application. Open-fast.com is known for its ability to change the settings of any given web browser and set its own search engine and homepage.
In case of a browser hijacker attack, it’s critical that you don’t get panicked and inform yourself about the risks and the specifics of this software. The reason is, most people, when confronted with the unusual changes that take place in their Chrome, Firefox, Safari, or other web browsers, such as a new homepage, an unfamiliar search engine, or a new new-tab page address, jump to extreme conclusions, thinking they have been hit by some kind of a virus. The automatic redirects to various known and unknown web pages and the never-ending stream of pop-up ads, banners, and click prompts also don’t help the situation. That’s why we’d like to start this article by saying to all the victims of Open-fast.com that this is not a virus, a Ransomware, or some other harmful infection.
Open-fast.com 2020
This is a browser hijacker – a type of software that is fairly harmless in and of itself. However, there are still a number of reasons why you would want to remove such software from your system and this is what we will cover here. We will also give you a detailed removal guide that will walk you through the uninstallation process of Open-fast.com so that you can restore your previous browser settings and return to your normal web browsing.
What is Open-fast.com?
The Browser Hijackers like Open-fast.com are generally known as potentially unwanted programs (PUPs) and there are some significant differences between PUPs and viruses or malware. The representatives of malware categories such as Trojans, Ransomware, Spyware, Worms, etc., are able to carry out an extensive list of harmful and illegal activities once they get installed on your computer.
Those include but are not limited to data theft, file encryption, money extortion, system corruption, and more. None of this can be performed by a browser hijacker like Open-fast.com. The main reason why a browser hijacker is considered as potentially unwanted is that its actions (the browser changes, the ads-streaming, and the constant redirects mentioned above) are seen as annoying, irritating, and totally unwanted by a lot of web users.
These actions, however, are not inherently malicious and are not intended to corrupt a computer or cause harm to its users. The sole purpose of programs like Open-fast.com is to get distributed to as many computers as possible, where they can generate large quantities of pay-per-click online ads that promote a variety of products and services. To advertise more effectively, however, the browser hijackers tend to place changes not only in the main web browser’s settings but also in the system’s registry. And, in doing so, they also lower the computer’s defenses in order to make it easier for the sponsored ads and page-redirects to pop-up on your screen. But those very same ads and page redirects, once clicked upon, may land you on different unsafe Internet locations that might have malware (including threats like Trojans and Ransomware) in them. So, this should be a huge red flag for anyone who still questions whether it is a good idea to uninstall the browser hijacker from their machine and remove its browser changes.
SUMMARY:
| Name | Open-fast.com |
| Type | Browser Hijacker |
Remove Open-fast.com Virus
We are sending you to another page with a removal guide that is regularly updated to counter the latest tricks malware creators use. It will show you how to:
- Locate and clean up your phone’s apps if they are infected.
- Find browser extensions related to the threat and how to remove them.
- Ensure your passwords were not stolen or tampered with.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Leave a Reply