*Source of claim SH can remove it.
Password Stealer
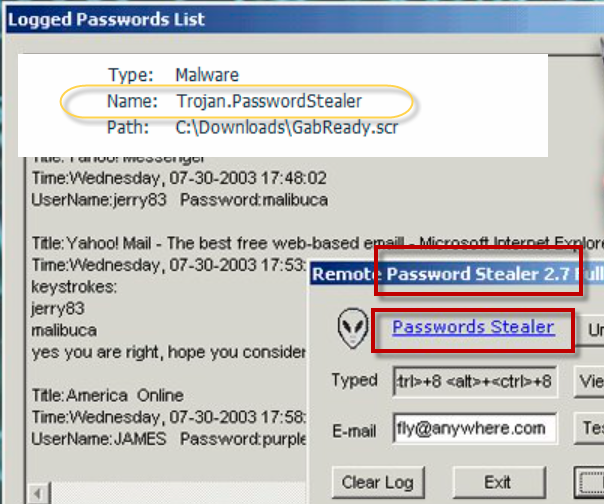
Password Stealer is a virus Trojan Horse infection that allows cyber criminals to see and record sensitive information that is found on the computer. Password Stealer may provide the hackers with full remote access to a machine and let them modify, corrupt, or delete user files.
Viruses, Ransomware, Trojans and unwanted software like adware and browser hijackers aren’t the only security hazards that you may encounter online. In many cases, there’s no need for a shady or malicious piece of software to enter your computer for you to become the victim of some insidious and nefarious cyber-criminal scheme. Sometimes, all that it takes for this to happen is that you fall for the false claims in some obscure spam phishing e-mail. And, trust us, schemes that use this type of tactics are very, very common. Thousands of web users receive fake and misleading spam messages each and every day, the sole purpose of which is to lure them or scare them into sending money to the people behind the scheme for no actual reason. If, for instance, you’ve recently received an e-mail that claims there’s a Trojan Horse infection such as Password Stealer and RegHost inside your machine that is lying dormant and would get activated in case you don’t pay a ransom to the blackmailer, your first reaction will likely be one out of the following two: you may disregard this message knowing it’s just another piece of spam or you may get intimidated and worried about the actual possibility that there may indeed be an insidious Trojan like Password Stealer within your system. In case your reaction is the latter, you may eve consider making the requested payment. Now, both options are understandable – the important thing here is to not pay the money regardless of how you feel about the unnerving message. Even if you are afraid there may be a Trojan in your computer, instead of paying the money, a much better option would be to take the matters into your own hands and try to clean your computer from any potential hidden threats. In this regard, we have added a guide for the removal of the insidious Password Stealer infection that is currently on the loose so that you can use it to ensure your machine’s safety.
Some more words about this type of nefarious e-mails schemes
Even if you have been consistently receiving such alarming and unnerving messages in your e-mail inbox, it’s all most likely nothing but a cyber-criminal scam. In nearly all instances of such spam e-mail campaigns, there’s actually no malware in the computer of the targeted users. Still, it’s important to not leave anything to chance which is why we once again advise you to not overlook the guide from this page. Password Stealer is indeed a serious software hazard of the Trojan Horse family and it’s certainly a malware program that you wouldn’t want to be present in your computer. This is why it’s still of significant importance that you make sure there is indeed nothing hidden in your system that may threaten its security. Also, for future safety, we advise you to never post your e-mail address or any other contact info about you on sites and pages that may be sketchy or unreliable as this makes it more likely for dishonest people to abuse this information and harass you in various ways.
SUMMARY:
| Name | Password Stealer |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Remove Password Stealer Malware
If you are looking for a way to remove Password Stealer you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for Password Stealer and any other unfamiliar programs.
- Uninstall Password Stealer as well as other suspicious programs.
Note that this might not get rid of Password Stealer completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


*Source of claim SH can remove it.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment